F5 has different modules and one of them is LTM – Local Traffic Manager . At this stage I would like to explain when LTM is faced on the internet facing side. On how we can save Public IPs .
LTM has Policies feature where you can re direct traffic based on DNS hostname. So in our Case For 1 Public IP we share more than 15 Apps
AppA.azure365pro.com
AppB.azure365pro.com
AppC.azure365pro.com
AppD.azure365pro.com
and goes on and we have a wildcard SSL Sharing the same SSL Certificate. Even though Public IP is much cheaper nowadays. It allows things to manage to remove and Add applications without touching the perimeter firewall.
Just Add DNS Record and use LTM Policies to re direct traffic to the specified Virtual Server. It works seamlessly without complicating our life in to many custom iRules
Lets consider your VLANs and Self IPs are in Place with Traffic allowed from Load Balancer to Desired Apps and SSL Imported to Load balancer Already.
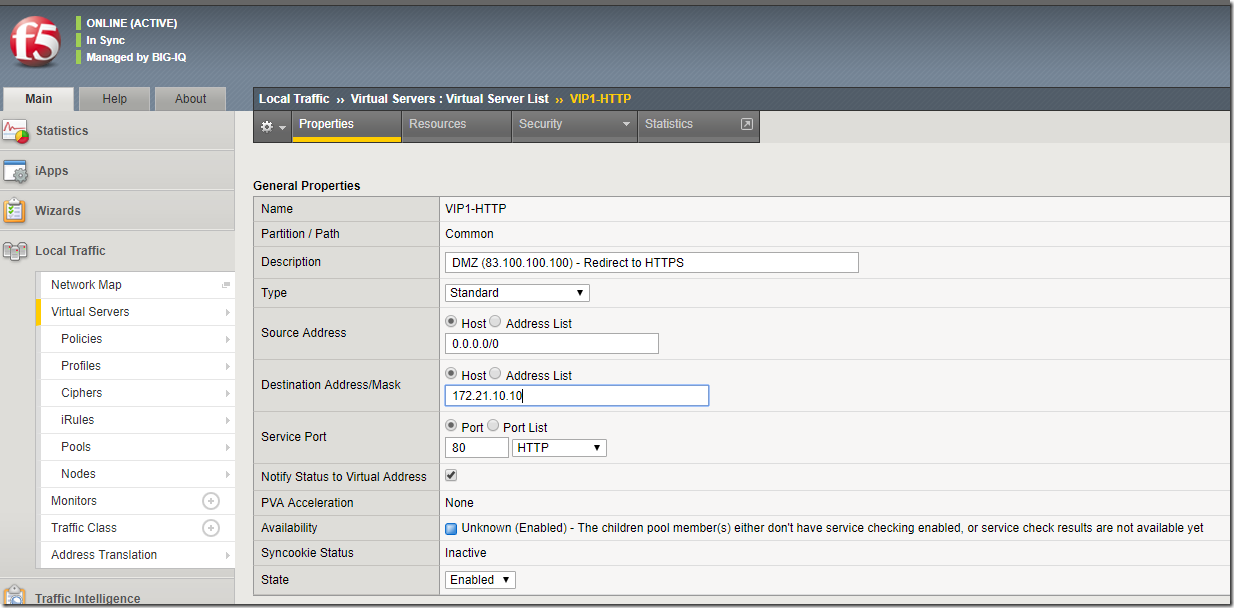
Its my First Virtual Server just to redirect all HTTP to HTTPS Traffic.
83.100.100.100 is my Public IP – Allowed only 443 to 80 to F5 LTM From Perimeter Firewall
172.21.10.10 is my Private IP – Its just a dummy IP from the Self IP Range Points no where.
