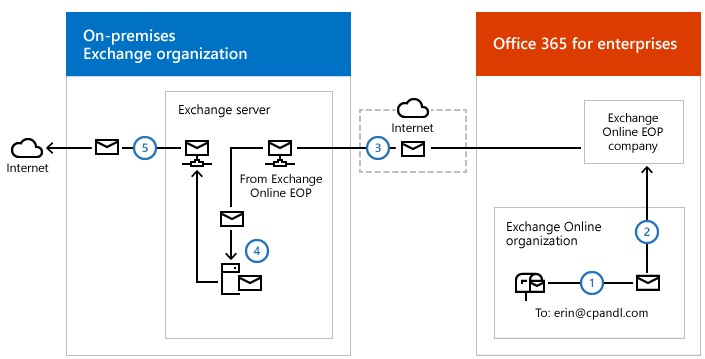
We love third-party software for centralized signatures because of the capability which they provide which we couldn’t achieve in Exchange Natively nor Office 365 till over the past decade. Signature software’s started providing cloud capabilities to route the email to their cloud to get them stamped. But some companies don’t want to route the email to their third-party cloud due to security and regulatory reasons even though they provide confidence saying they go via the same Azure infrastructure which is totally understood. Also, government agencies don’t want to route their email into a different country just for signatures even they wish to consume what the cloud provides them. As technology evolves in the Microsoft Graph space we have to wait for the options on how a signature can be applied to the mail transport layer without routing the whole email to different infrastructure.
To work around this situation, We can utilize the On-premises Exchange servers which are in hybrid to stamp the signature for Office 365 Internal Mail flow by creating a transport rule with additional headers. let’s see how to implement them.
You need to rerun the Hybrid wizard and enable centralized transport in order to achieve it. The most important thing before you need to enable centralized transport is if your MX is still pointing to On-premises servers your Office 365 groups will stop working if you are not using a dedicated group domain as it doesn’t currently support hybrid even though having group writeback enabled.
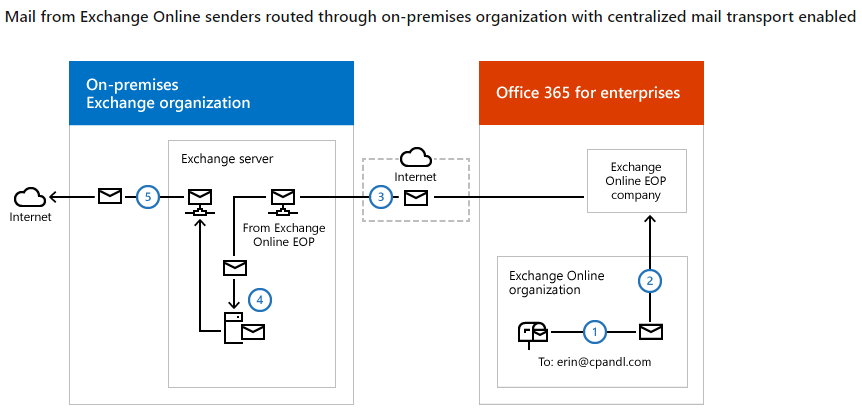
So you have to give up Office 365 groups, or you need to plan to move your MX to cloud or you need to have a dedicated group domain for office 365 groups so that it doesn’t need to come through this. Also, you have to understand that your Office 365 mail flow is going to pass through these servers. make sure you’re on-prem servers have enough juice. all your objects have to be synced and a proper hybrid should be in place. as the cloud object should be there in on-prem to give the email back to office 365.
We need a dedicated connector where the custom transport rule can use it. In order to forward the internal office 365 mail flow to the On-premises server for signatures. In simple words, we are adding a header value and divert all the office 365 emails to on-prem and on-prem object has a target address to the cloud and transport rule will not apply while it’s coming back. while it comes back the signature software on the exchange servers stamps the signature on the email as it’s on the transport layer.
