Hybrid Modern Authentication (HMA) for Exchange On-Premises is being there for while which has a amazing set of features to integrate your endpoint logins to terminate in Azure AD directly. Azure AD will give a clear indication on the health of your identity and a clear visibility giving you access to Azure AD workbooks with meaningful sign in data using log analytics .It is Supported from Exchange 2013 (CU19) and 2016 (CU8).Also you can use Azure AD issued tokens to authenticate your Exchange servers on-premises which improves security drastically where you are taking a step moving away from basic Authentication and getting the advantage of Oauth. Also this is a preliminary step if you wish to utilize Windows In tune and Outlook for iOS so that you gain the advantage of device based Conditional Access.
As you are aware basic auth on Exchange Online is going away for good where Its time to move away from legacy authentication methods to keep your environment secured. I was waiting for the day Exchange Web Services needs to be killed where the first step is already announced that it will no longer receive feature updates moving away to Microsoft Graph taking advantages of all Microsoft Services from a single endpoint.
Currently its not easy to enable HMA in Exchange On-Premises as Oauth is still new for On-Prem environments where there is too much usage on legacy protocols from Meeting Room Systems to Service Desk Applications and Oracle EBS using EWS and basic auth methods so its a journey you should start moving towards Oauth. We are seeing too many custom applications using Exchange Web Services to process emails which was the only way back then to access mailbox or calendar data. I still remember writing scripts to create folders in all mailboxes using EWS Managed API for Enterprise vault Managed folders.
It would be definitely one of the best initiative to improve security and taking advantage of your Azure AD investment which you are getting through Office 365 Services. Most of the enterprise environments going to remain hybrid as there is lot of legacy behind these systems.
In Short –
- Improved Security with Azure AD Conditional Access.
- Improved End user Experience similar single sign ON experience like Teams or any other Office 365 services.
- Developers can leverage latest authentication mechanisms with Microsoft Graph to retrieve and process Office 365 and On-Premises data.
