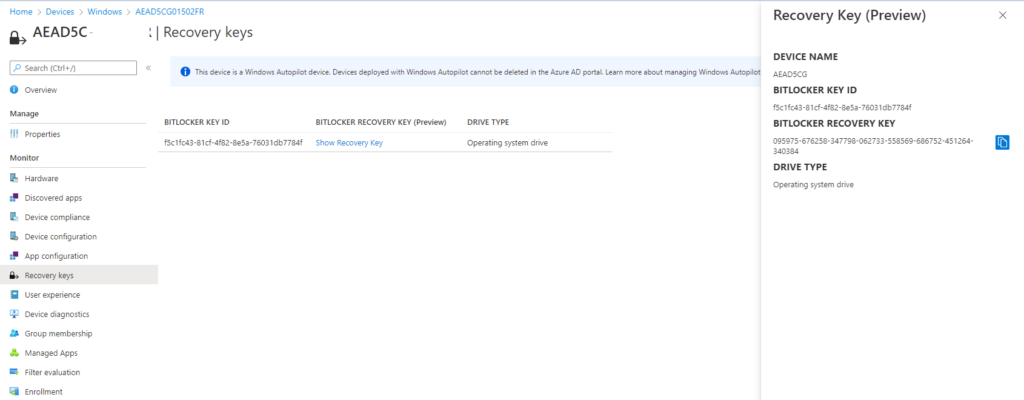
Note: BitLocker Policy configurations are not applicable for the devices that enrolls through Autopilot Enrollment. As the new devices gets encrypted automatically.
- Autopilot Enrollment method for enrolling devices to Microsoft Intune has its own automatic encryption without a BitLocker Policy
- By default, XTS-AES 128-bit (default) BitLocker configuration is applied to Autopilot Enrolled device.
- BitLocker policy can be used for Hybrid Joined Devices. (Devices which are applied via SCCM should not have any impact on this)
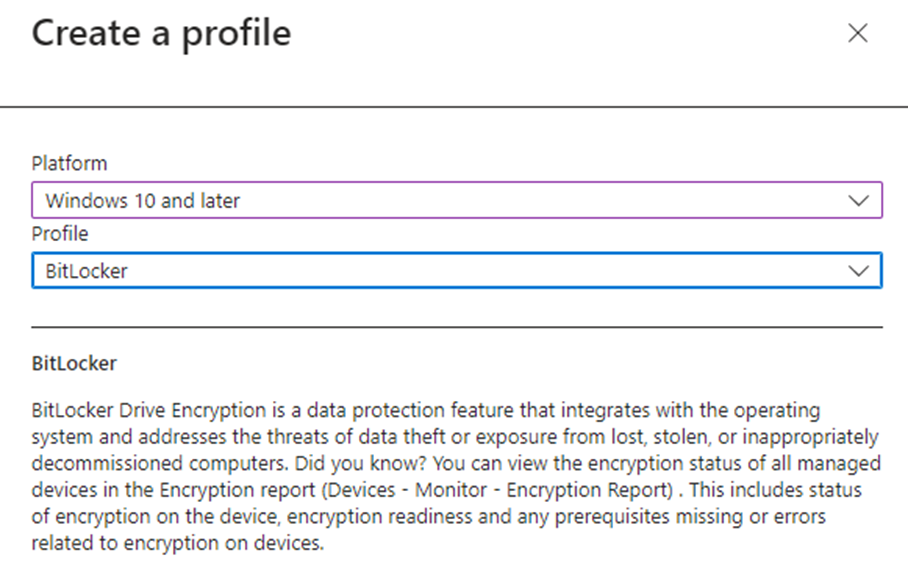
M365 Disk Encryption Profile to deploy BitLocker using Intune for your laptops and desktops, Microsoft Made it seamless to deploy them.