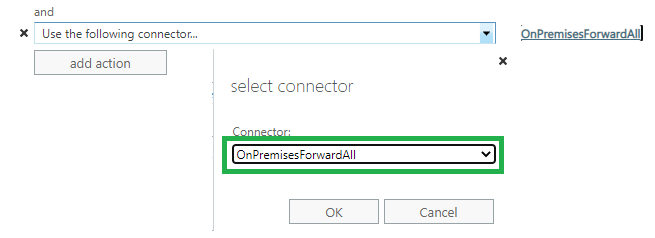
OnPremisesForwardAll is the Connector we created. Sharing all the connectors. so that you will get an understanding of how all the connectors fall into space in a hybrid scenario with default connectors in place.
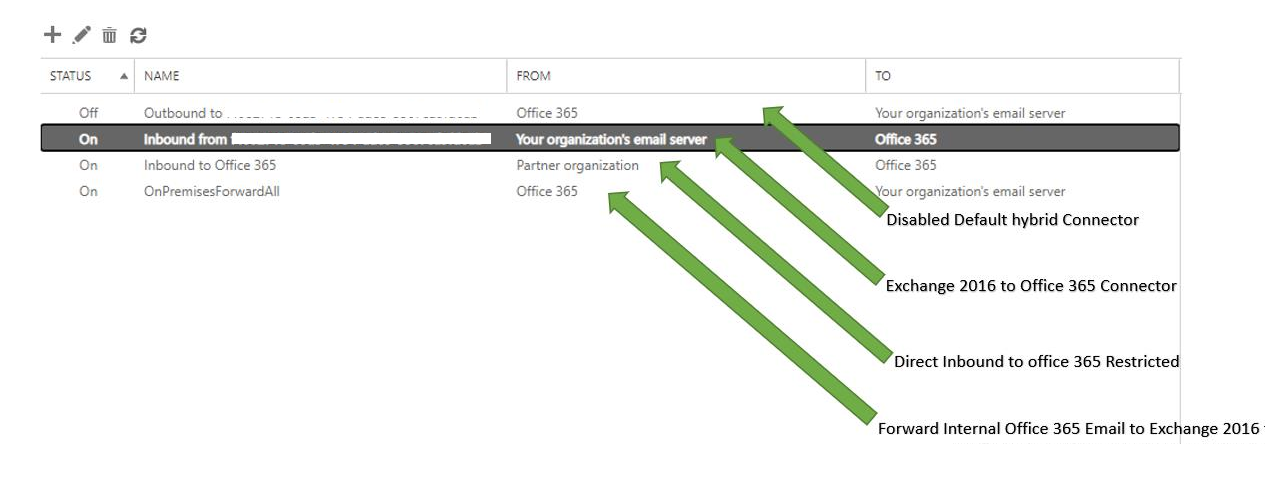
Let’s create the OnPremisesForwardAll connector before we create the transport rule.
