Microsoft 365 High-level deployment settings check List for Architects and Optimization teams: It covers many topics and requires extensive knowledge of various technologies before configuring them. Please do the appropriate research before changing any settings in a production tenant. It also requires multiple licenses to utilize some of the features part of the deployment settings.
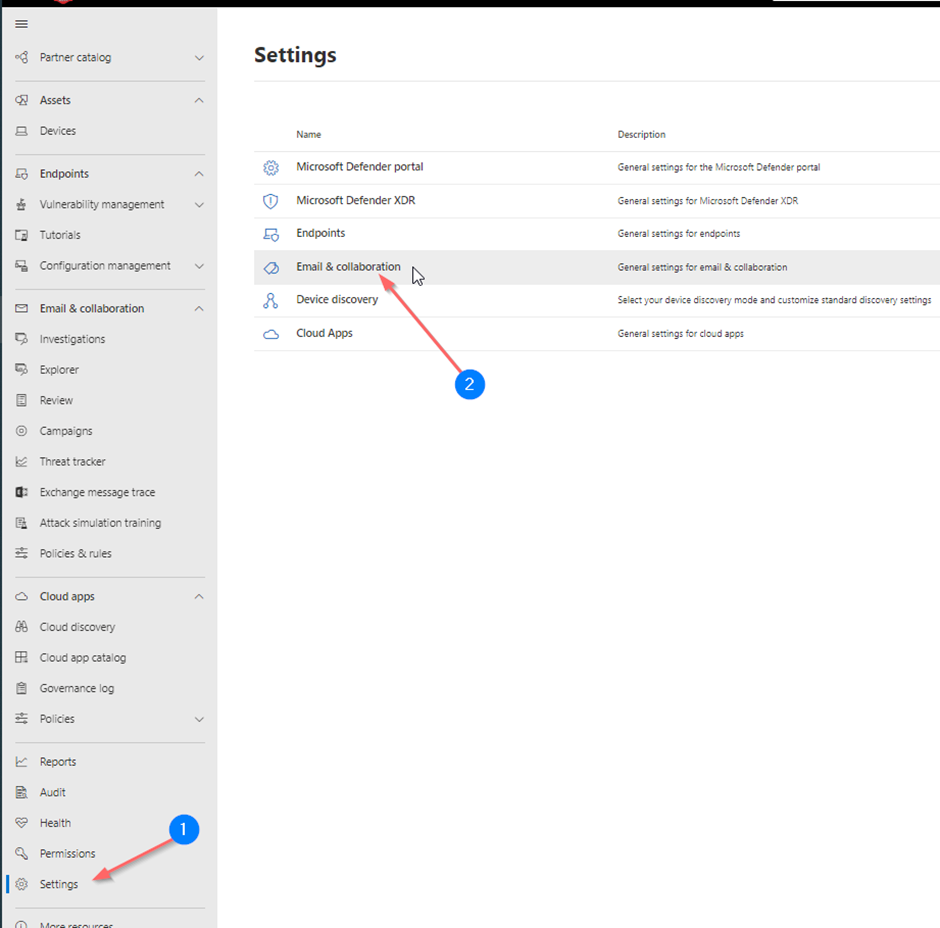
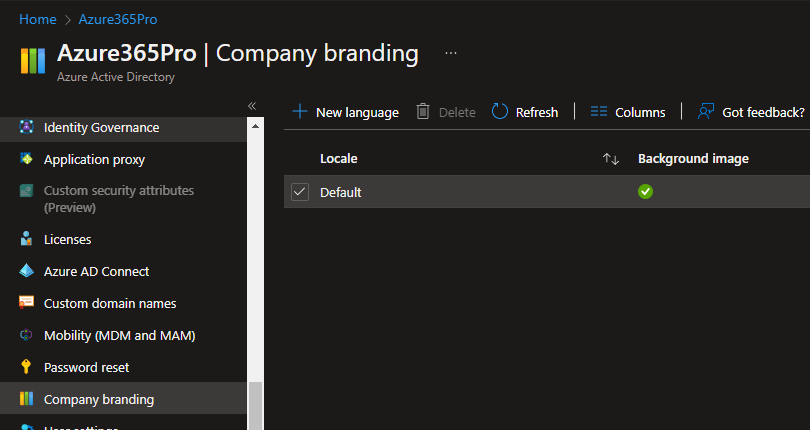
- Microsoft 365 Login Page Branding – In Azure Portal
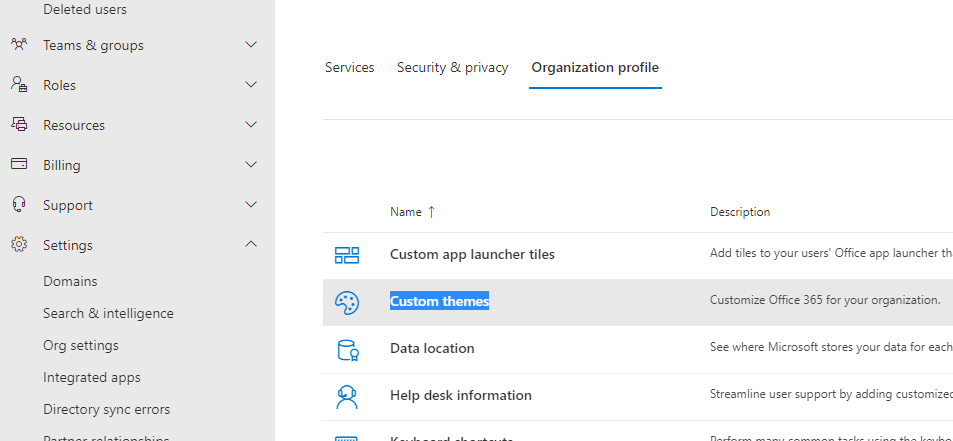
- Microsoft 365 Organization Profile Branding – In Admin Microsoft Portal
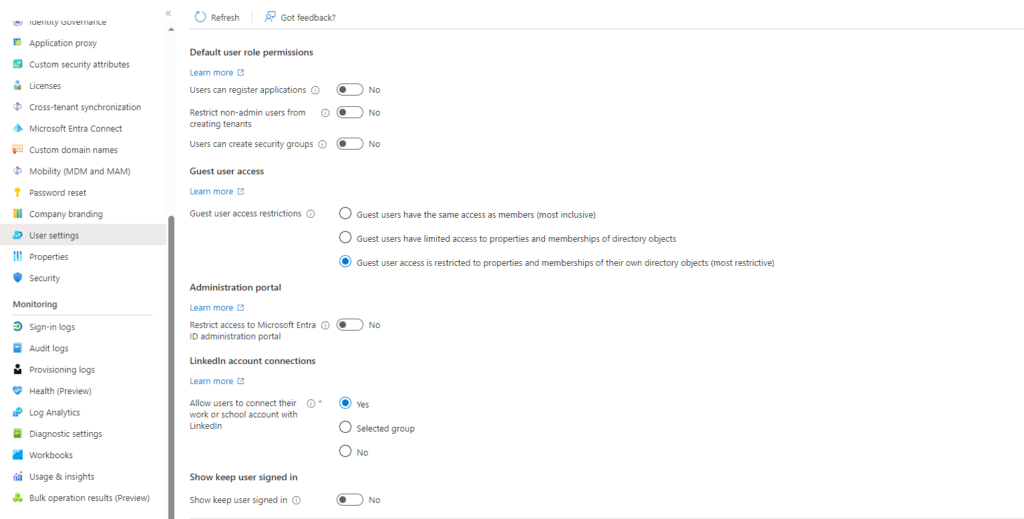
- Restricting Users from creating Azure AD Tenants
- Manage legacy MFA Migration
- Enable Multifactor authentication registration policy
- Restricting users from joining their Personal Devices (BYOD Devices) to Azure AD (Optional)