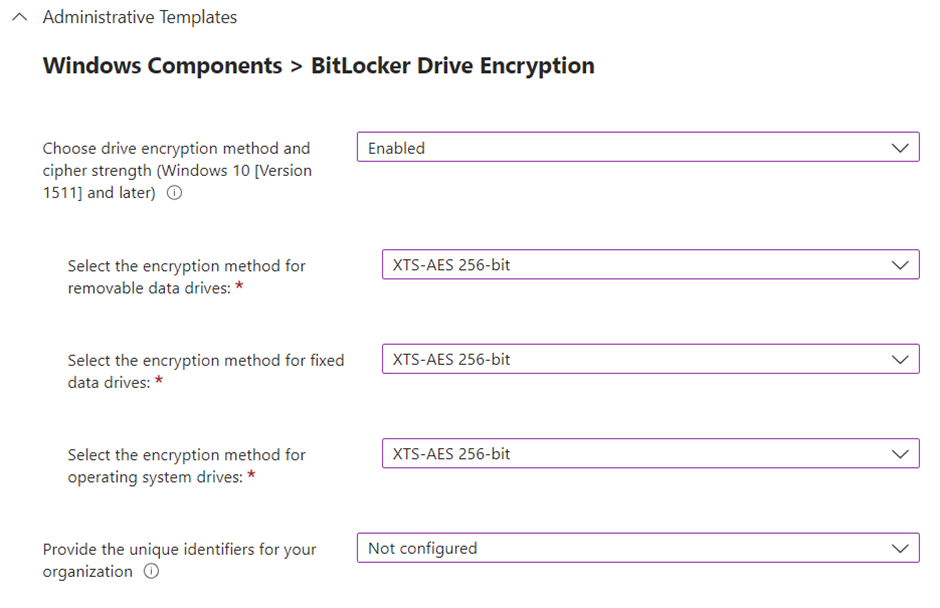
Note: We recommend going on with 128 bits as Autopilot is encrypting 128 bits by default.
If you go with 128 bits. if you have Auto Pilot Devices it’s going to be automatically encrypted and if you have a 128-bit BitLocker policy applied on top of 128 bit. it’s going to apply seamlessly, and no changes will be made., So that you can keep 128 bits across the environment.