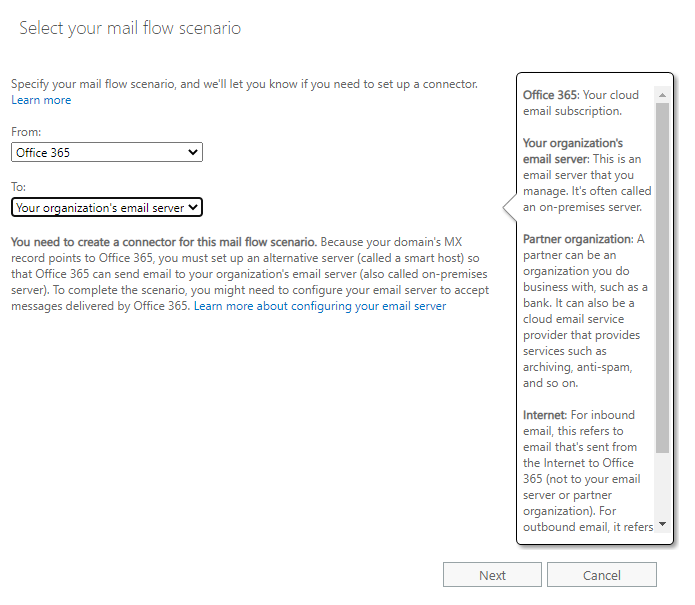
exchange online – ECP – connectors – create a new connector –
Choose From Office 365 – Your Organizations email server
new connector
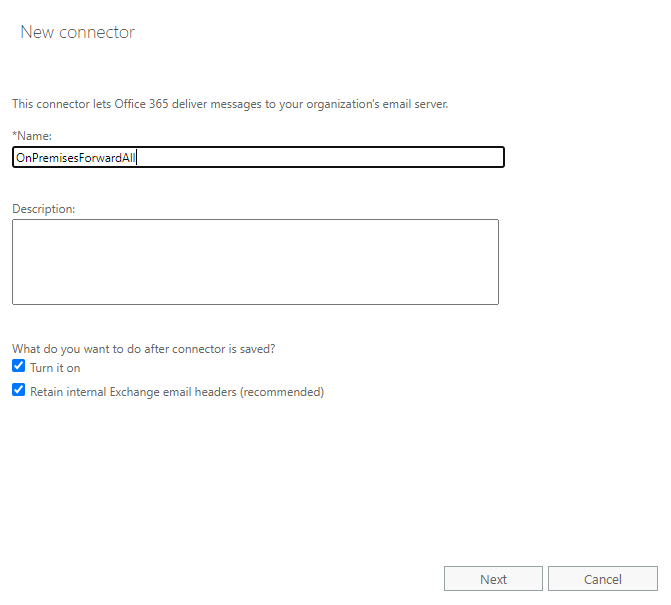
Only when I have a transport rule set up that redirects messages to this connector
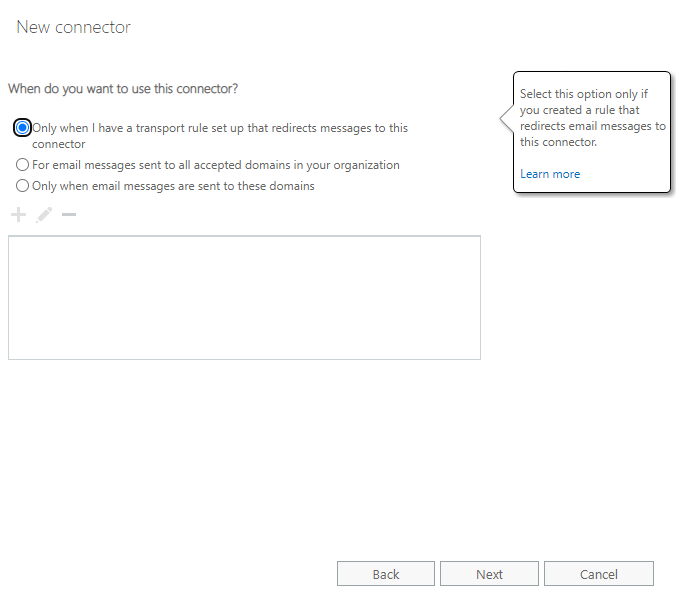
How do you want to route email messages? your hybrid server public IPs
