What we learned so far:
- AWS IAM is global and not limited to any specific region
- Root account is the account through which we signed up for AWS account and by default it has full access to all the services and resources. It is also required to configure MFA for security purpose.
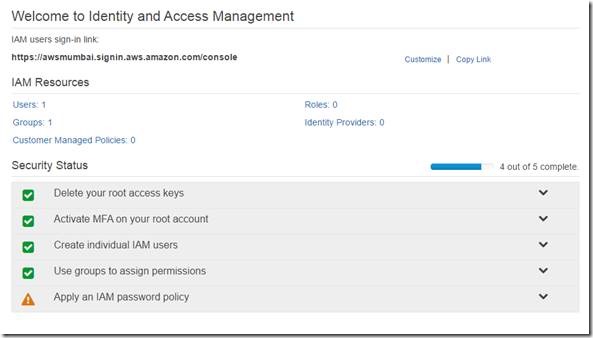
Now that we have understood IAM being a centralized control of your AWS account. Configuring MFA (multi-factor authentication) is one of the mandatory steps for the root account else we notice it shows as a pending task out of the 5 security step. We have successfully configured in previous article
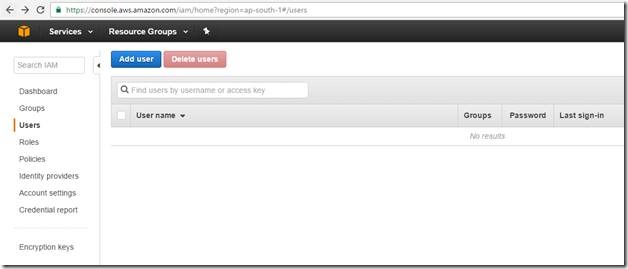
IAM consist of Users, Group, Roles & policy documents and further we will understand more how to configure those & use it. After setting up the multi-factor authentication (MFA) on AWS root account we will further create User and Group so that we can delegate AWS service & resources access to dedicated authorized users.
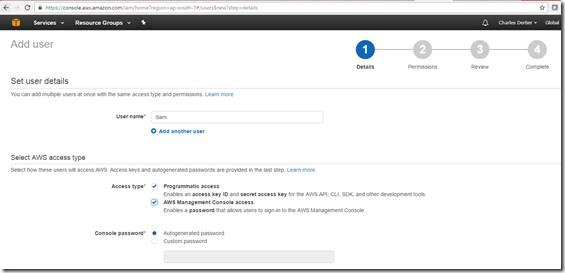
Let us use “SAM” as a new user and below you will find two access type option.
1. Programmatic Access – User needs access key ID and secret access key to access the AWS service using API, CLI, SDK and other development tools.
2. AWS Management Access Console – User needs password to login using web AWS management console
While creating user you could also create more than one users and assign option to change password at first sign in. If you notice there are two access type
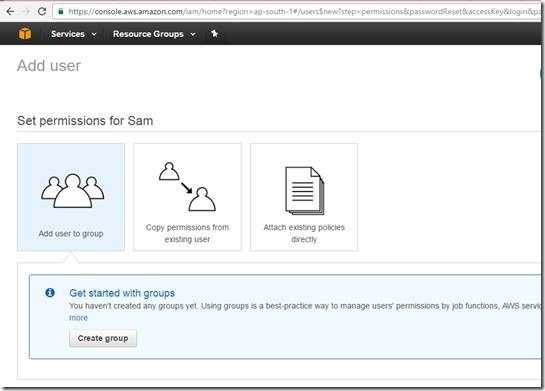
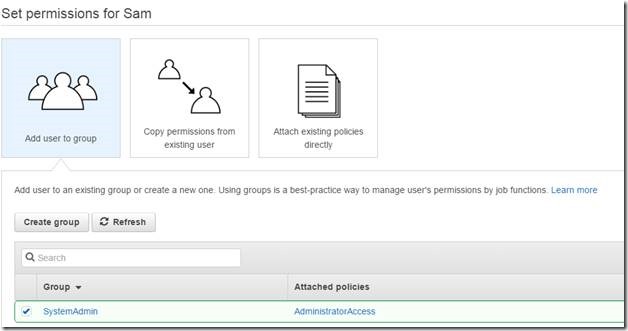
Instead of assigning the AWS services directly to the users let’s create custom group and add users to it which is a best practice. You might want to create groups based on the organization requirement and delegation purpose like HR, System Admin, Finance etc. As a group the policies are applied to users
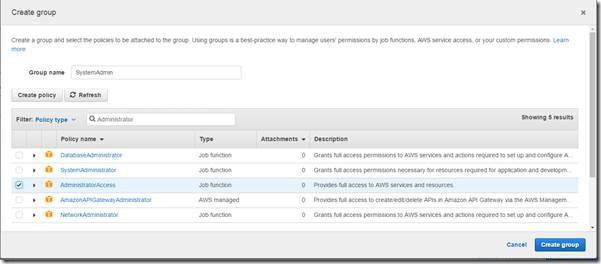
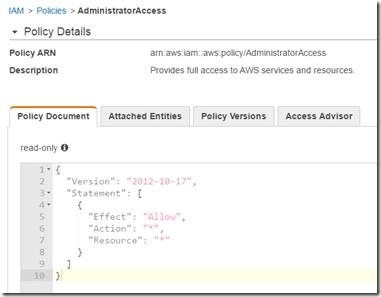
We will create a group called “SystemAdmin” and assign policy “AdministratorAccess” to manage AWS services. Policy document is set of permissions which are assigned to group & any users who are member of the group inherits the permission. Policy document “AdministratorAccess” as mentioned below provides full access to AWS services and resources.