- Intelligent Identity Analytics.
Turning ON Hybrid Modern Authentication without proper planning can bring down most of your users in few hours. If your applications using EWS with basic auth it works aside with modern authentication. As enabling and disabling takes effect in 60 to 120 mins in a 4 node DAG approx. IISreset and rebooting services can help to take effect instantly.
- No Exchange 2010 in your environment.
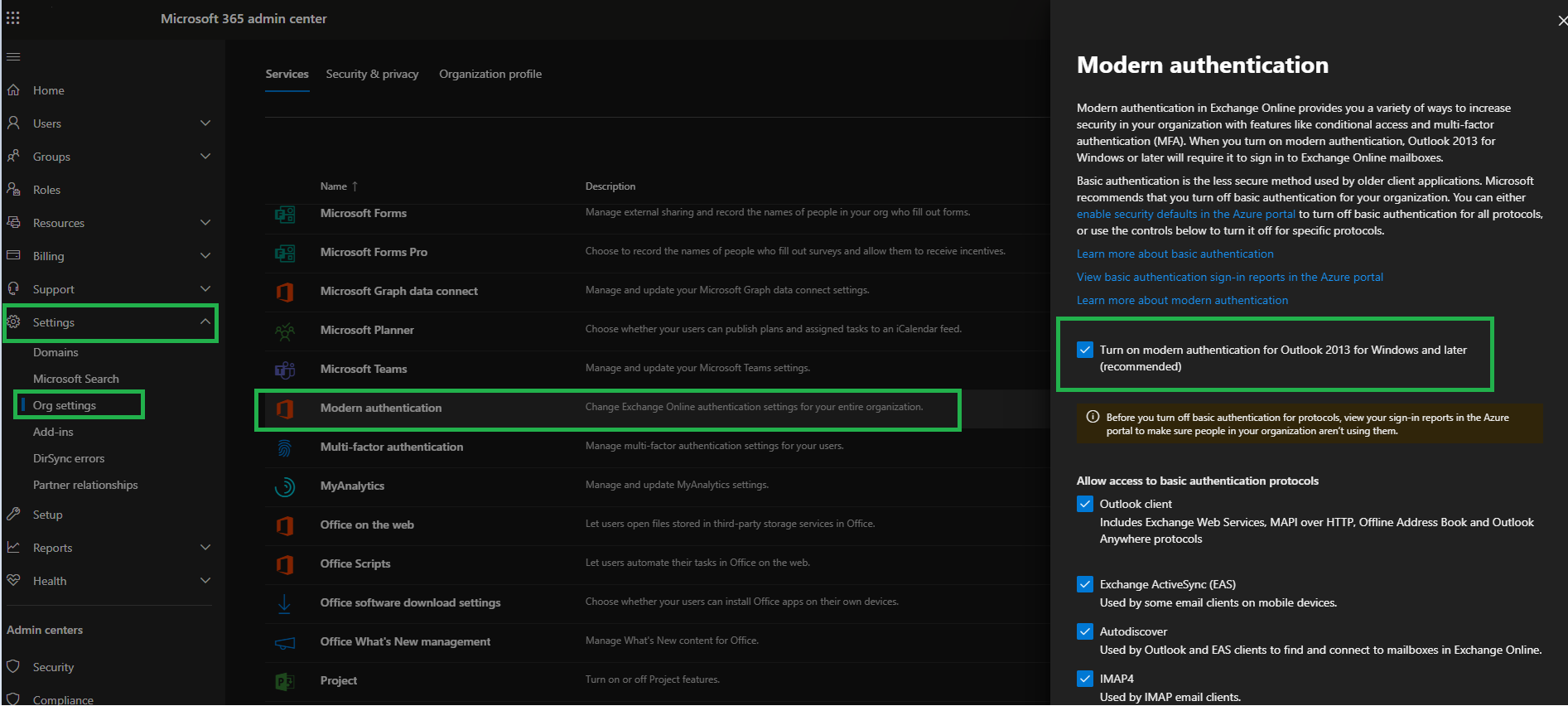
- Make sure OAuth for Exchange Online is enabled. (For tenants created before August 1, 2017, modern authentication is turned off)
Connect-ExchangeOnline
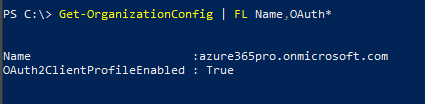
Get-OrganizationConfig | FL Name,OAuth*
To Enable
Set-OrganizationConfig -OAuth2ClientProfileEnabled $true
or you can check in Admin Center https://admin.microsoft.com
- Exchange server 2013 CU19 and above, or Exchange server 2016 CU8 and above. (Highly Recommended to be on latest roll-up)
- No SSL Offloading on Load Balancer (Most of the Environment have SSL bridging which is what we want https on external and internal servers)
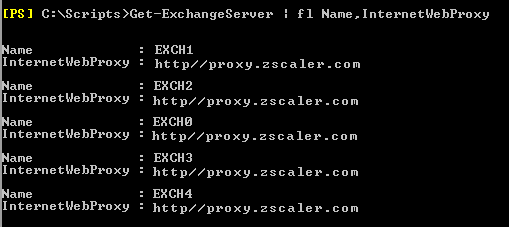
- If Exchange Servers running behind proxy make sure InternetWebProxy is populated (Removed Authentication and SSL inspection for all Microsoft URLs in Forward Proxy)
- Office 365 Hybrid Configuration Wizard is completed.
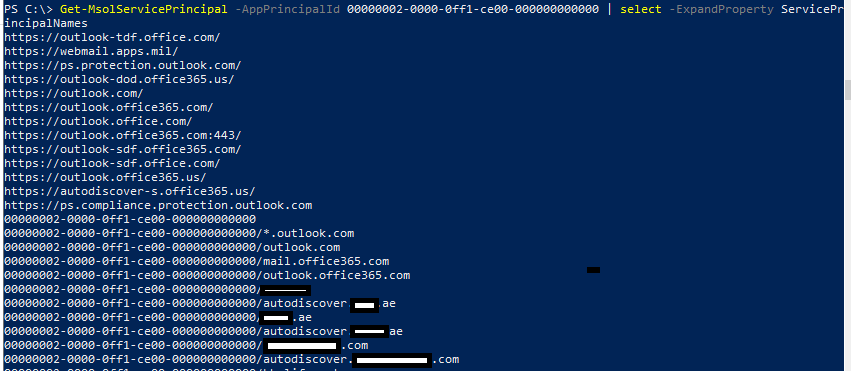
- Your hybrid wizard should add all required ServicePrincipalNames (All Exchange URL entries should be listed here. email.azure365pro.com/autodiscover.azure365pro.com for example)
- Outlook Office 365 Clients work seamlessly while comparing with Office 2016 Clients. (If you have more Office 2016 Clients keep your fingers crossed and get ready for rollback)
Connect-MsolService
Get-MsolServicePrincipal -AppPrincipalId 00000002-0000-0ff1-ce00-000000000000 | select -ExpandProperty ServicePrincipalNames
- Decommission Skype for Business Servers (if you have one follow use this link)
Lets check how to make OAuth Authentication to onprem mailboxes without enabling Modern Authentication first once we gain the confidence and we feel everything works as expected so that you make sure all critical line of business application.
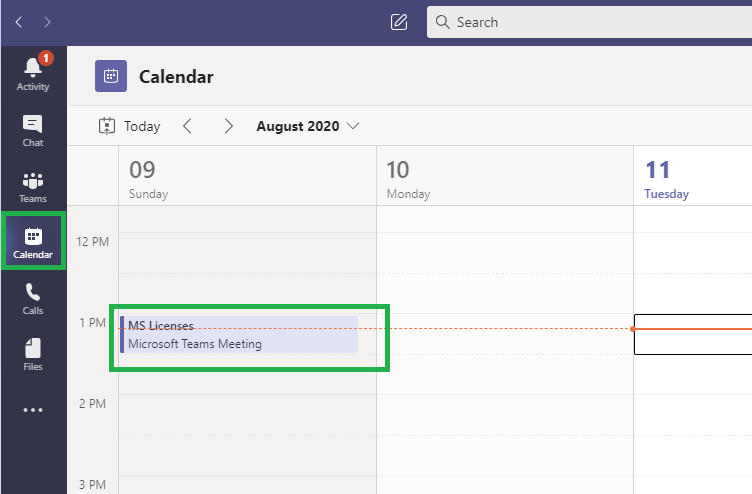
There are several ways to check OAuth is functional and working seamlessly. If Oauth is Active and functional “Calendar Tab Appears in Microsoft Teams for On-Prem users.