Name VIP1-HTTP
Partition / Path Common
Description DMZ (83.100.100.100) – Redirect to HTTPS
Type – Standard
Source Address Host 0.0.0.0/0
Destination Address/Mask Host 172.21.10.10
Service Port Port 80
Notify Status to Virtual Address Checked
PVA Acceleration None
Availability Unknown (Enabled) – The children pool member(s) either don’t have service checking enabled, or service check results are not available yet
Syncookie Status Inactive
State Enabled
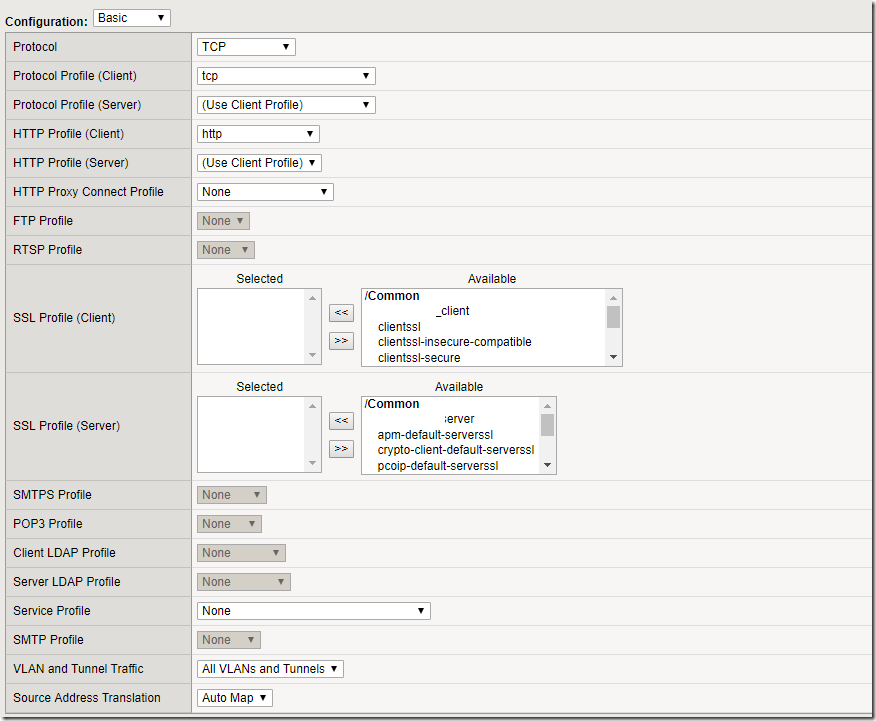
Configuration: Basic
Protocol TCP
Protocol Profile (Client) tcp
Protocol Profile (Server) Use Client Profile
HTTP Profile (Client) http
HTTP Profile (Server) Use Client Profile
HTTP Proxy Connect Profile None
FTP Profile None
RTSP Profile None
SSL Profile (Client) None Selected
Selected Available
SMTPS Profile none
POP3 Profile none
Client LDAP Profile none
Server LDAP Profile none
Service Profile none
SMTP Profile none
VLAN and Tunnel Traffic All VLANS and Tunnels
Source Address Translation Auto Map
Everything left to default.
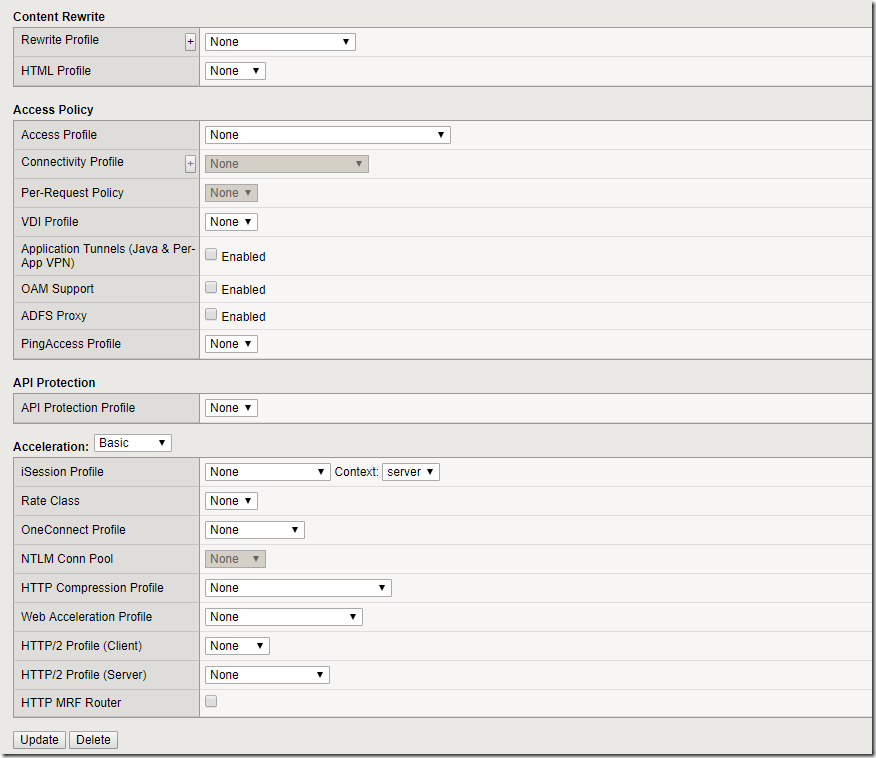
Content Rewrite
Rewrite Profile none
HTML Profile none
Access Policy
Access Profile none
Connectivity Profile none