You can drill down to see the code (Jason format) which details attributes and its value. If you are developer you will love to read this and look for other policy documents too.
- Attributes – versions, statement, effect, action & resource
- Values – date, Allow, *(wildcard)
User is added to the Group – “SystemAdmin”
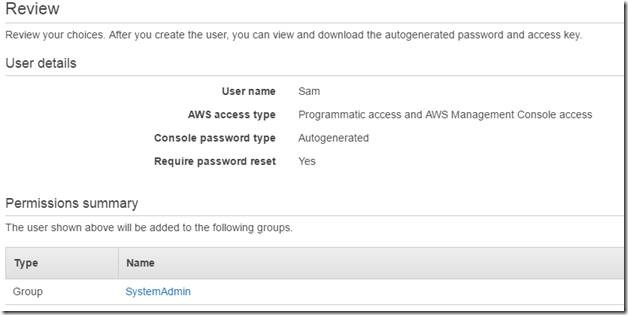
Review the summary
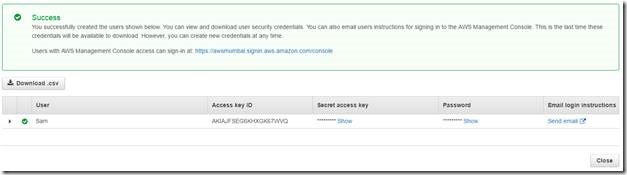
After clicking on create you will see the below details. Since we have selected both the access type; user is assigned not only with Access Key ID, Secret Access Key but also with password to access AWS services and resources using programmatic as well as via management console
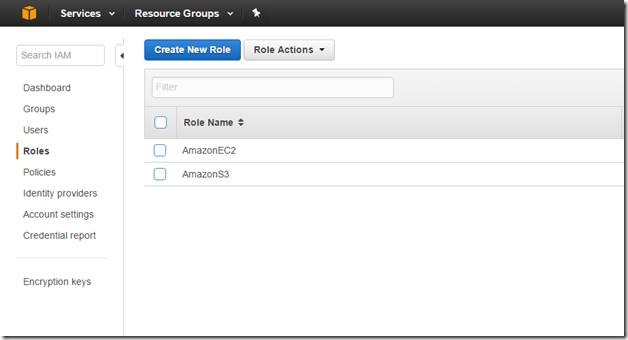
Let’s understand roles, it is just a set of permission that grants access to actions and resources in AWS. It allows one service to interact with another AWS service and in further article we will understand more about roles.
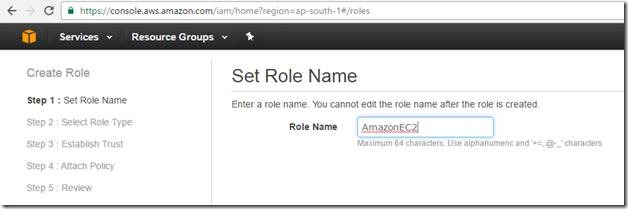
Let us create a role called “AmazonEC2”
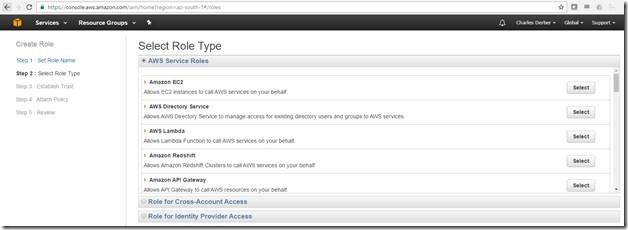
Select AmazonEC2 service under role type under AWS service roles and click on select
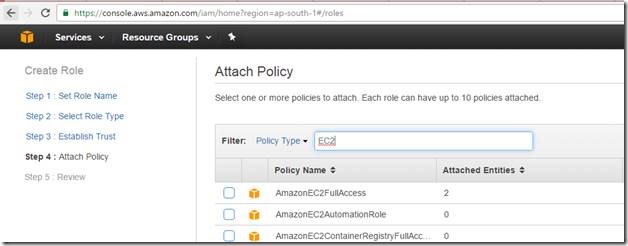
Select the policy AmazonEC2FullAccess & click on next step.