- Moving Coexistence Mode from Islands to Teams Only
- Allowing Admin Roles to Invite Guests to have SSO for External Users added to Azure AD IAM
- Enable Admin Consent Requests with Reviewers – For Application Consents
- Enabling Integration with Defender to Endpoint Manager to Test Defender Onboarding from endpoint manager
- Configure Conditional Access
- Enable Intune Advanced Features
- Configure Idle Session Timeout
- Enable Self-Service Password Reset
- Configure Authentication methods for reset
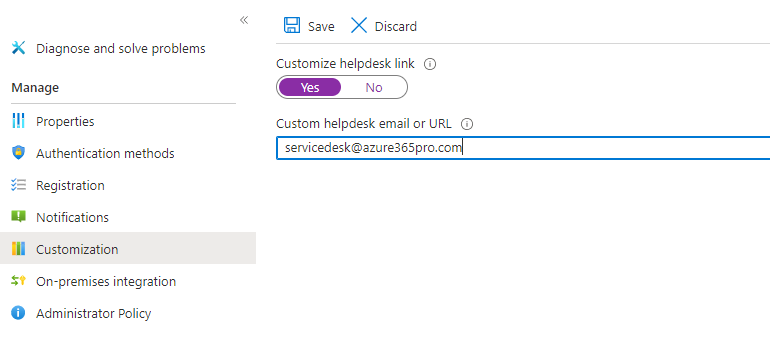
- Configure the Service Desk Link or email
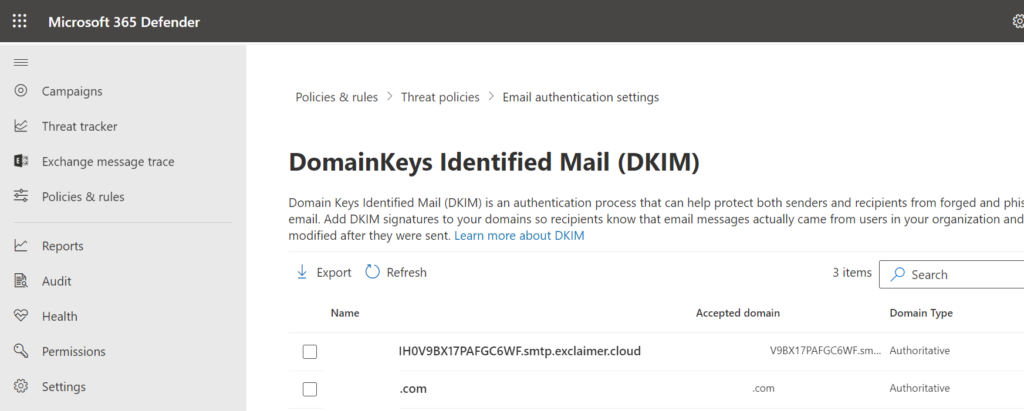
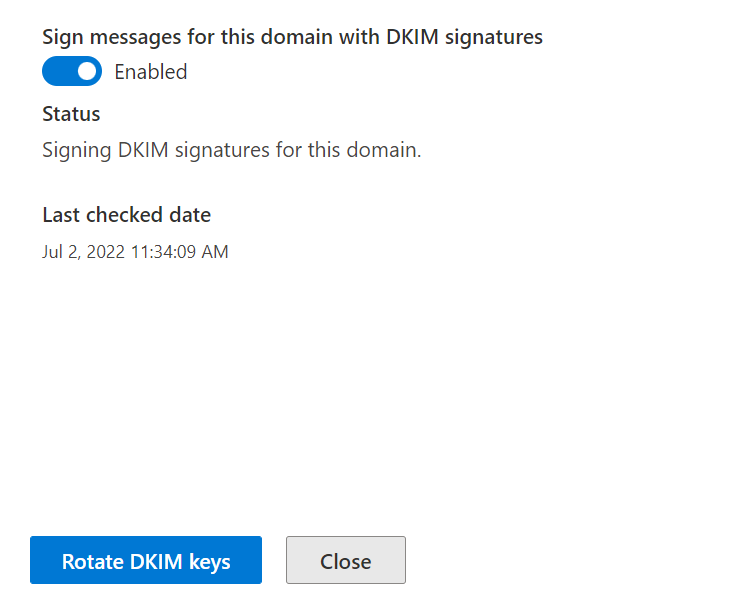
- Implement SPF / DKIM / DMARC
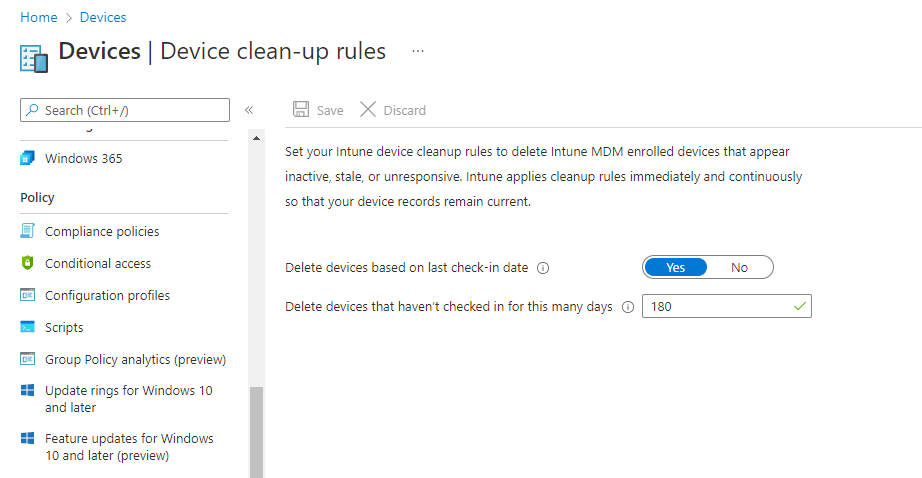
- Device Clean-Up Rules