Per-Request Policy none
VDI Profile none
Application Tunnels (Java & Per-App VPN) Not Enabled
OAM Support Not Enabled
ADFS Proxy Not Enabled
PingAccess Profile none
API Protection
API Protection Profile none
Acceleration:
iSession Profile none Context: server
Rate Class none
OneConnect Profile none
NTLM Conn Pool none
HTTP Compression Profile none
Web Acceleration Profile none
HTTP/2 Profile (Client) none
HTTP/2 Profile (Server) none
HTTP MRF Router Not Enabled
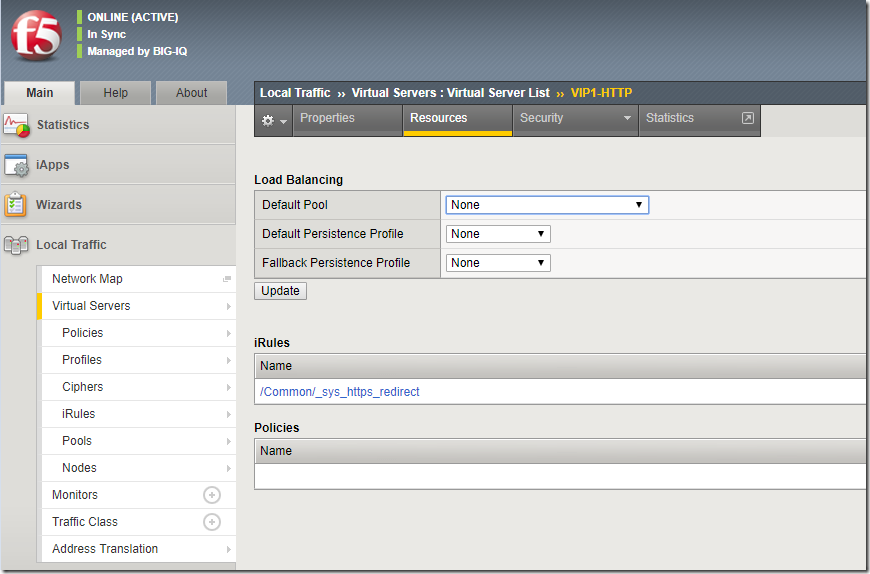
Load Balancing
Default Pool none
Default Persistence Profile none
Fallback Persistence Profile none
iRules (Use the Default irule to redirect all traffic to Https no matter whatever it is)
/Common/_sys_https_redirect
Security Settings . We have ASM – Application Security Manager enabled am not going to into that in this article. Definitely it has amazing features.
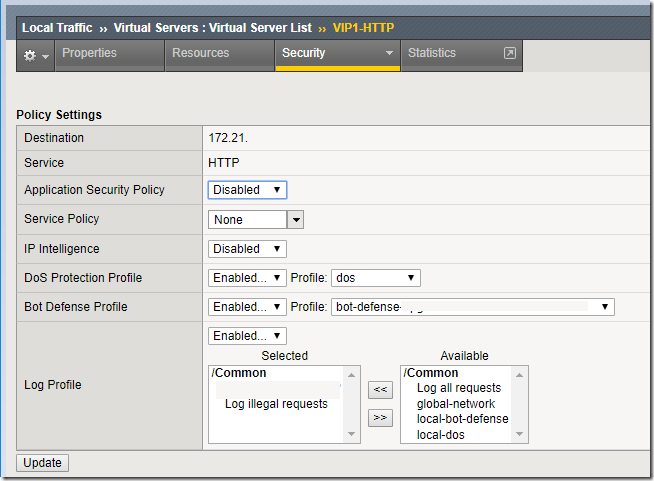
Policy Settings
Destination 172.21.10.10:80
Service HTTP
Application Security Policy Disabled
Service Policy none
IP Intelligence Disabled
DoS Protection Profile Profile: Enabled
Bot Defense Profile Profile: Enabled
Log Profile Log illegal Requests
Now we are done with HTTP To HTTPS redirection.