All new meetings visible in the Teams Client from On-Premises Exchange Servers to the cloud.
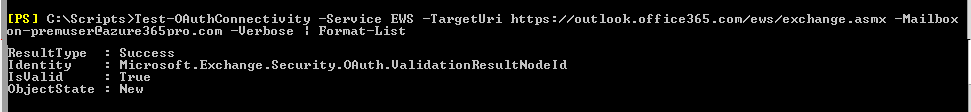
Check On-Prem EWS Connectivity using below command
Test-OAuthConnectivity -Service EWS -TargetUri https://outlook.office365.com/ews/exchange.asmx -Mailbox on-premuser@localhost -Verbose | Format-List
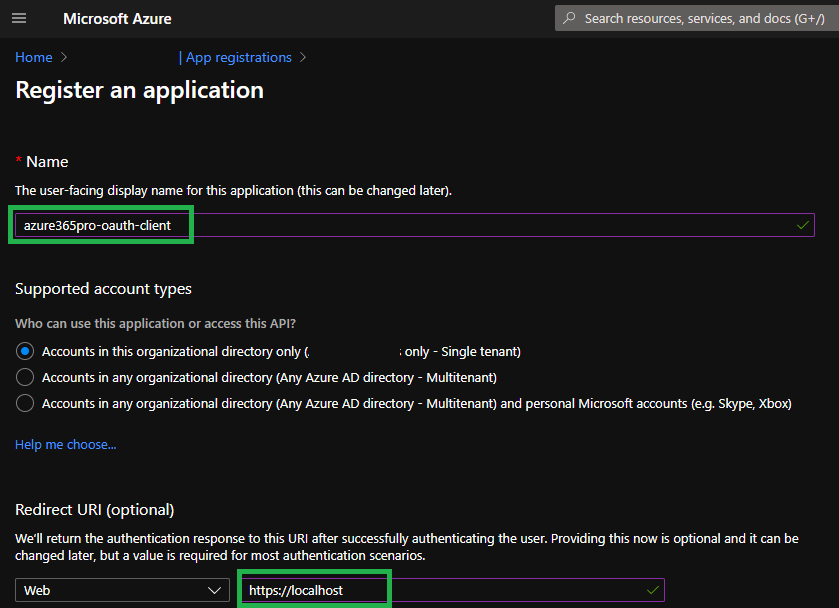