- Use MDE (Microsoft Defender for endpoint) to enforce security configuration settings from MEM (Microsoft Endpoint Manager)
- Implementing Azure Active Directory Connect for Directory Synchronization
- Setting Deletion Threshold on Azure AD Connect
- Enable Password to write back
- Disable Teams Creation by everyone in the Tenant except specific users (Optional)
- Enable Microsoft Defender Anti Virus
- Enable Endpoint Detection and Response (EDR)
- Attack Surface Reduction Rules in MEM Endpoint Security – Azure365Pro.com
- Enable BitLocker (Device Encryption) (Optional)
- Windows Update Rings Configuration in Microsoft Endpoint Manager
- Disable Family Options UI in Microsoft Defender
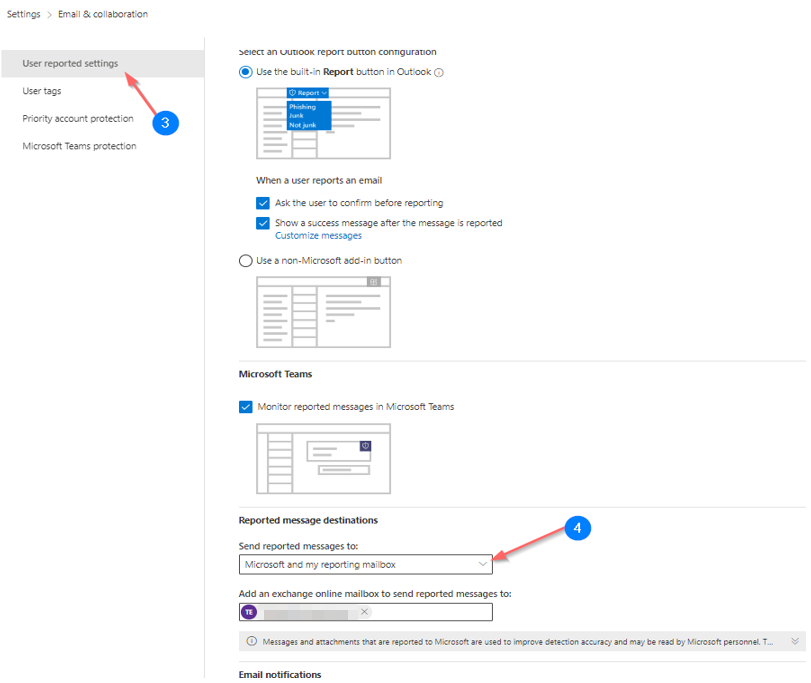
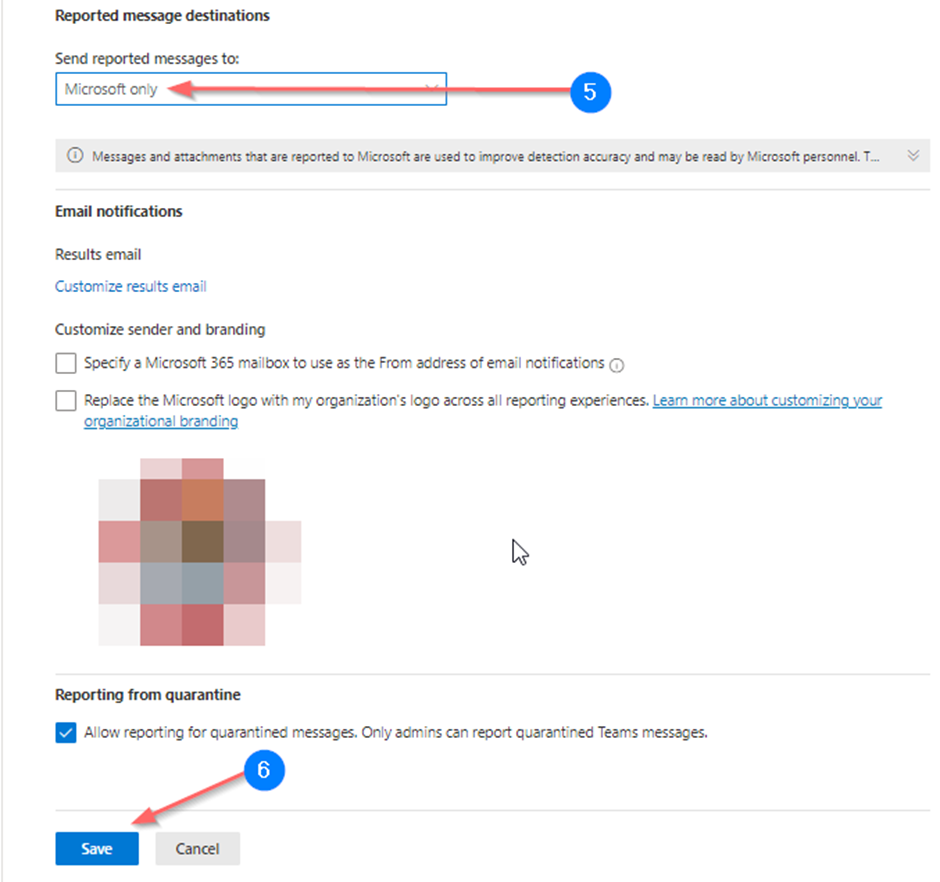
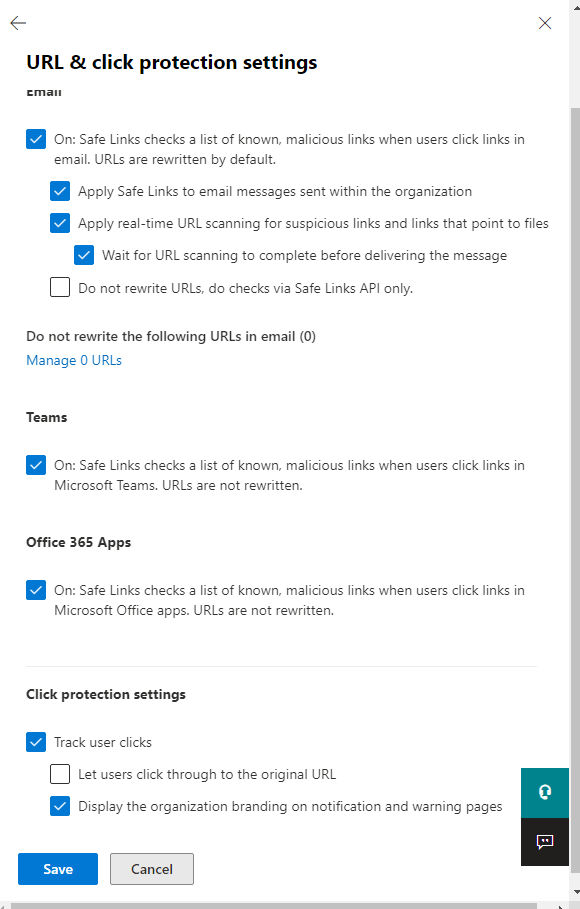
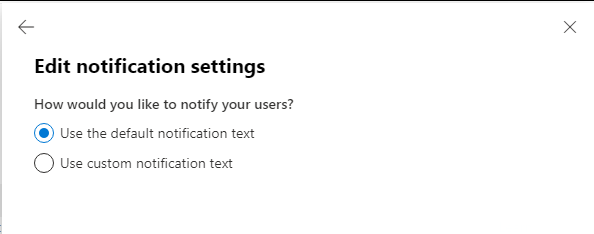
- Add Safe Links Policy
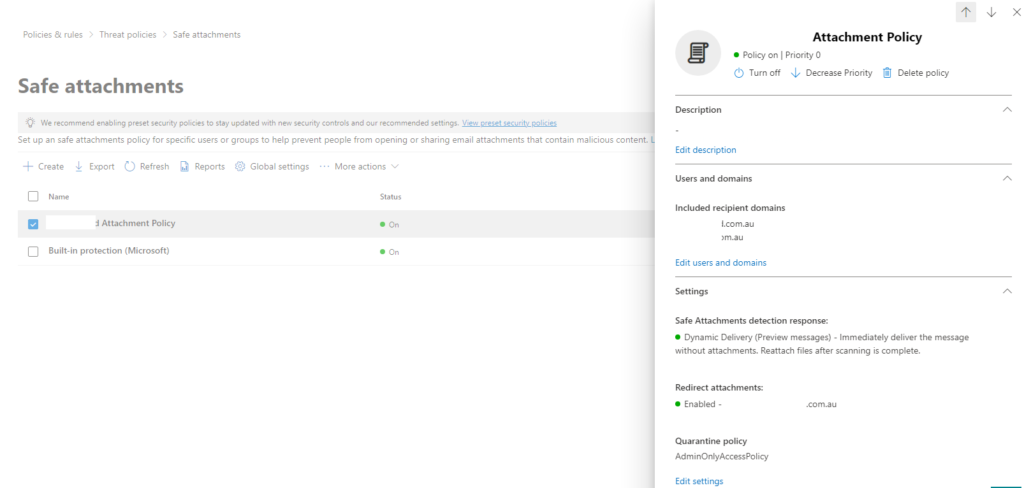