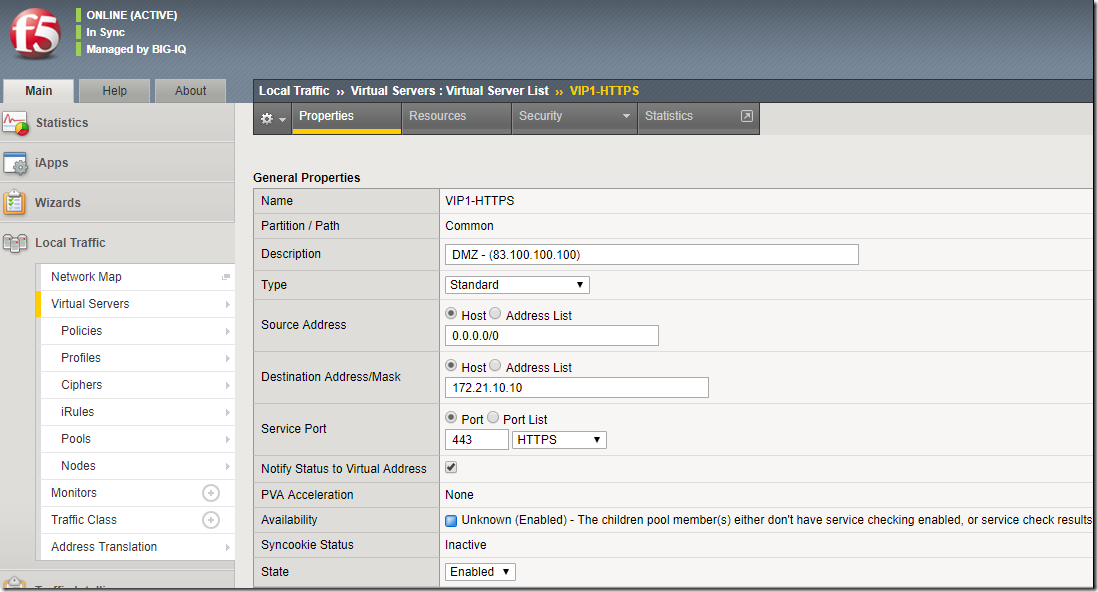
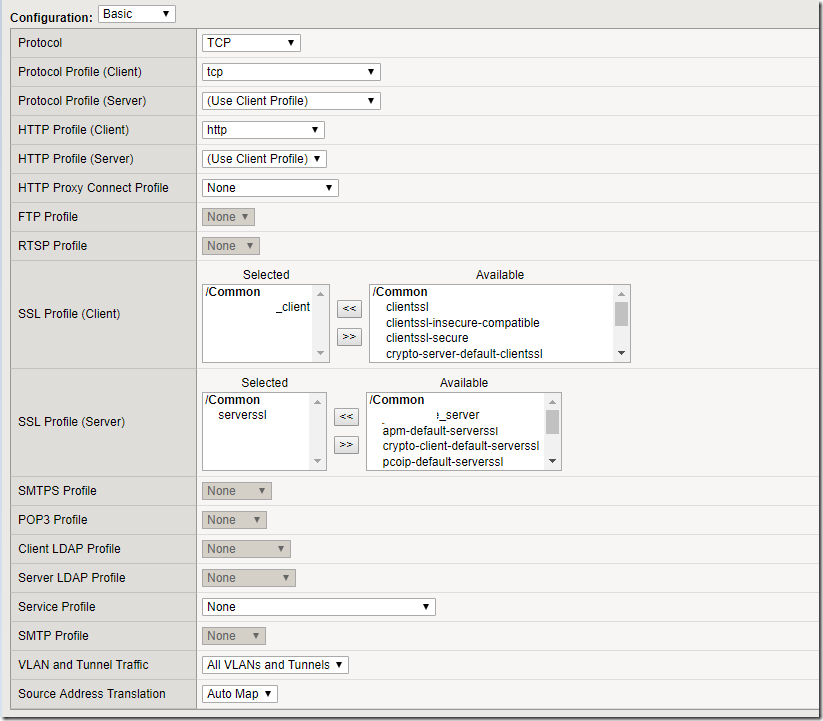
Lets create a Virtual Server for HTTPS
General Properties
Name VIP1-HTTPS
Partition / Path Common
Description DMZ (83.100.100.100)
Type Standard
Source Address Host 0.0.0.0/0
Destination Address/Mask Host 172.21.10.10
Service Port Port 443
Notify Status to Virtual Address Enabled
PVA Acceleration None
Availability Unknown (Enabled) – The children pool member(s) either don’t have service checking enabled, or service check results are not available yet
Syncookie Status Inactive