We can also register a application in Azure AD and use OAuth and Microsoft Graph to access On-prem mailboxes.
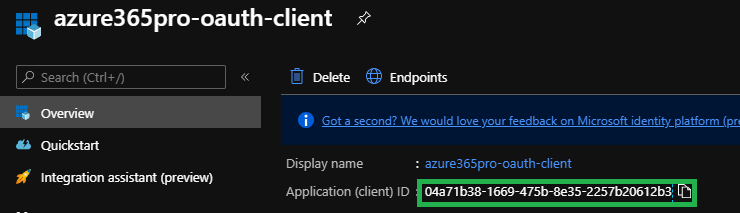
- FriendlyName – azure365pro-oauth-client
- Redirect URI (optional) –
https://localhost
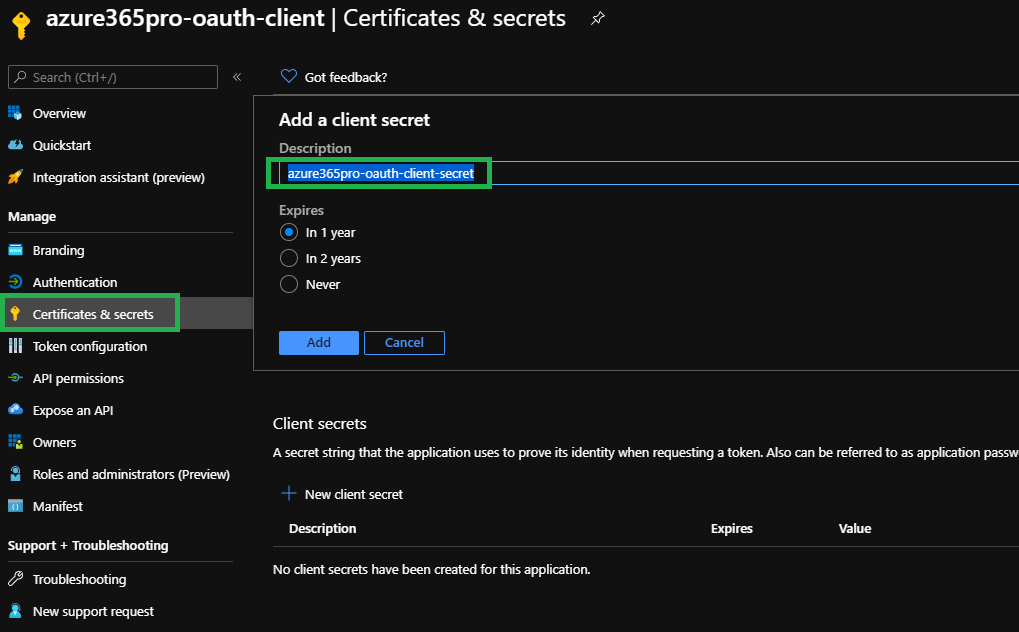
Create a Client Secret and copy the value
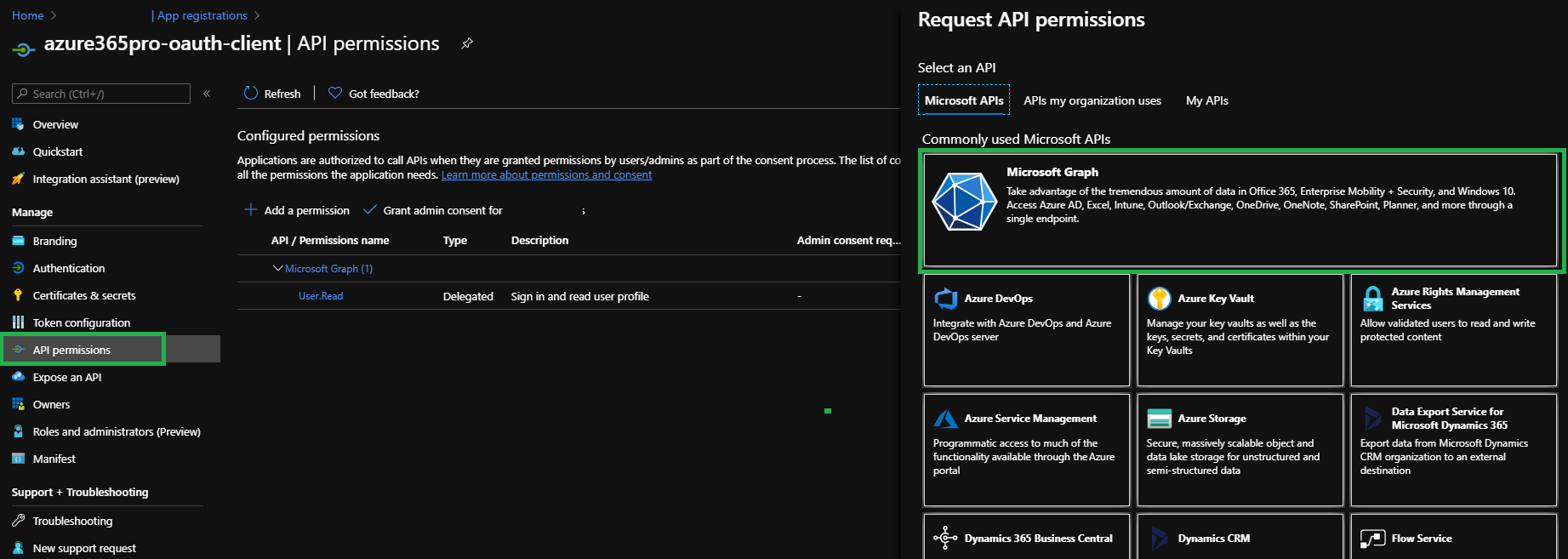