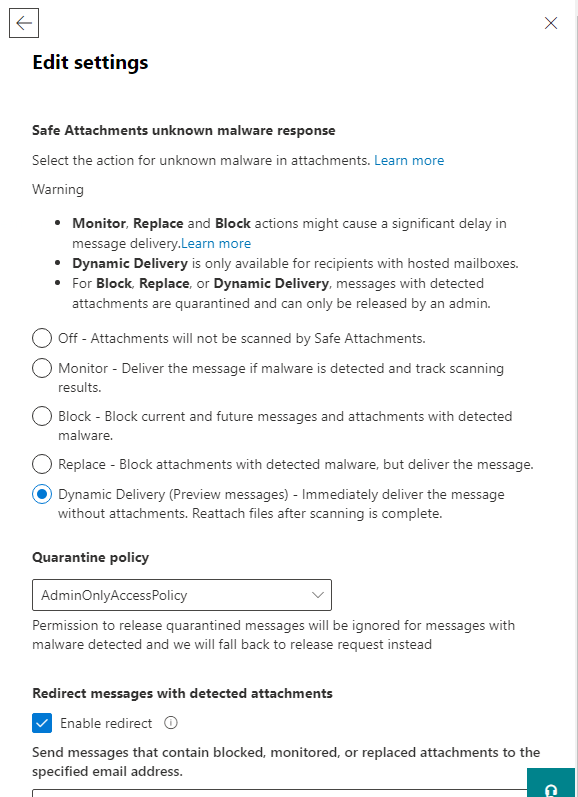
- Add Safe Attachments Policy
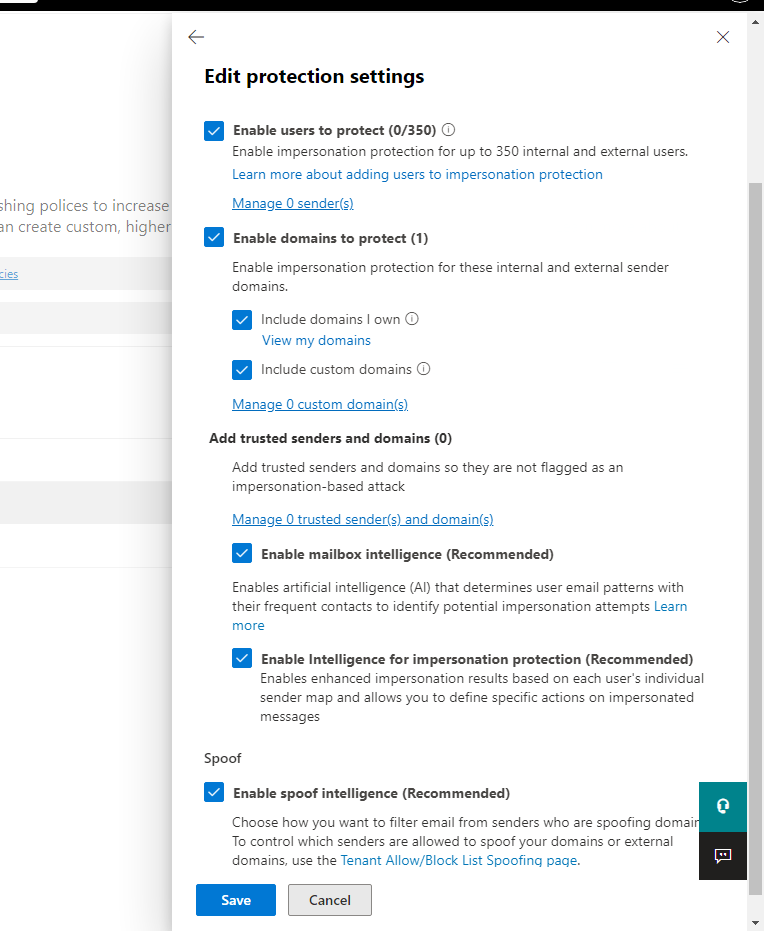
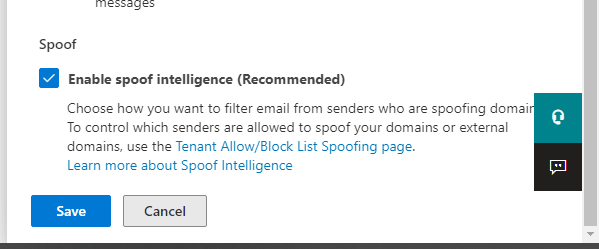
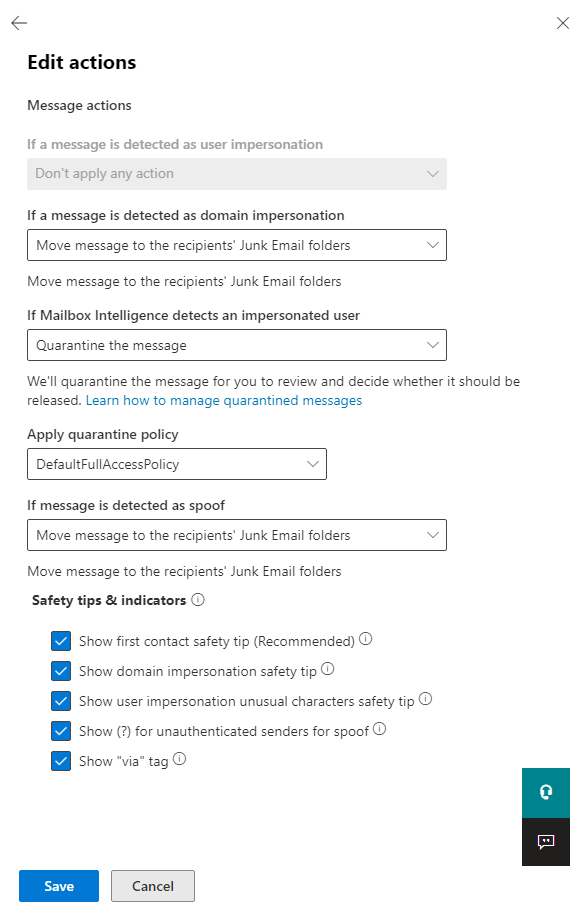
- Add Anti-phishing Policy
- Optimize Anti-Spam Policy
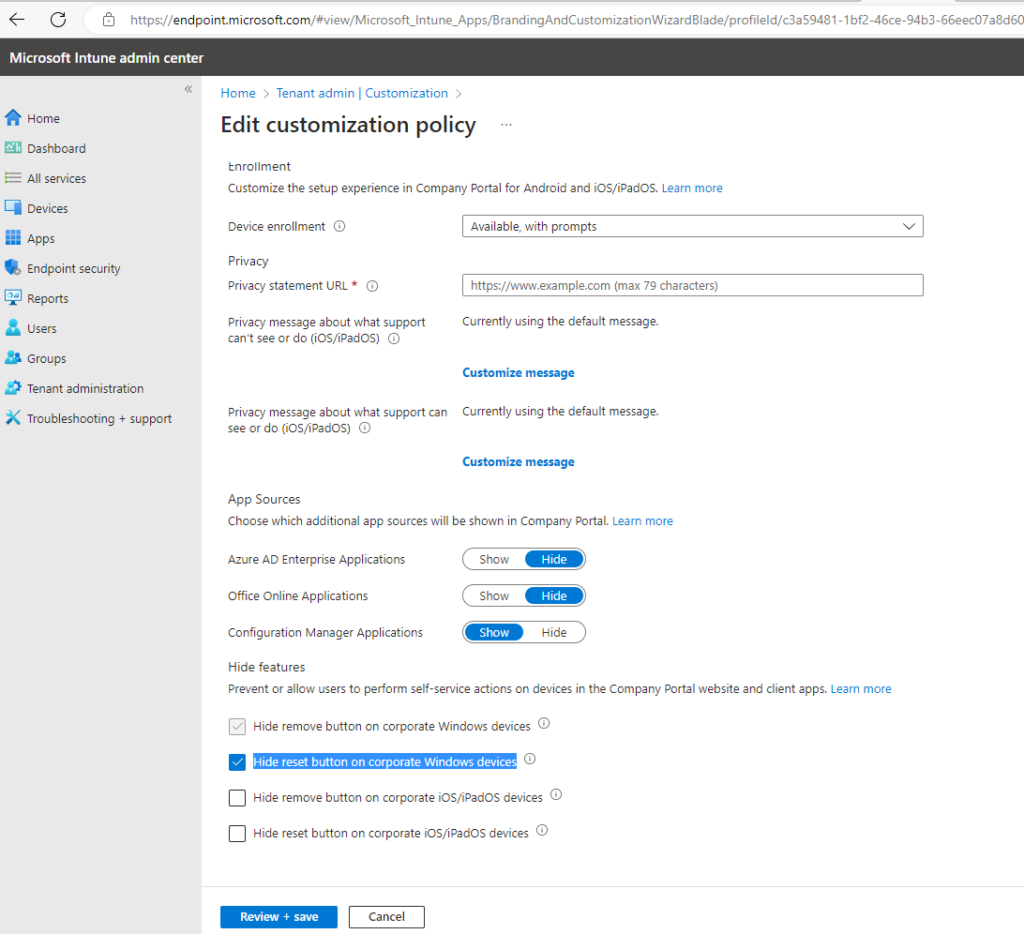
- Intune Customization Policy – Hide Reset
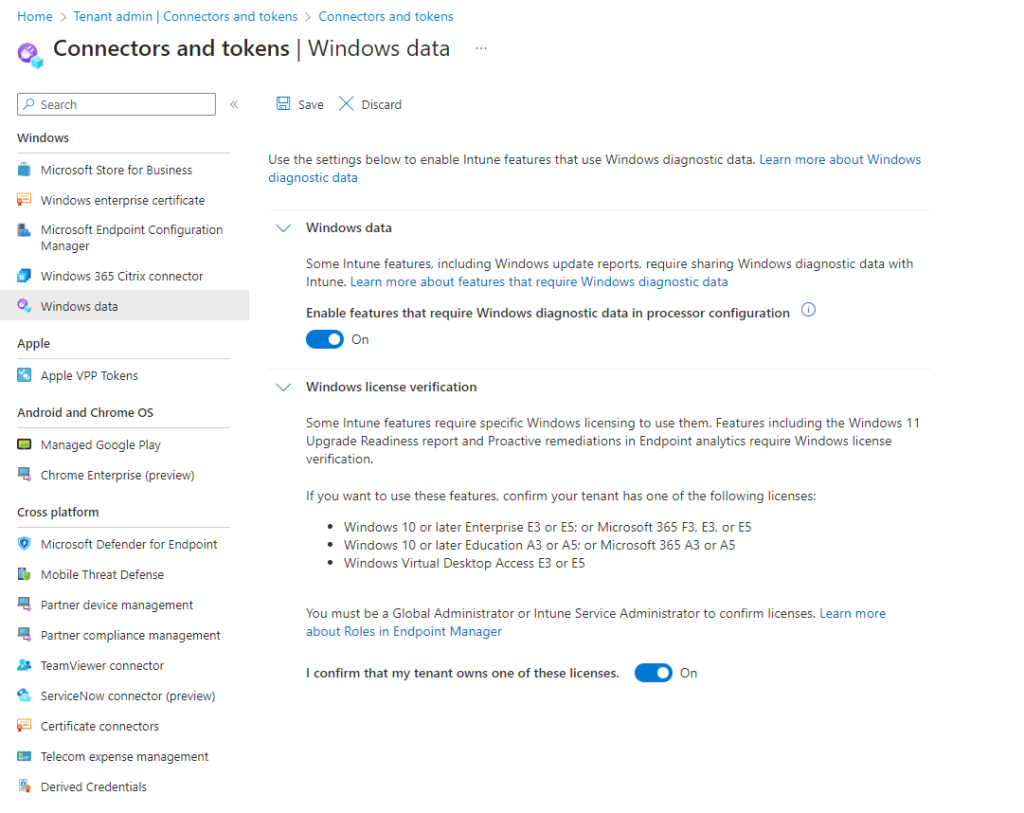
- Enable Intune to access Windows Diagnostic Data (Connectors and tokens)
- Enhancing Email Security: Tagging External Emails in Microsoft 365
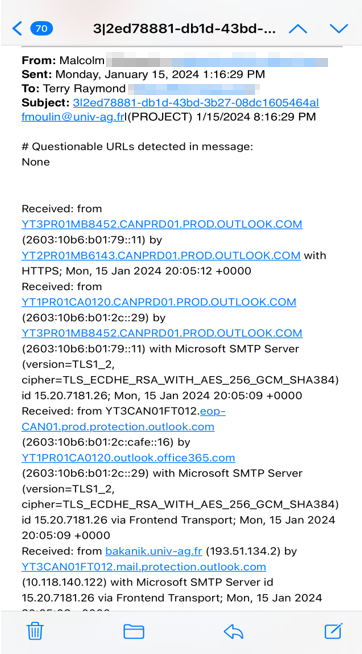
- Questionable URLs detected in message – Microsoft 365
.
- Microsoft 365 Login Page Branding – In Azure Portal
.
- Microsoft 365 Organization Profile Branding – In Admin Microsoft Portal
.
.
- Restricting Users from creating Azure AD Tenants
- Users can create Azure AD Tenants – Set to NO.