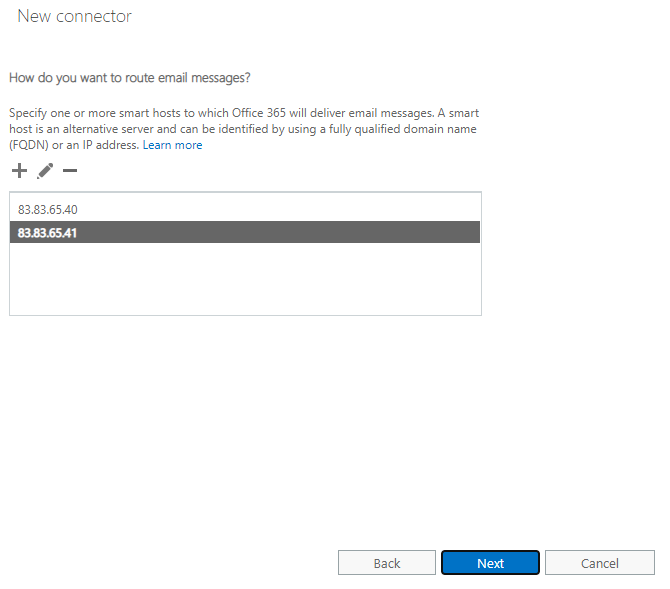
always to transport layer security with proper SSL in place
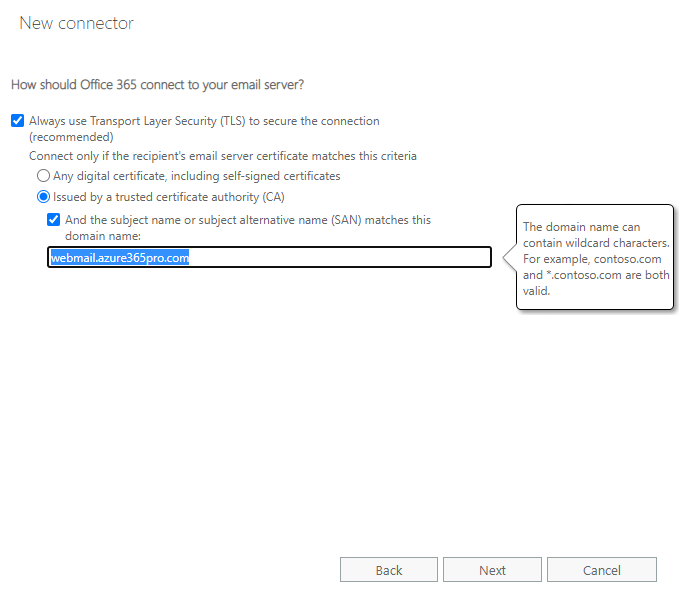
Next and Save the Connector.
Now let’s create a transport rule to use the connector
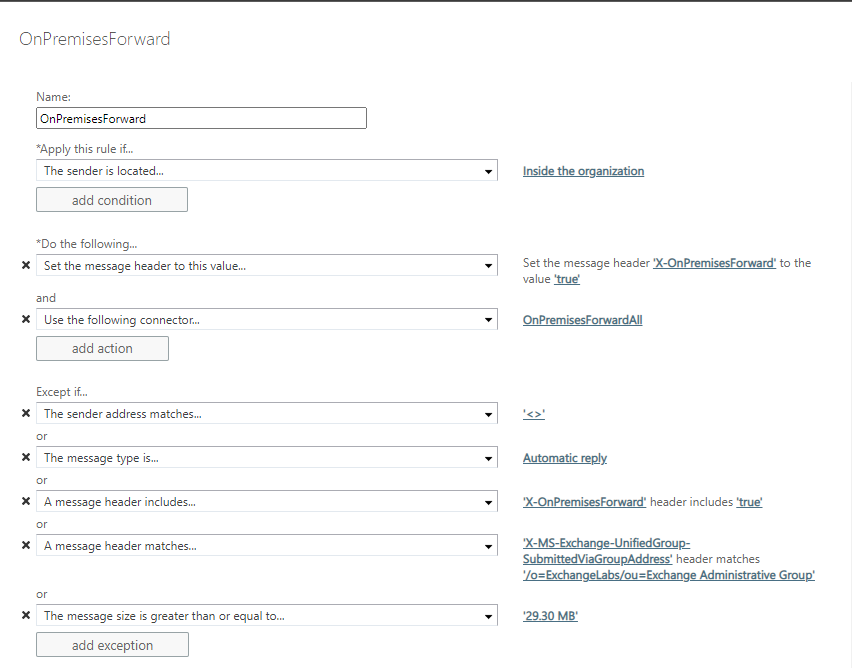
Added an exception for the message type automatic Reply. Otherwise out of office messages will not work within office 365 users.