Add Microsoft Graph Permissions –
Choose Microsoft Graph – Delegated Permissions
Mail
Mail.Send
Add Permissions
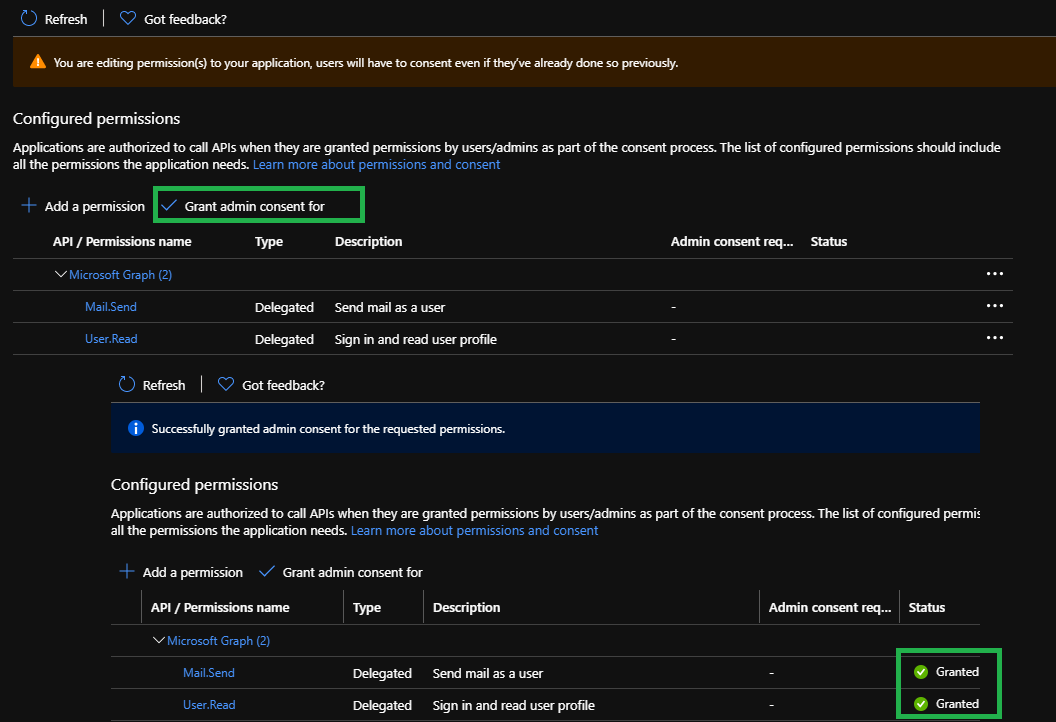
Choose Grant Admin Consent for
Once you see “Granted” We are good to send email using OAuth
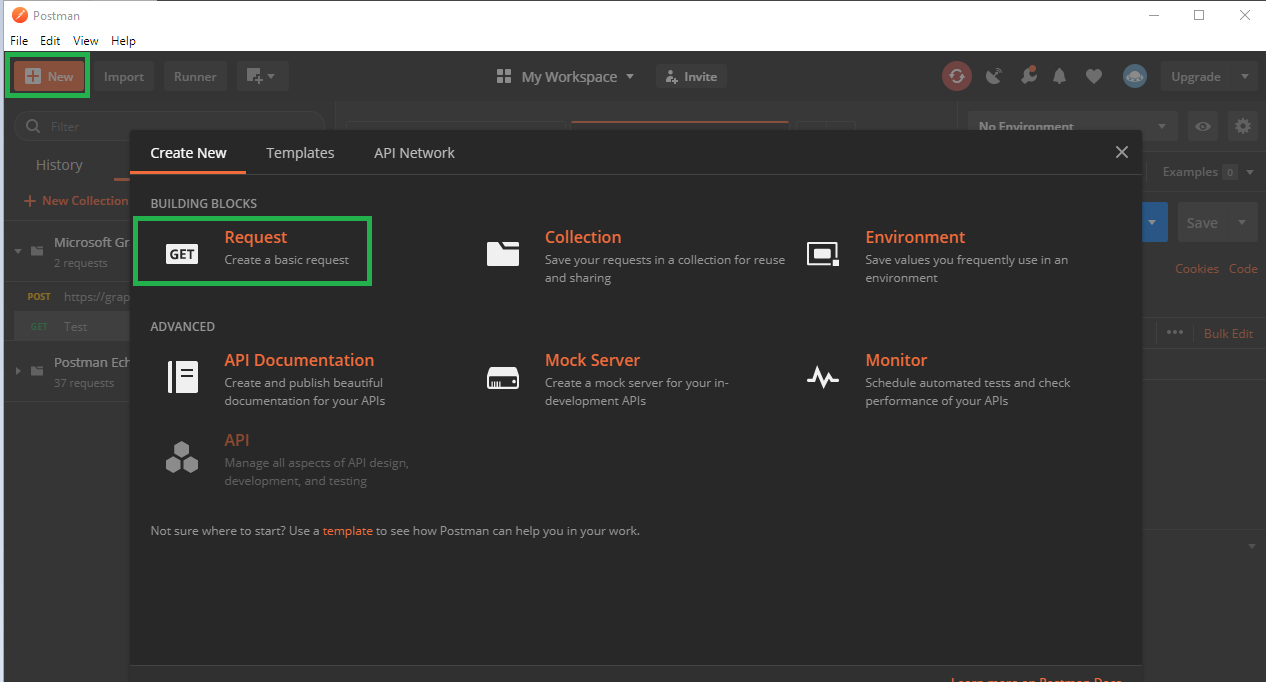
Lets use Postman free version. One of the best tools to test OAuth.