If you go with 256 bits. if you have Auto Pilot Devices it’s going to be automatically encrypted and if you have a 256-bit BitLocker policy applied on top of 128 bit. it’s not going to apply seamlessly, and the device needs to be decrypted to encrypt again, Either Manual or You need to apply a custom registry to disable default encryption so that you can keep 256 bits across the environment.
Hence, we recommend 128 bits, so that everything goes smooth on an Auto Pilot Environment even without a bit locker Policy.

We are recommending 128 bit – Not 256 bit.
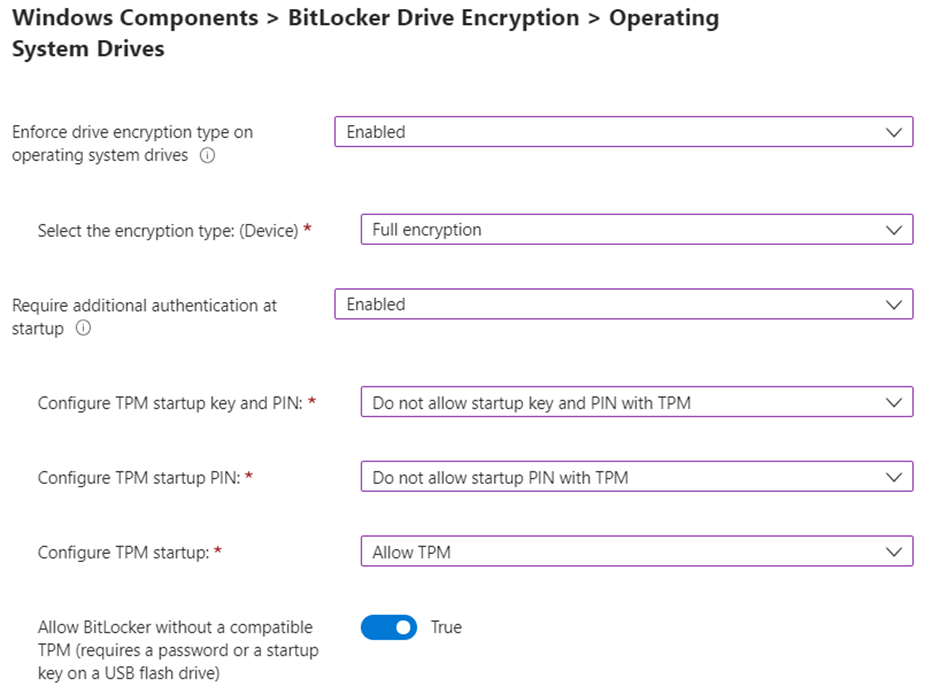
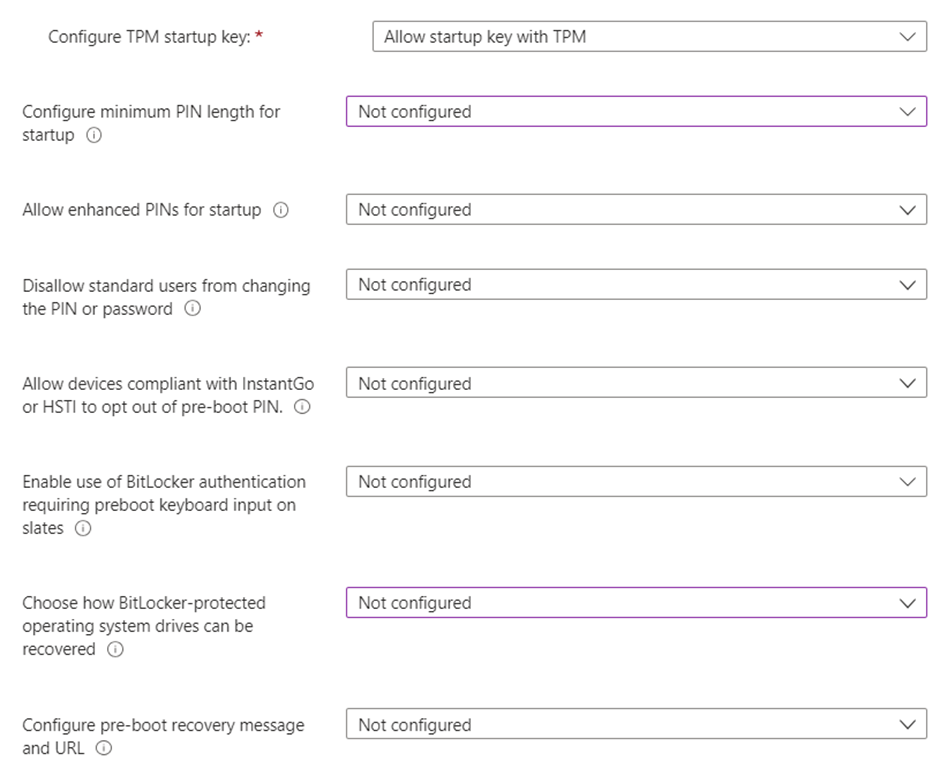
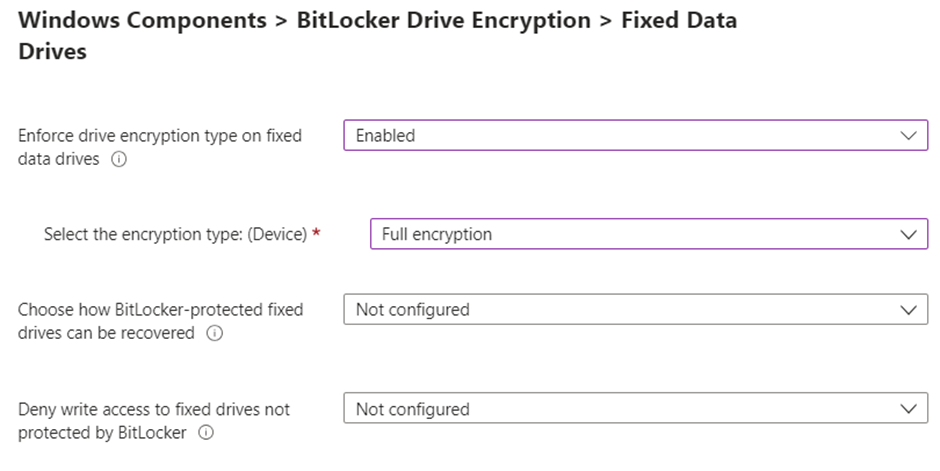
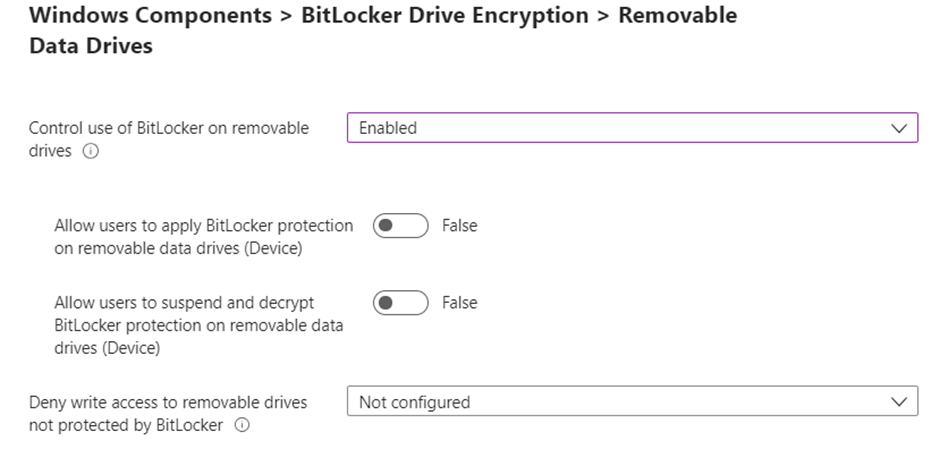
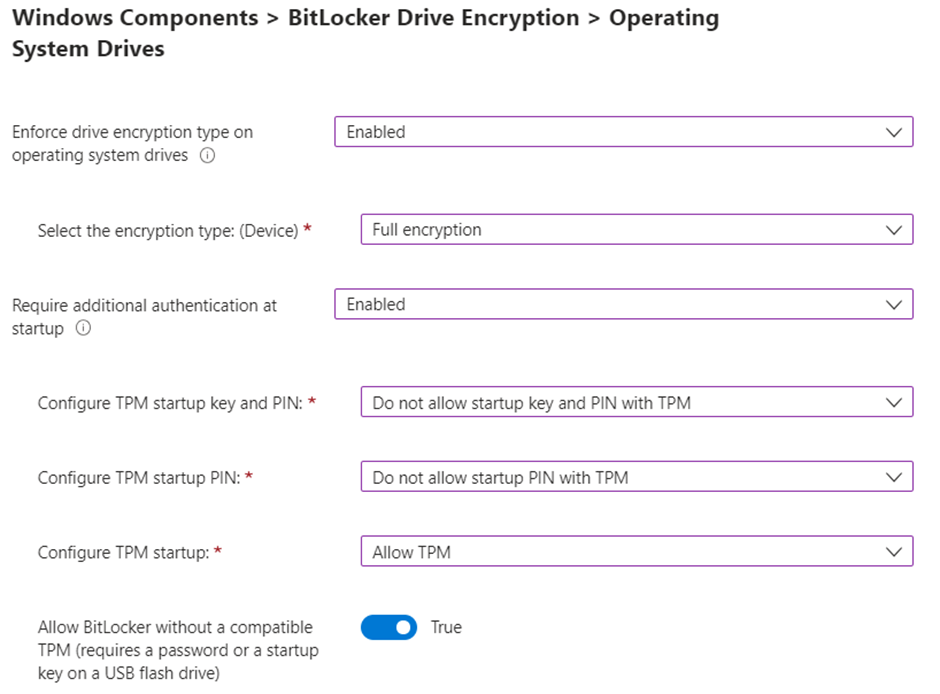