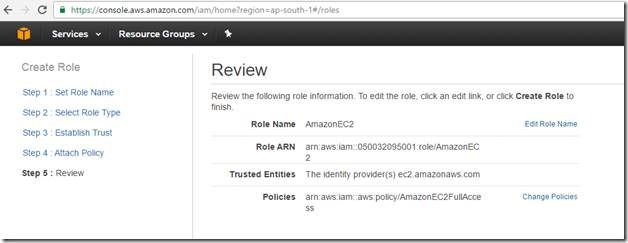
Review the role summary
Now the role is created and available as mentioned below. Working with role is again a vast topic we will see in further articles.
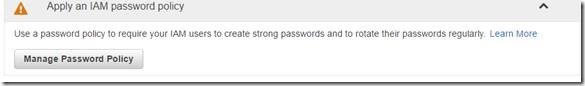
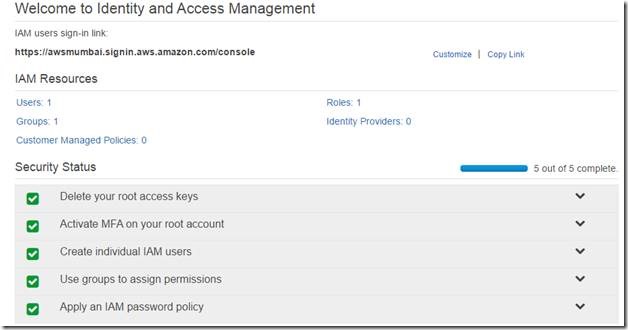
Now that we have created role lets finish the last part of the security status i.e. configure and apply IAM password policy.
Click on manage password policy
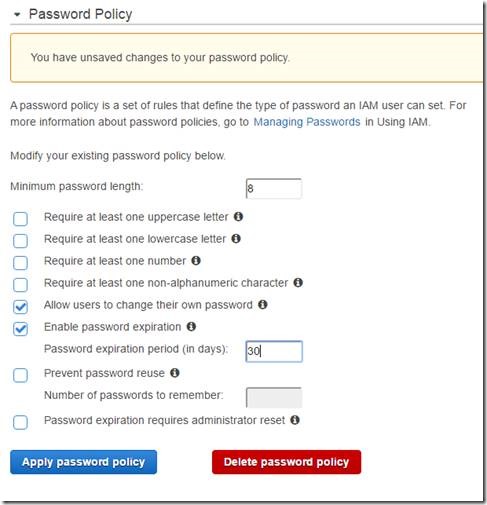
Below is the default option and let’s modify as your requirement, in my case I had updated password length with 8 and enabled password expiration to 30days.
Below is the security status which shows that we completed the 5 out of 5 steps complete.
Let’s summarize:
- New users have no permission by when created and hence Administrator must assign permission to access AWS services and resources.
- Access Key ID and Secret Key are different from Password and used for different purpose for example access type called Programmatic and Management Console. You cannot use password to do programmatic Access type & key ID/Secret Key to do Management console access.
- Configure MFA at least on your AWS root account for security purpose.
- You can create your own password policies under AWS IAM as per your requirement.
This is not the end of AWS IAM, there is lot to learn and deep dive on this topic but we have gone through the overview and a quick hands-on. We will explore more in the coming articles so stay tuned.





Nice Article. How it help to developer in terms of balance the day to day life.
Very nice article! Thanks for it! I have experienced this support firsthand at the annual conference and as a member of the national medical student committee
Good blog article about aws course.
icecreamhaven vanilla A smooth, creamy flavor that’s simple yet satisfying. Perfect on its own or as a base for toppings.
“The attention to detail on this site is impressive. Every aspect is carefully thought out and executed.”