https://www.postman.com/downloads/
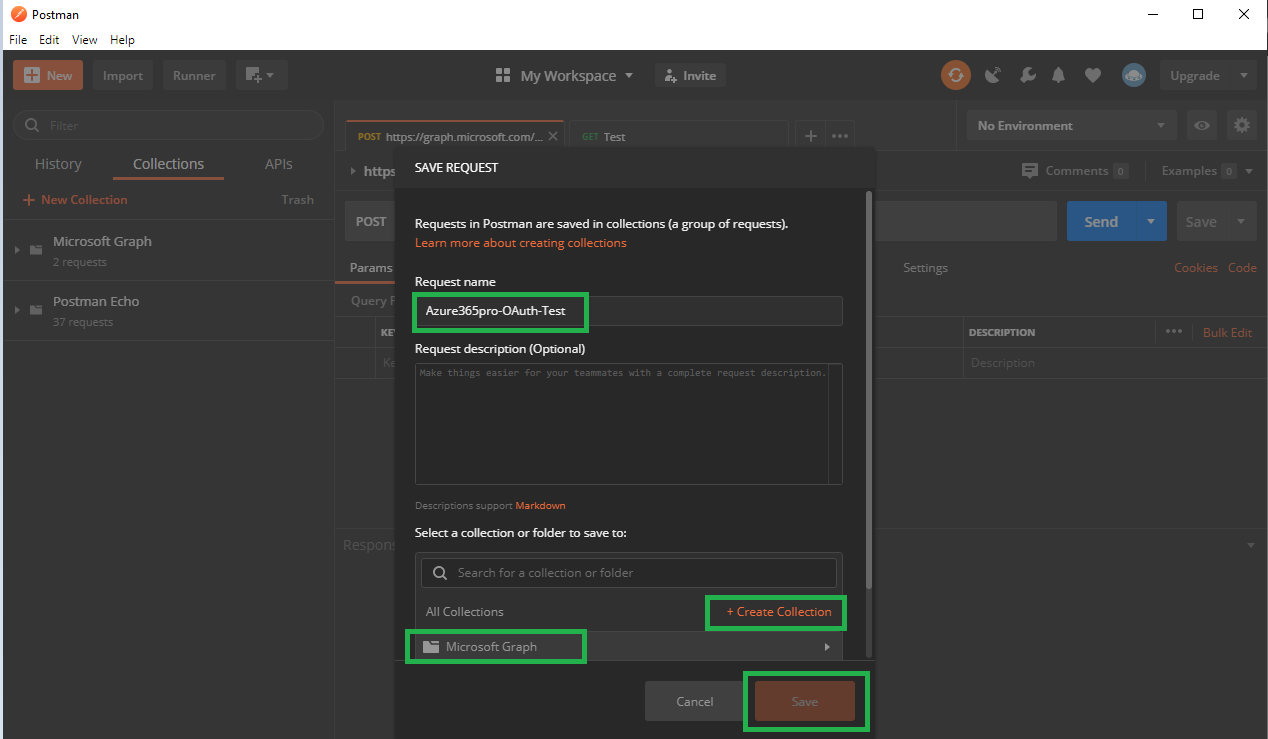
Create New –
Create a Sample Request and Save in to my Collection called Microsoft Graph (Name it whatever you want)
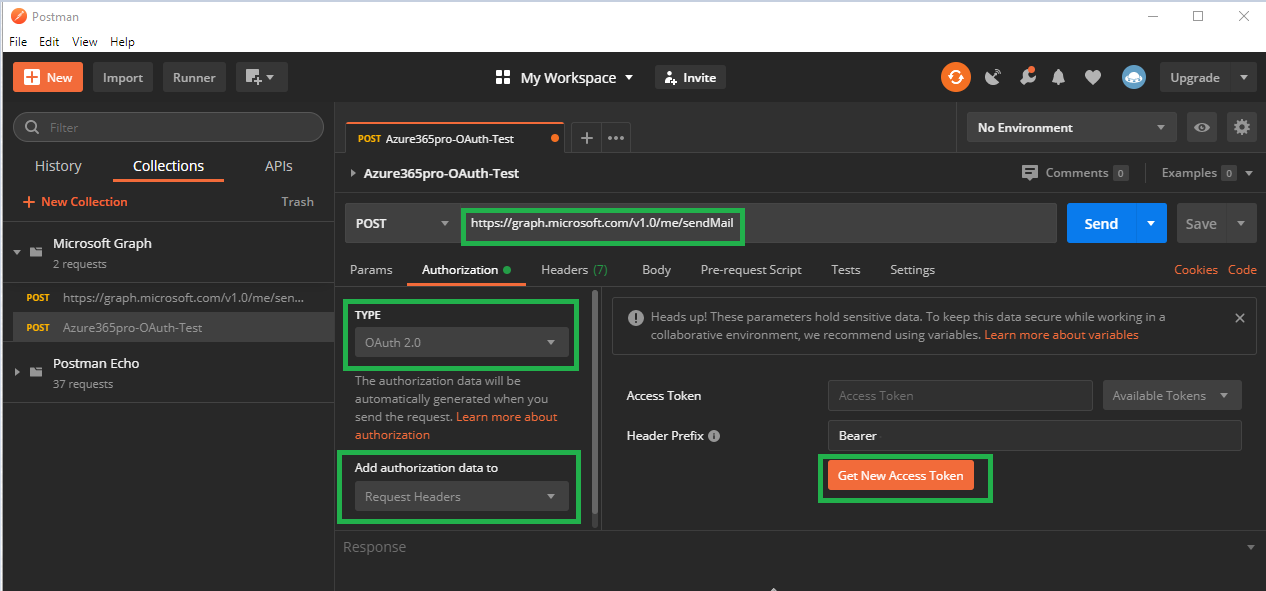
OAuth in simple words. You take the token and use the token to retrieve resources whenever you time. Until the token is valid and you can refresh the token whenever required.