State Enabled
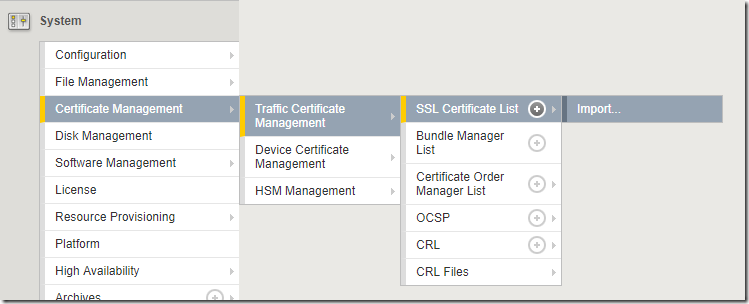
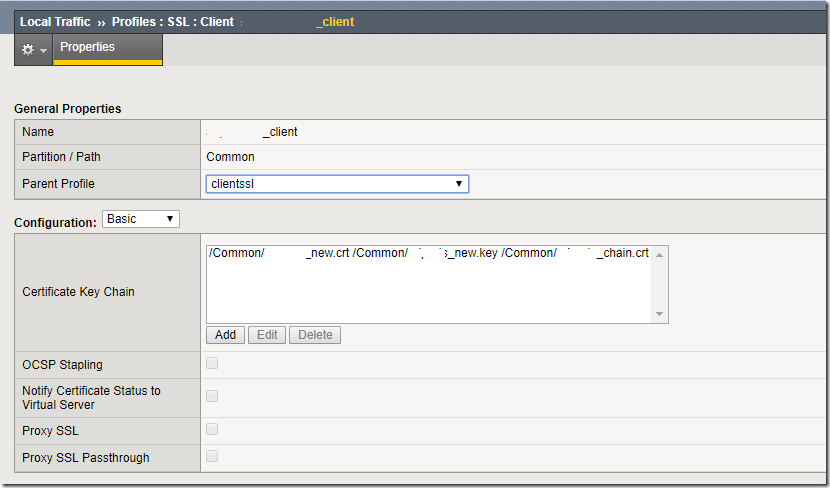
Get the SSL Issues and Import using a pfx file. So that we can use them on the HTTPS Virtual Server.
Import pfx file – Certificate Management – Traffic Certificate Management – SSL Certificate List – Import
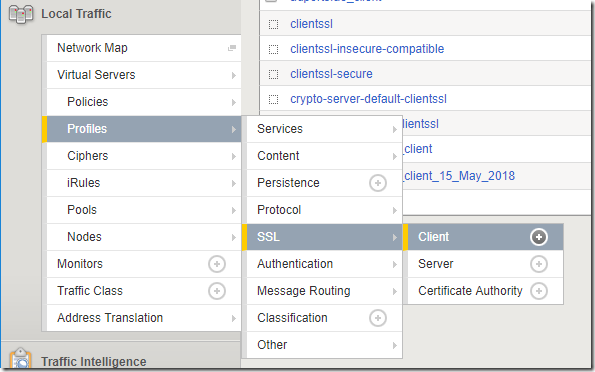
Local Traffic – Profiles – SSL
Create a Client Profile and Assign the SSL
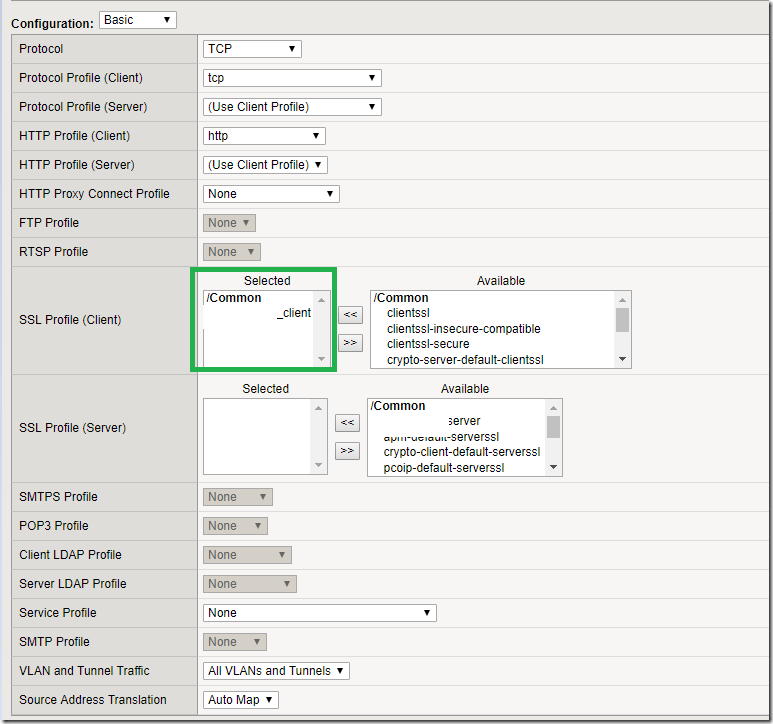
Exactly Same as HTTP Profile . Only difference in here is
SSL Assigned on Both.