- Users can create Security Groups – Set to NO ( For Large Enterprises)
- Show keep user signed in – Set to No
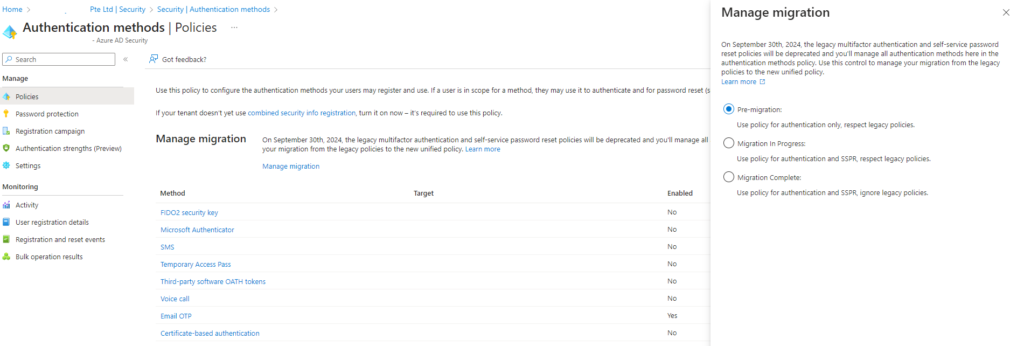
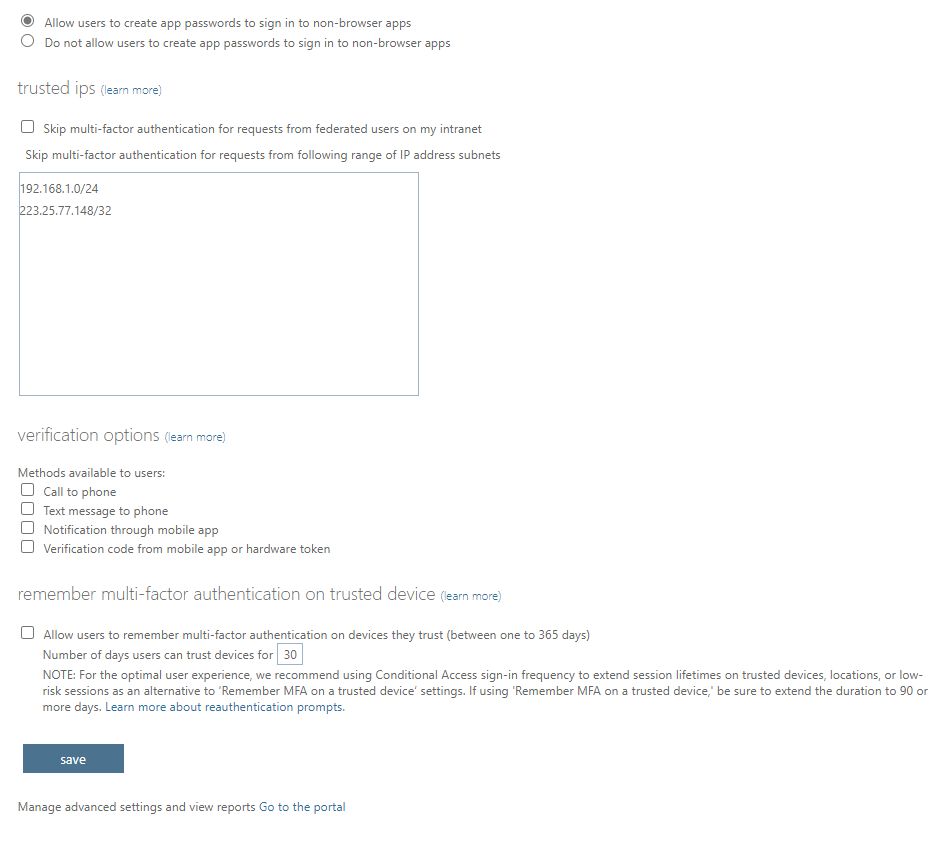
Couldn’t save new migration state: you cannot move to migration complete until disabling all methods in the legacy SSPR policy.
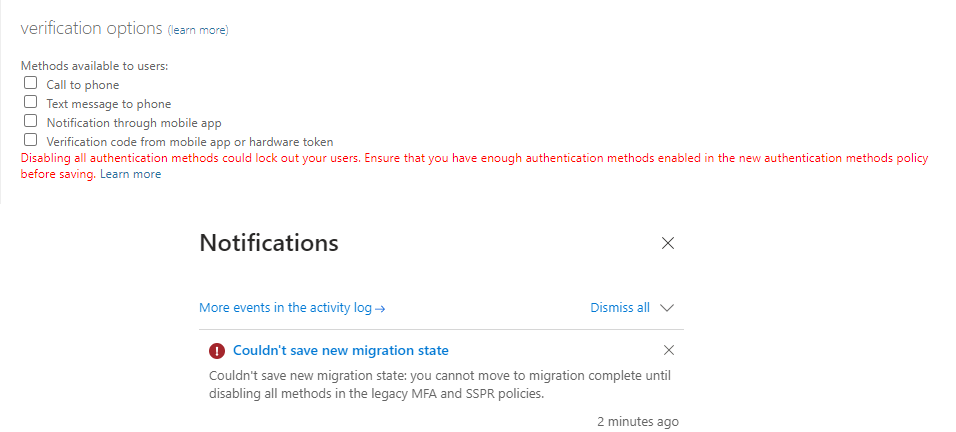
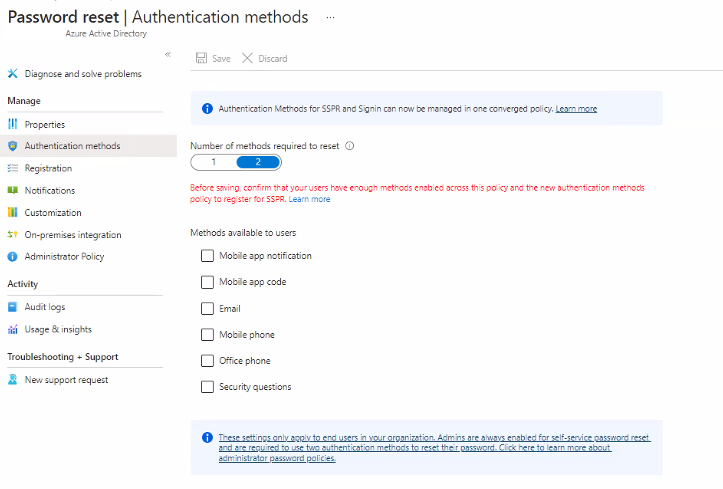
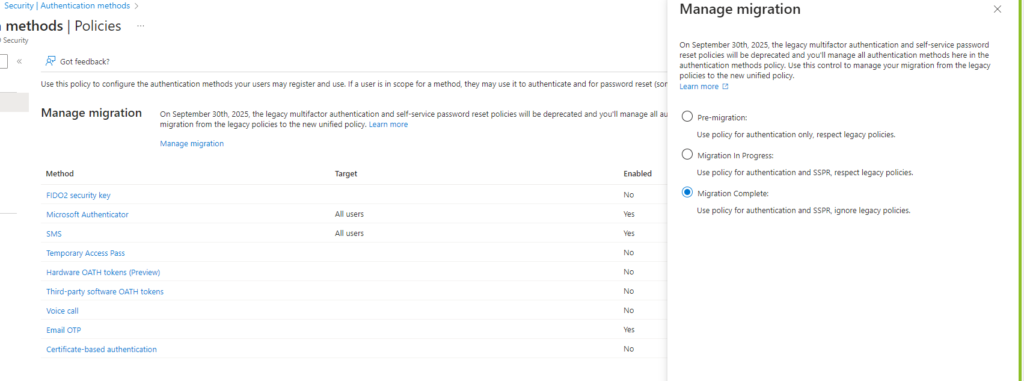
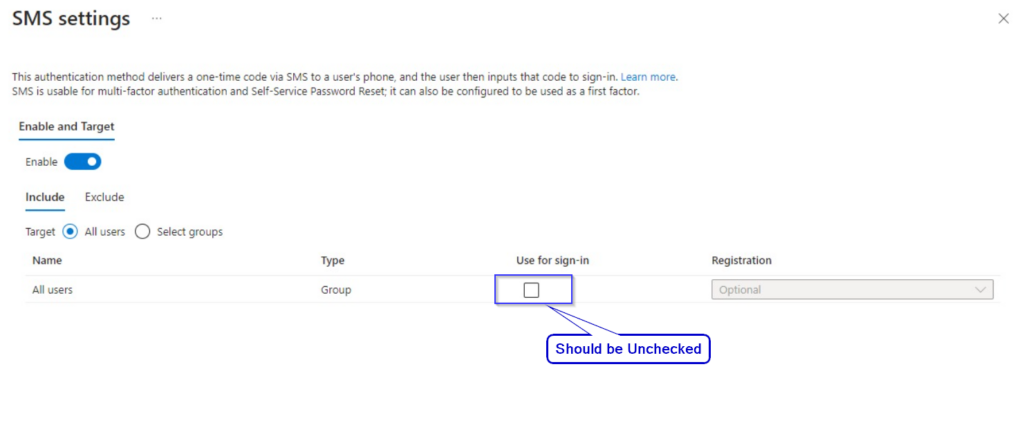
As SMS is insecure, we recommend to keep it unchecked.
.
- Enable Multifactor authentication registration policy.