Name – OnPremisesForward
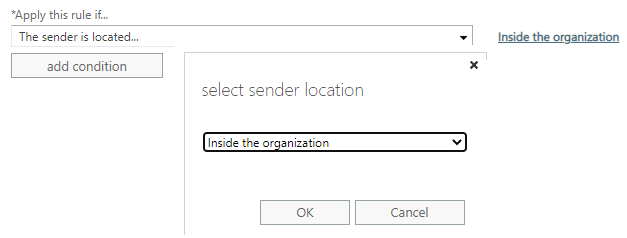
The sender is located “Inside the Organization”
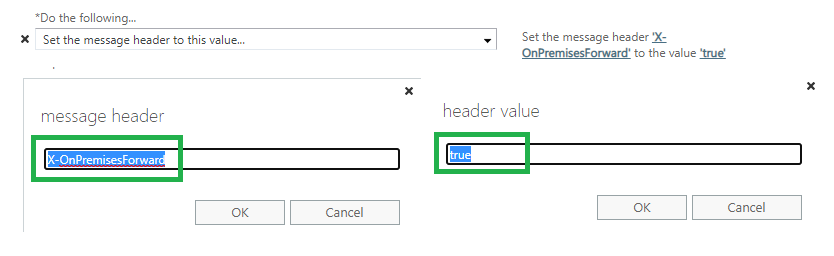
Set the message header to this value X-OnPremisesForward to the value true
Use the following connector
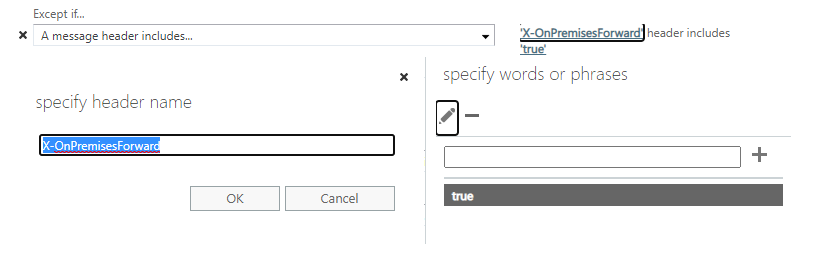
Except if
a message header includes X-OnPremisesForward
you need this – otherwise, your planner comments will be added with signatures which may look a bit ugly.
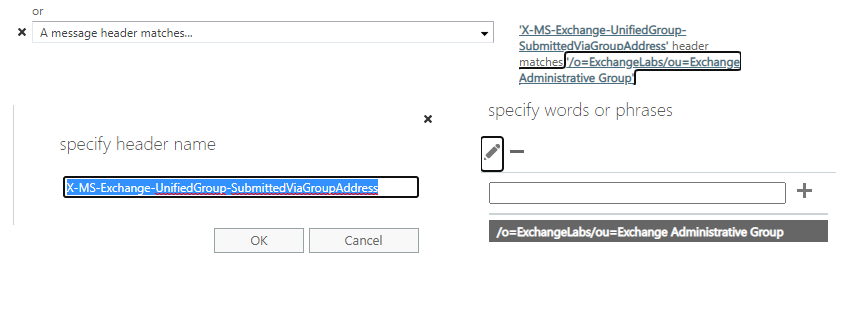
or
a message header matches
X-MS-Exchange-UnifiedGroup-SubmittedViaGroupAddress matches /o=ExchangeLabs/ou=Exchange Administrative Group
Now all your Office 365 users and On-Prem users are stamped with the same signature without the email getting routed elsewhere.


CodeTwo Email Signatures for Office 365 adds signatures for people with mailboxes in your Office 365 tenant since the software is optimized for Office 365. CodeTwo Exchange Rules adds signatures for people with mailboxes on the on-premises part of your environment since all emails originating from there are processed using Exchange Transport Service, to which the CodeTwo software is connected.