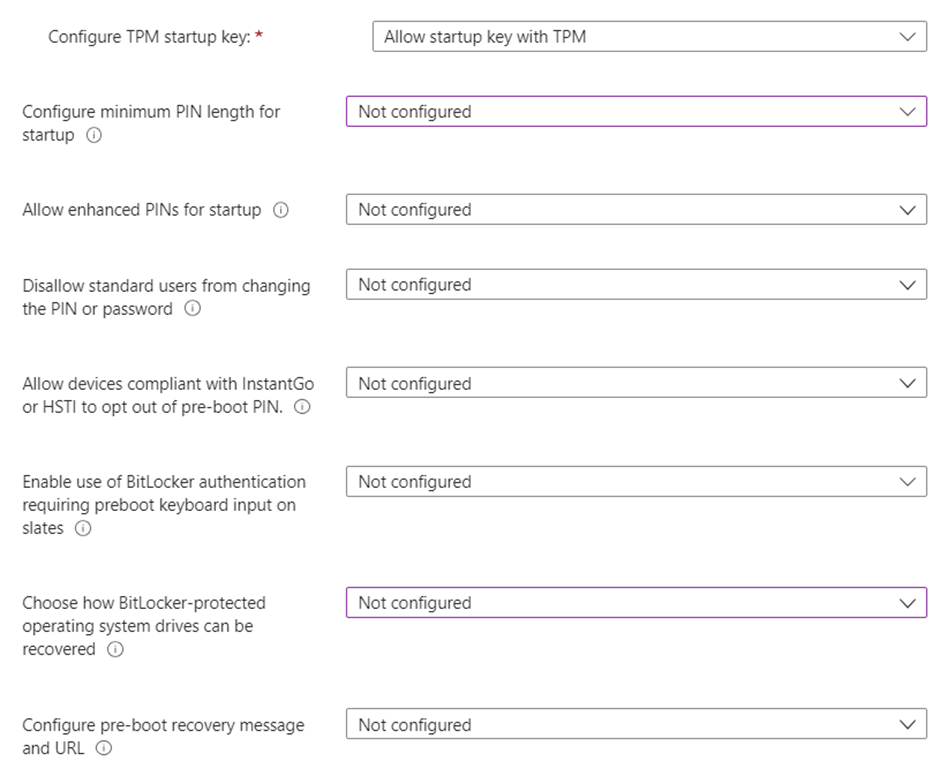
BitLocker Silent Deploy
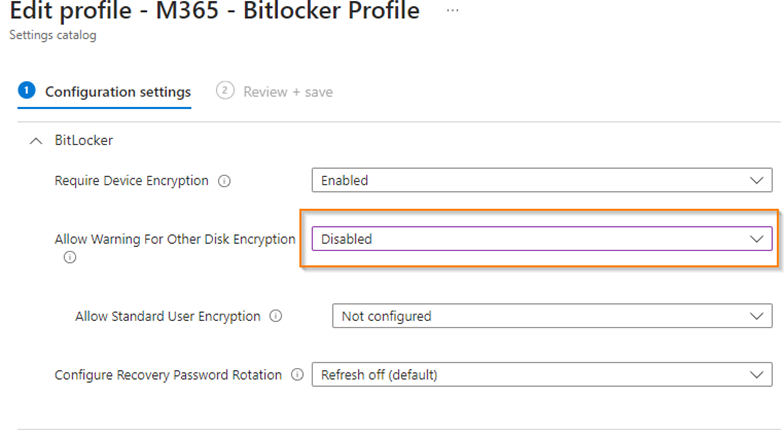
Encrypt Windows devices with BitLocker in Intune – Microsoft Intune | Microsoft Docs
Known Errors –
Start – Eventvwr – Application and Service Logs – Microsoft – Windows – Bitlocker-API – Management
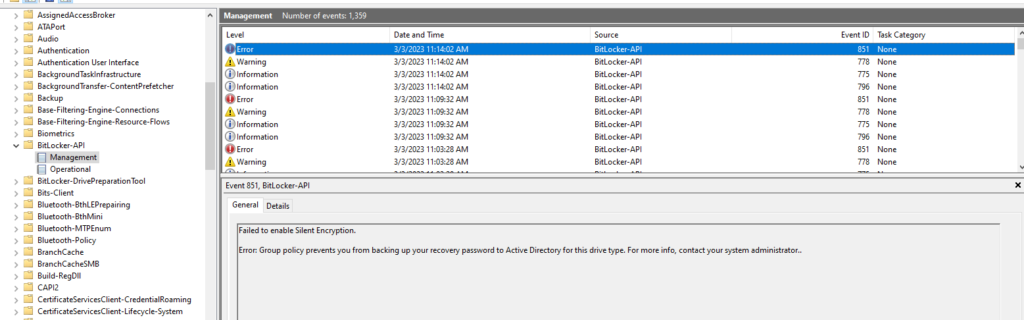
It Failed to enable Silent Encryption.