lets see how to create a token
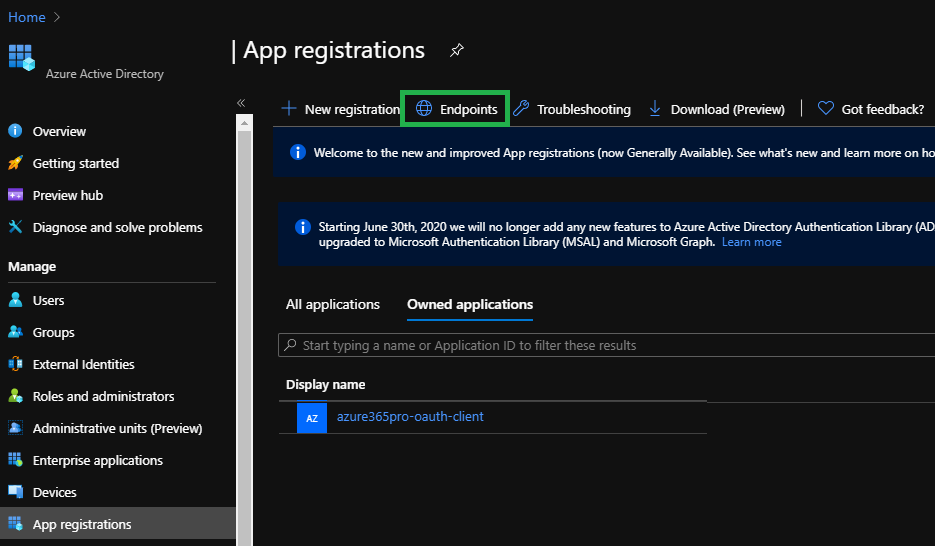
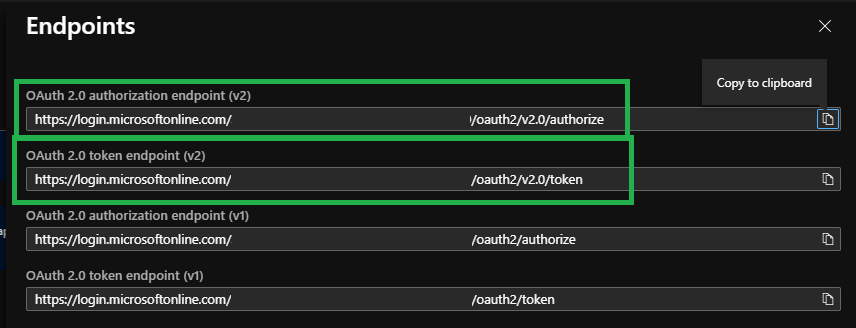
Choose Endpoints to get the required URLs
Auth URL = OAuth 2.0 authorization endpoint (v2)
Access Token URL = OAuth 2.0 token endpoint (v2)
Copy Both URLS
Copy Client ID
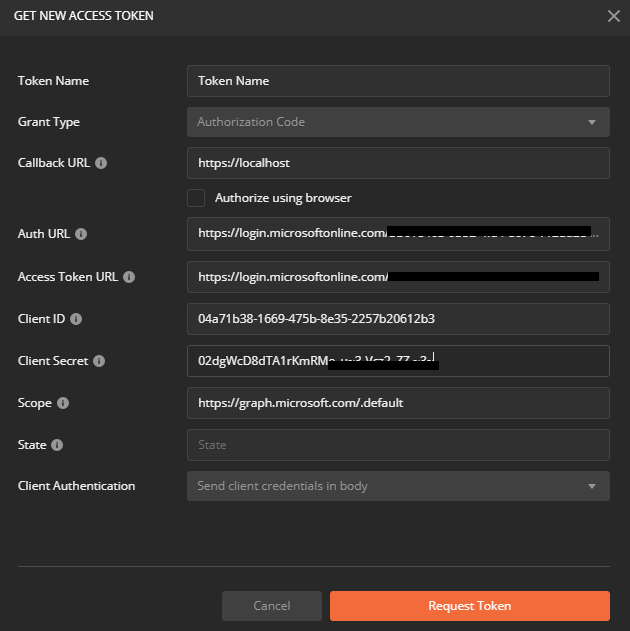
Request Token – Once you filled all the required information
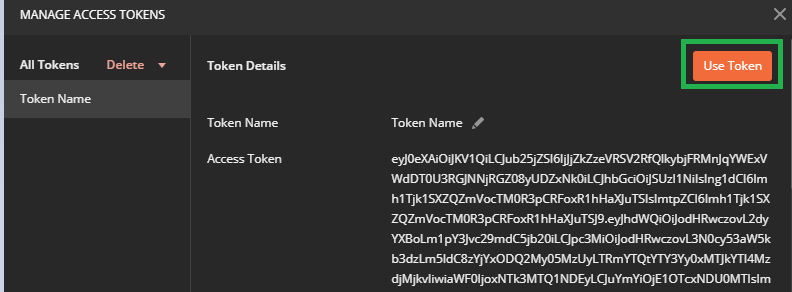
Now you have your
Token Name = Friendly Name
Grant Type = Authorization Code
Callback URL = https://localhost
Auth URL = OAuth 2.0 authorization endpoint (v2)
Access Token URL = OAuth 2.0 token endpoint (v2)
Client ID = (Get it from the Overview Tab like below)
Client Secret = (Get it from Certificates and Secrets Tab like above)
Scope = https://graph.microsoft.com/.default
State = State
Client Authentication = Send Client Credentials in body
Now once you request token it prompts for Microsoft Login so that you can authenticate with MFA.