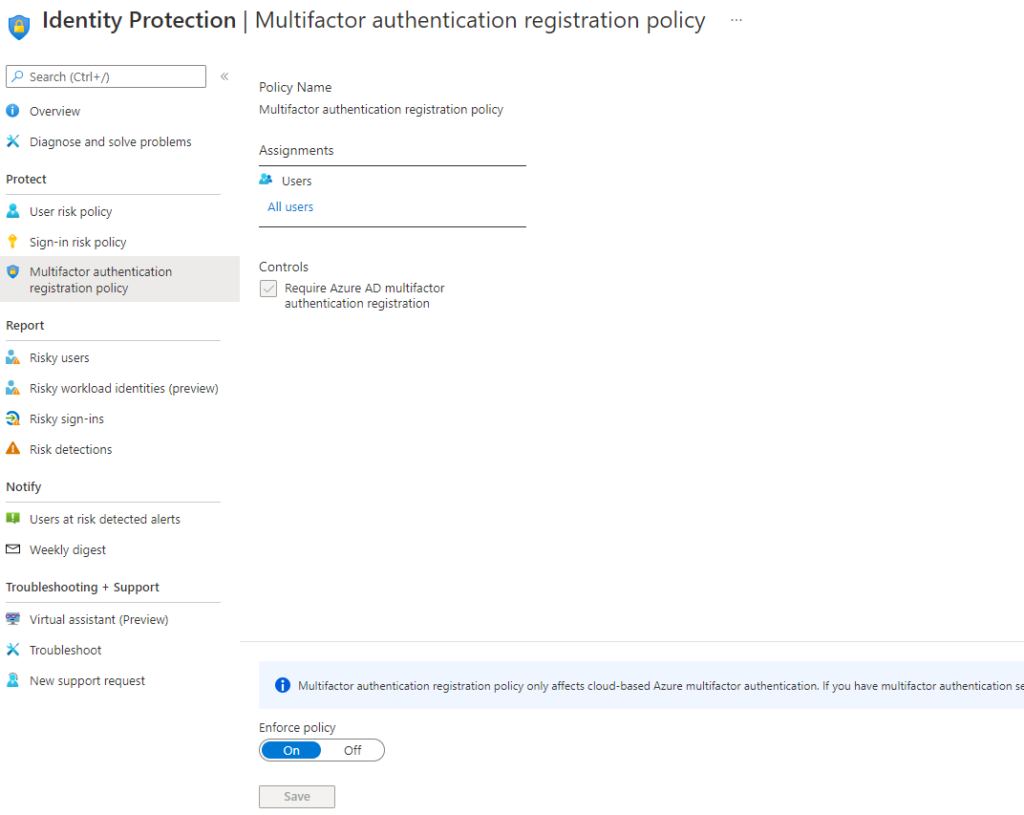
.
- Restricting users joining their Personal Devices to Azure AD
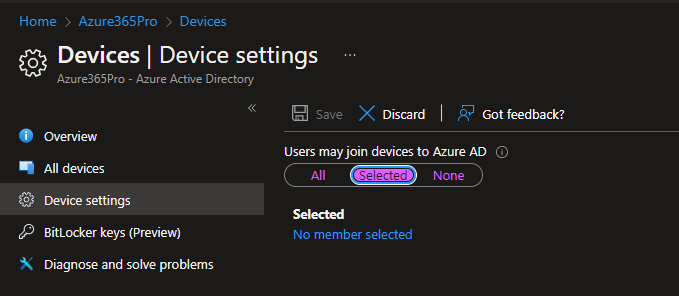
.
- Moving Coexistence Mode from Islands to Teams Only
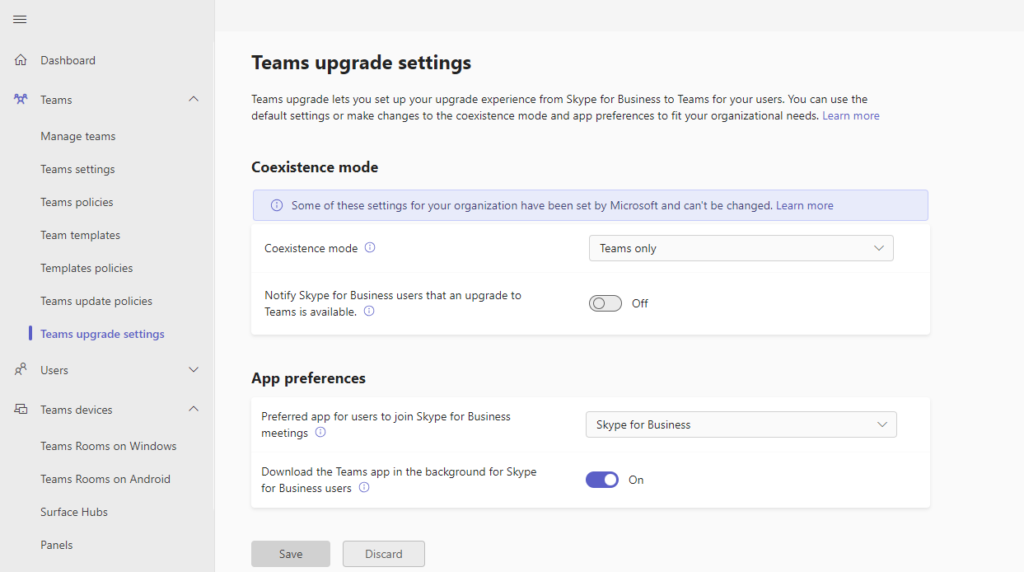
.
- Allowing Admin Roles to Invite Guests to have SSO for External Users added to Azure AD IAM
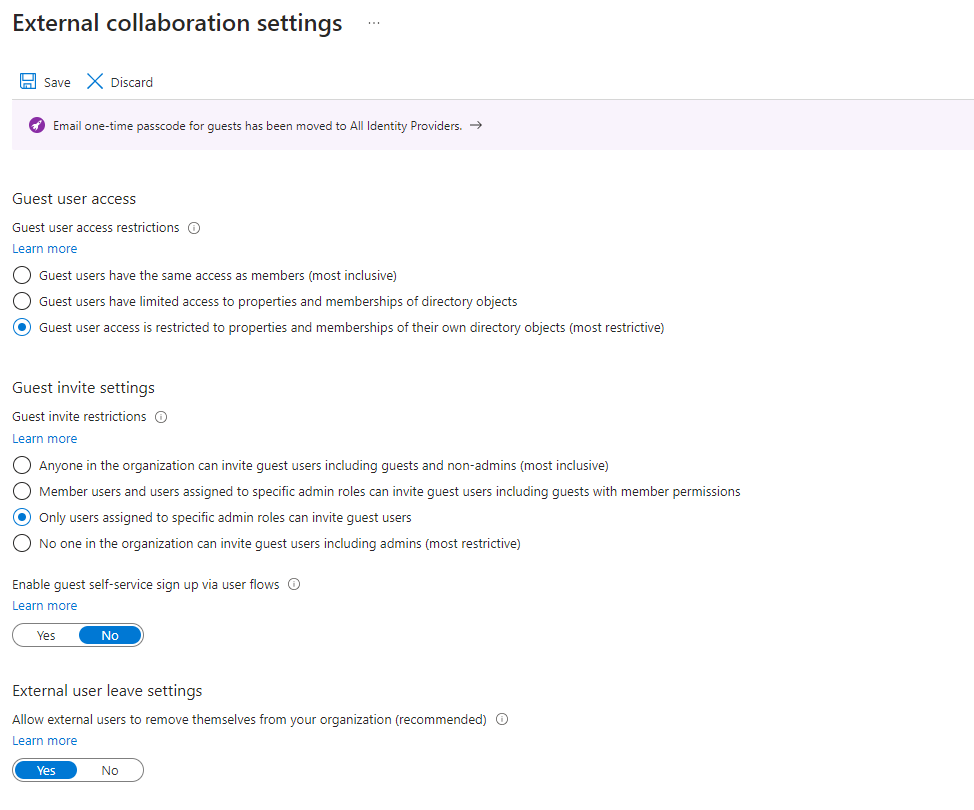
.
- Enable Admin Consent Requests with Reviewers – For Application Consents
.
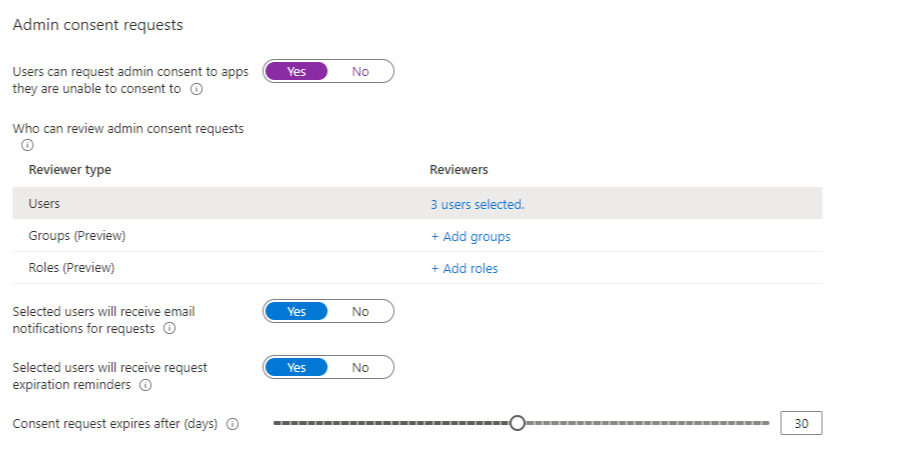
- Enabling Integration with Defender to Endpoint Manager to Test Defender Onboarding from Endpoint Manager
.