Error: Group policy prevents you from backing up your recovery password to Active Directory for this drive type. For more info, contact your system administrator.
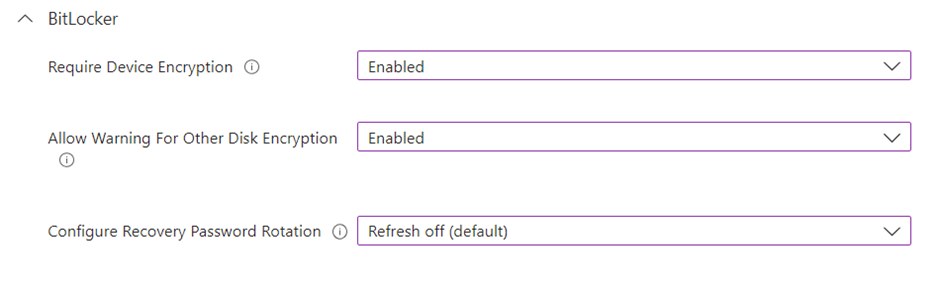
Solution – Policy Misconfigured – Require device to backup recovery information to Azure AD is not Configured – It should be configured to resolve it.
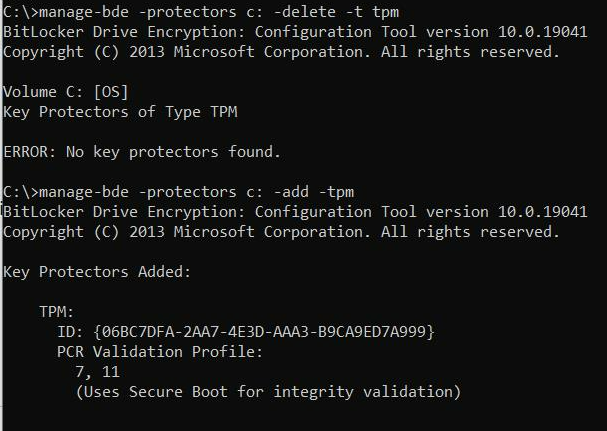
Error: BitLocker cannot use Secure Boot for integrity because it is disabled.
manage-bde -protectors -get c:
This shows that PCR 7 is NOT in use / Even though the secure boot is enabled.
Solution –
manage-bde -protectors c: -delete -t tpm manage-bde -protectors c: -add -tpm
Error 1: BitLocker could not be enabled
The Bitlocker encryption key cannot be obtained. Verify that the Trusted Platform Module (TPM) is enabled and ownership has been taken.if this computer does not have TPM, verify that the USB drive is inserted and available.
C: was not encrypted
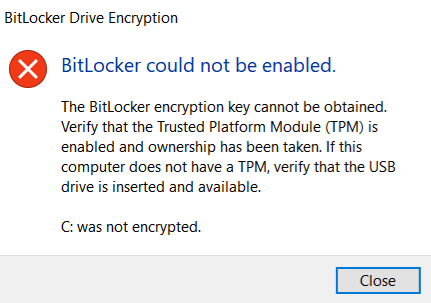
Error 2: BitLocker cannot use Secure Boot for integrity because the UEFI variable ‘SecureBoot’ could not be read.
Solution for #1 and #2: Clear the TPM using TPM.msc