Choose Use Token
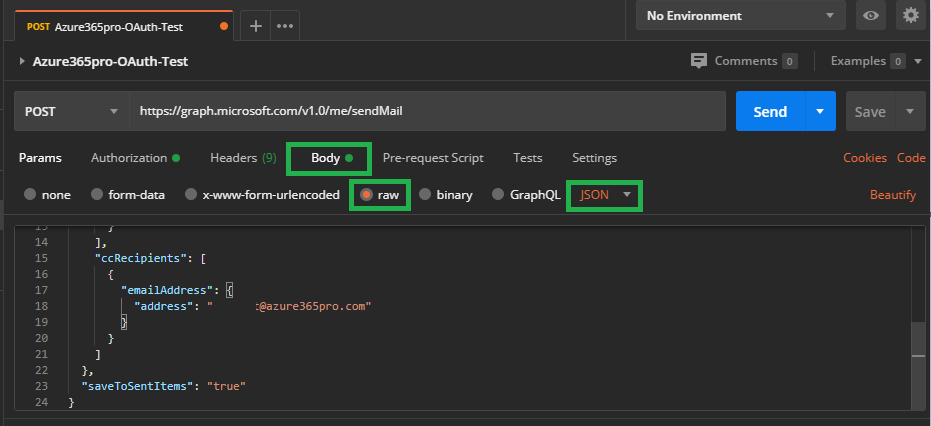
Lets take a sample json file fill in some sample email below (Microsoft Graph reference)
{
"message": {
"subject": "Email Through OAuth Azure365Pro",
"body": {
"contentType": "Text",
"content": "OAuth is Amazing"
},
"toRecipients": [
{
"emailAddress": {
"address": "xx@localhost"
}
}
],
"ccRecipients": [
{
"emailAddress": {
"address": "xx@localhost"
}
}
]
},
"saveToSentItems": "true"
}
Choose
Body
Raw
JSON
and Send
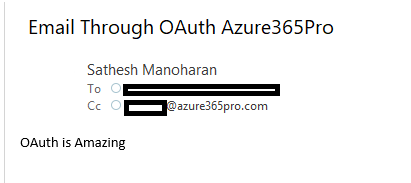
Now you can see the email in OnPrem Mailbox. You can see the value of Microsoft Graph you can use almost take any JSON payload and use it seamlessly.
Now We are in a good shape and utilizing Microsoft graph and in the same time verified OAuth Connectivity is healthy.
Verify OAuth is there in Authentication Methods in all On-Prem Exchange virtual directories
Get-MapiVirtualDirectory | FL server,*url*,*auth* Get-WebServicesVirtualDirectory | FL server,*url*,*oauth* Get-OABVirtualDirectory | FL server,*url*,*oauth* Get-AutoDiscoverVirtualDirectory | FL server,*oauth*
Make Sure OAuth is there in all virtual directories, Its there in default installations. Unless someone played around.
Confirm EvoSts Object exist. It is created by the hybrid wizard.
Get-AuthServer | where {$_.Name -eq "EvoSts"}
Now Schedule Maintenance Period as this is the type we need your front line teams to be equipped.
To Implement –
Set-AuthServer EvoSTS -IsDefaultAuthorizationEndpoint $true
Set-OrganizationConfig -OAuth2ClientProfileEnabled $true
To Rollback all users –
Set-AuthServer EvoSTS -IsDefaultAuthorizationEndpoint $false
Set-OrganizationConfig -OAuth2ClientProfileEnabled $false
Once users starts restarting Outlook Clients it requests them to Pass MFA or whichever if your Conditional Policy.
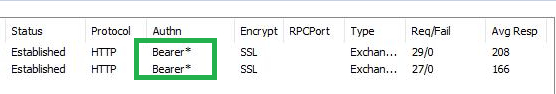
if you see “Bearer” you have been successfully moved from MAPI over HTTP to OAuth based Connectivity mechanism.
You can quickly rollback for all if you seeing most of users having issues.
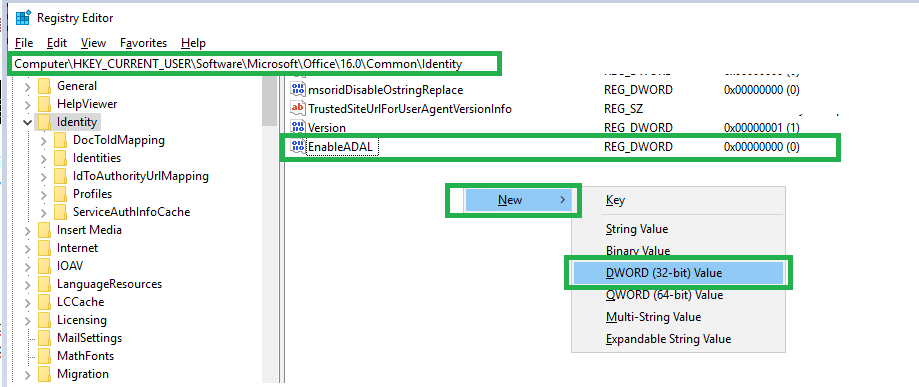
if you see very minimal clients having issues. you can rollback them with a client based registry.
Computer\HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\Identity
REG_DWORD 0
Every environment is different.Let us know how your transition went. if your not within proxy and all clients are Outlook for Office 365 with latest patches you can see good amount of success.If you all your clients are Outlook 2016 and Outlook 2013 and not well patched you cannot see much of success. All the best.