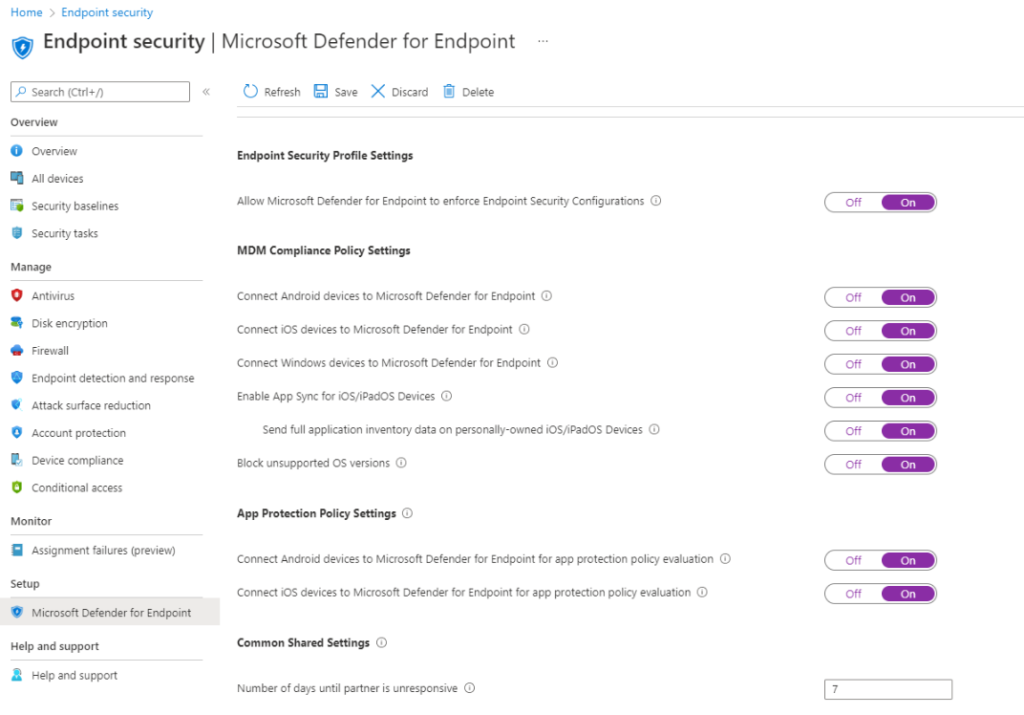
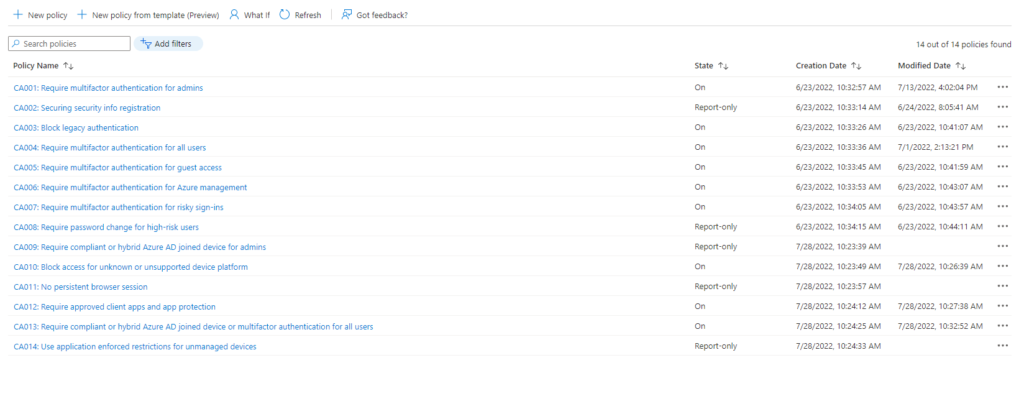
- Configure Conditional Access
- CA001: Require multifactor authentication for admins
- CA002: Securing security info registration
- CA003: Block legacy authentication
- CA004: Require multifactor authentication for all users
- CA005: Require multifactor authentication for guest access
- CA006: Require multifactor authentication for Azure management
- CA007: Require multifactor authentication for risky sign-ins
- CA008: Require password change for high-risk users
- CA009: Require compliant or hybrid Azure AD joined device for admins
- CA010: Block access for unknown or unsupported device platform
- CA011: No persistent browser session
- CA012: Require approved client apps and app protection
- CA013: Require compliant or hybrid Azure AD joined device or multifactor authentication for all users
- CA014: Use application enforced restrictions for unmanaged devices
With Devices-based Conditional Access.
.
- Enable Intune Advanced Features
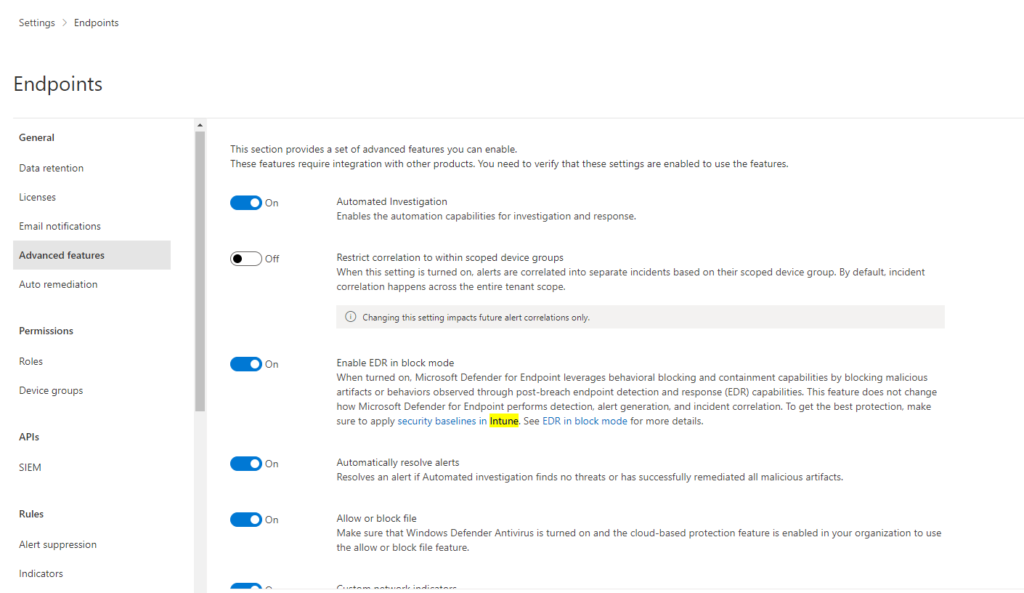
.
- Idle Session Timeout
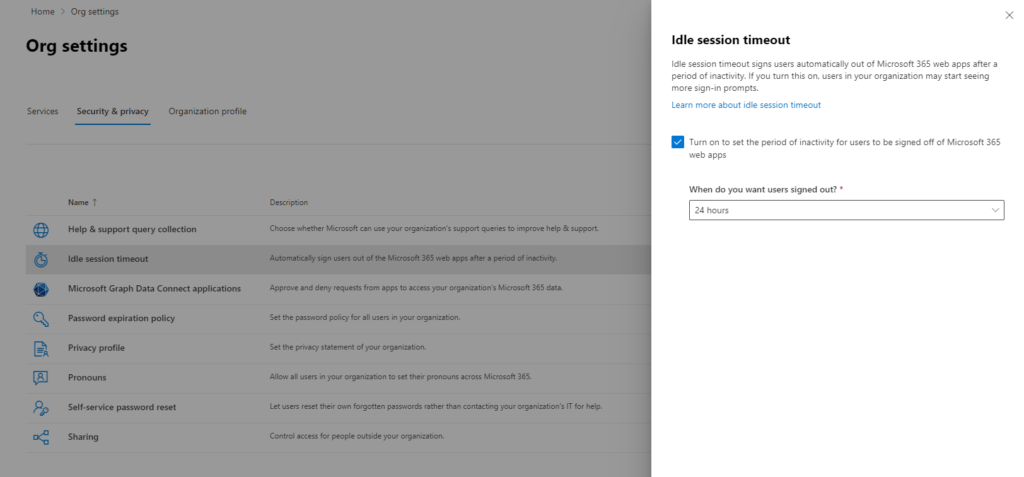
.