SSL Profile (Client) – Valid Wild Card SSL
SSL Profile (Server) – You place a default SSL or leave it Empty
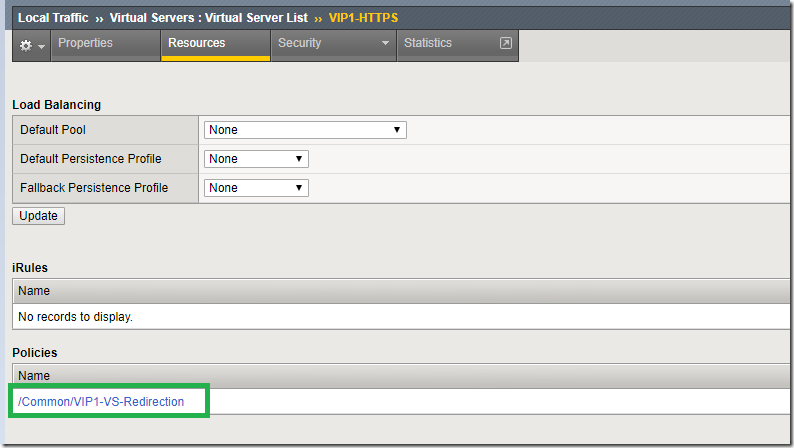
Leave Everything to none. Lets see how we can create this Policy. To Get App Redirection Working.
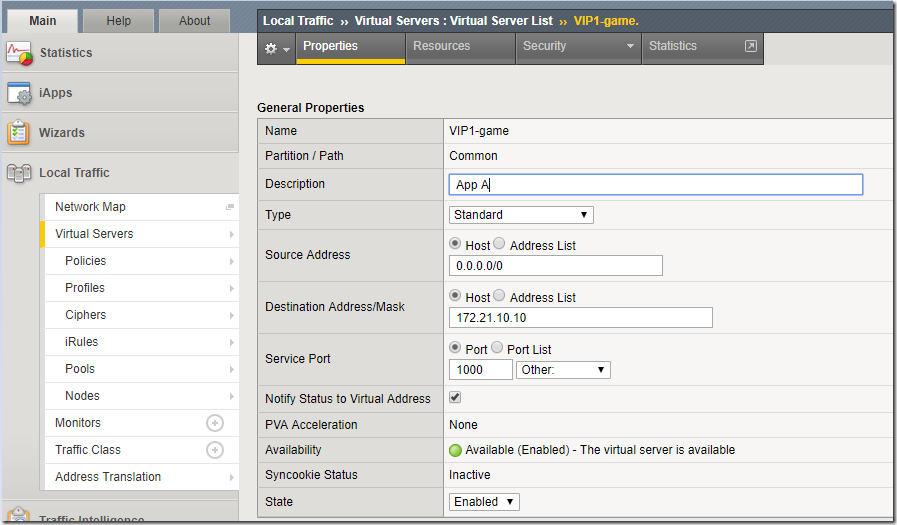
- Lets Create App A with Same Settings but Service Port 1000
- Lets Create App B with Same Settings but Service Port 1001
- Lets Create App C with Same Settings but Service Port 1002
- Lets Create App D with Same Settings but Service Port 1003
It can go on with the Same Shared Public IP.