- Enable Self-Service Password Reset
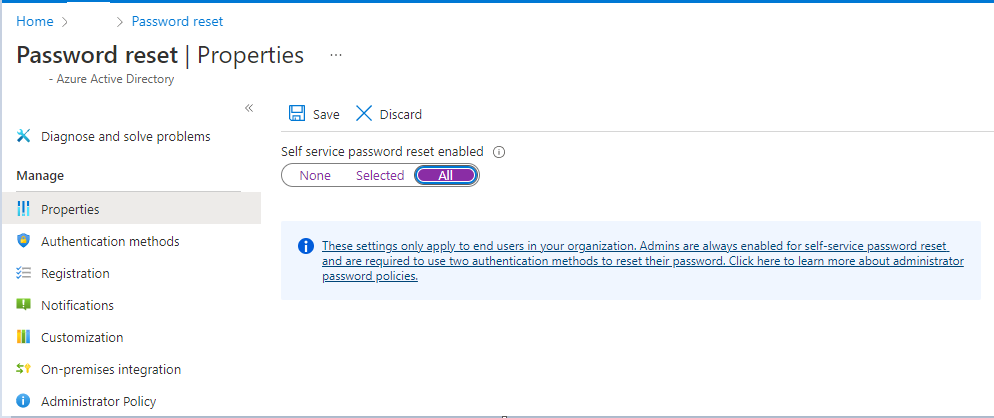
.
- Configure the Service Desk Link or email.
- Enable DKIM for your domain
- DMARC Sample Record
TXT _dmarc "v=DMARC1; p=reject; pct=100; fo=1;rua=mailto:dmarc@azure365pro.com; ruf=mailto:dmarc@azure365pro.com"
.
- Device Clean-Up Rules
Delete devices based on last check-in date – Yes
Delete devices that haven’t checked in for this many days – 180
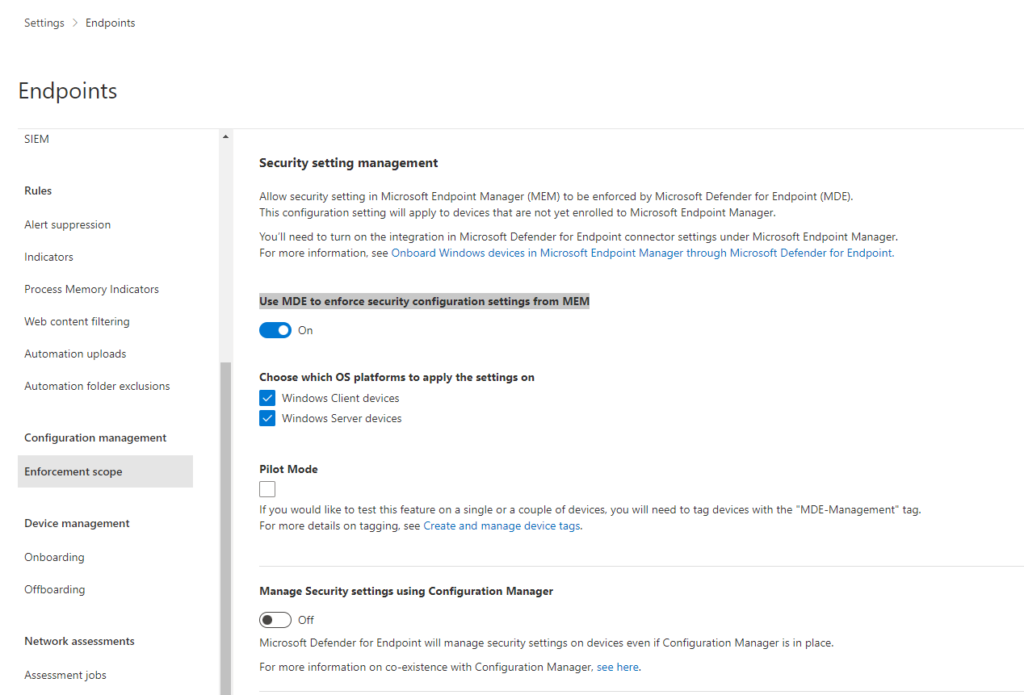
- Security Setting Management
Allow security settings in Microsoft Endpoint Manager (MEM) to be enforced by Microsoft Defender for Endpoint (MDE).
This configuration setting will apply to devices not yet enrolled in Microsoft Endpoint Manager.
You’ll need to turn on the integration in Microsoft Defender for Endpoint connector settings under Microsoft Endpoint Manager.”
.
Use MDE (Microsoft Defender for Endpoint) to enforce security settings from MEM (Microsoft Endpoint Manager)
So that Servers and Client Policies can be managed from MEM (Microsoft Endpoint Manager) and not from SCCM
.
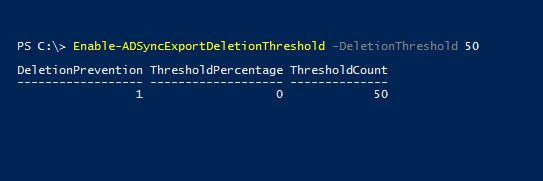
Setting Deletion Threshold on Azure AD Connect
It’s wise to reduce your Azure AD Connect deletion threshold from 500 to 50. suppose your total user base is from 3000 to 5000 users. So that you are Cloud environment is unaffected when something worse happens on your on-premises Active Directory.
The default value is 500.
Get-ADSyncExportDeletionThreshold
Enable-ADSyncExportDeletionThreshold -DeletionThreshold 50
if the action is intentional.
Disable-ADSyncExportDeletionThreshold
.
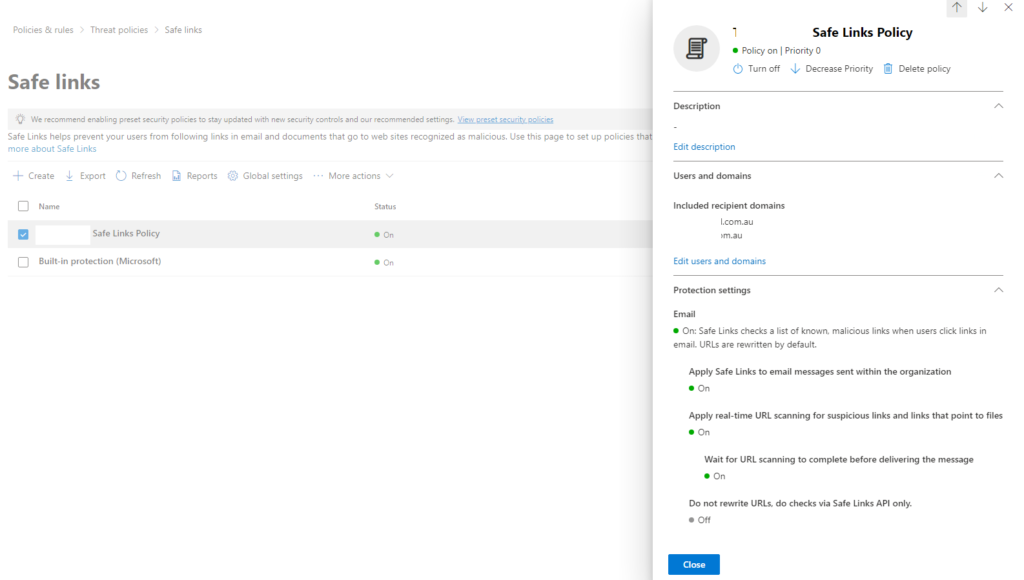
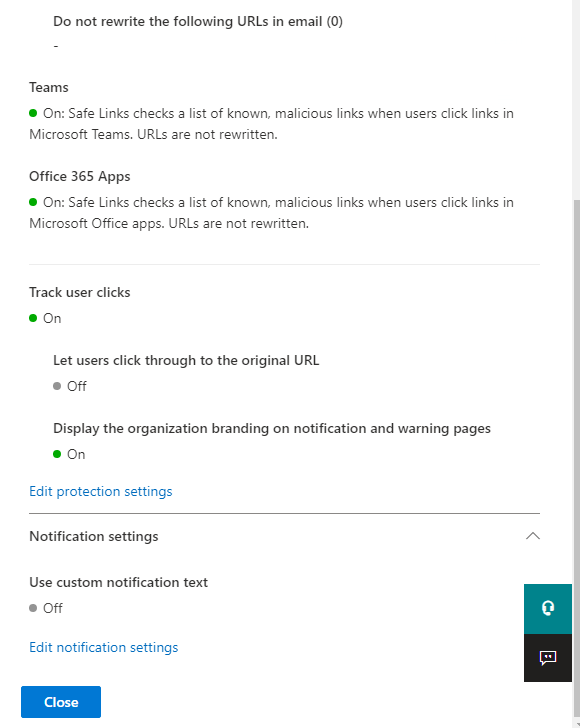
- Add Safe Links Policy
https://security.microsoft.com/safelinksv2
.
- Add Safe Attachments Policy
https://security.microsoft.com/safeattachmentv2
.
- Add Anti-Phishing Policy
https://security.microsoft.com/antiphishing
.
Intune Customization Policy – Hide Reset
- Hide remove button on corporate Windows devices
- Hide reset button on corporate Windows devices
- Hide remove button on corporate iOS/iPadOS devices
- Hide reset button on corporate iOS/iPadOS devices
Enter Organization Name and Privacy URL – Otherwise it will not allow to save
.
Enable Intune to access Windows Diagnostic Data
Questionable URLs detected in message – Microsoft 365