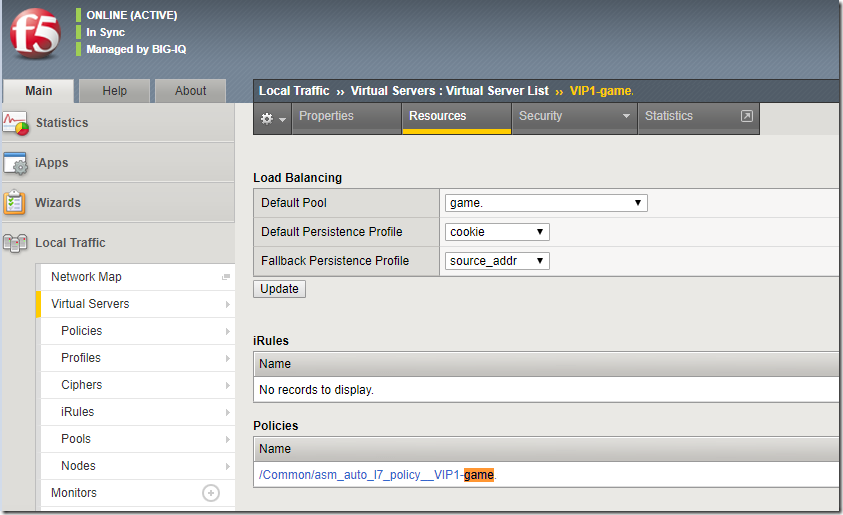
SSL is Assigned for SSL Profile (Client)
game Virtual Server with Custom port 1000 is directing the traffic to game Pool . which has the real game pool members.
Default Pool
Default Persistence Profile cookie
Fallback Persistence Profile source_addr
Lets Create a Policy.
For Example
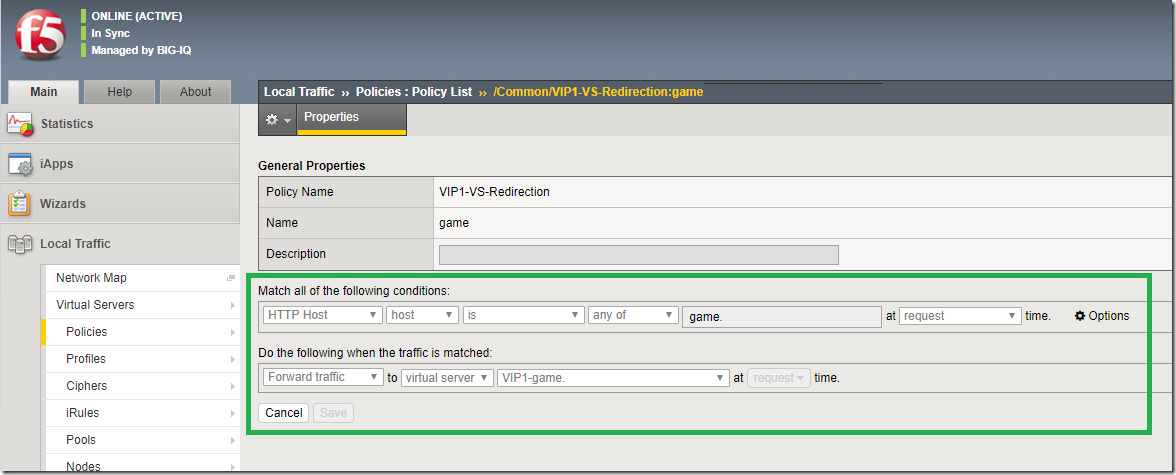
AppA.azure365pro.com (In my Case App A is game.azure365pro.com)
AppB.azure365pro.com
AppC.azure365pro.com
HTTP Host host is any of game.azure365pro.com request time (DNS hits the main Virtual Server)
Forward Traffic to Virtual Server game.azure365pro.com (Forward Traffic to Real Member)
Now Apply the Policy and Assign them to the HTTPS Main Pool listening on 443.
Now you can use the same policy to forward multiple hostnames to different pools with same ssl and same public ip.
It helps to manage F5 more simpler on the perimeter level with minimal public IPs giving a lot of flexibility.
No doubt Its an amazing product. Their APM module is amazing as well . Will Discuss that in future posts.