The service Principal requires more permission on few cases in Azure. But it doesn’t apply to all in this case. as the security model differs for the environment. Below is a scenario that vnet peering is failing on terraform as both the vNETs are managed by the same DevOps Project.
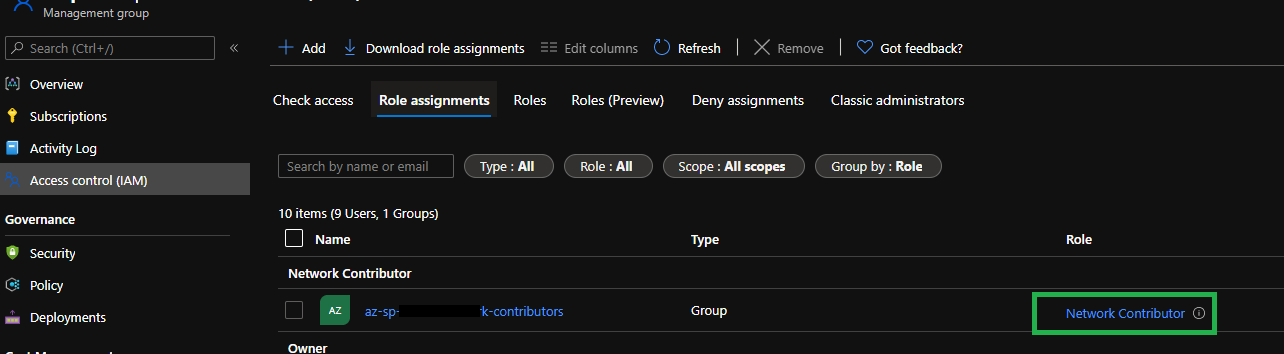
Search for Management Groups which are associated – Add all these service principals to a security group and then Add them to the network contributor role on the specific management group.
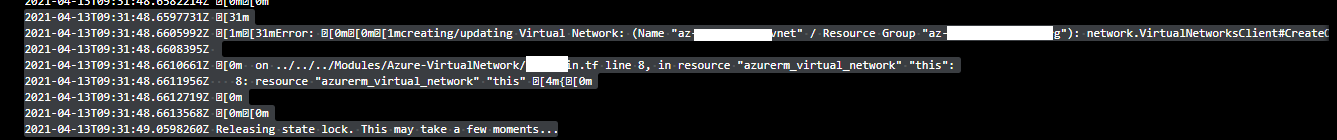
2021-04-13T09:31:48.6597731Z [31m
2021-04-13T09:31:48.6605992Z [1m[31mError: [0m[0m[1mcreating/updating Virtual Network: (Name "az-mw-pr-uaen-vnet" / Resource Group "az-mw-pr-uaen-net-rg"): network.VirtualNetworksClient#CreateOrUpdate: Failure sending request: StatusCode=0 -- Original Error: Code="NetcfgInvalidSubnet" Message="Subnet 'mw-pr-uaen-waf-snet' is not valid in virtual network 'az-mw-pr-uaen-vnet'." Details=[][0m
2021-04-13T09:31:48.6608395Z
2021-04-13T09:31:48.6610661Z [0m on ../../../Modules/Azure-VirtualNetwork/1.5/main.tf line 8, in resource "azurerm_virtual_network" "this":
2021-04-13T09:31:48.6611956Z 8: resource "azurerm_virtual_network" "this" [4m{[0m
2021-04-13T09:31:48.6612719Z [0m
2021-04-13T09:31:48.6613568Z [0m[0m
2021-04-13T09:31:49.0598260Z Releasing state lock. This may take a few moments...
Add Network Contributor level on the management group in my case. in your case, it could be your resource group / virtual network level. whichever suits your environment.
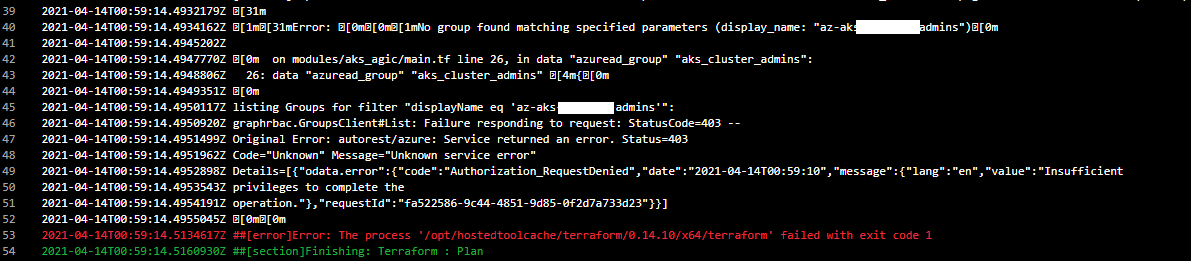
2021-04-14T00:59:14.4932179Z [31m
2021-04-14T00:59:14.4934162Z [1m[31mError: [0m[0m[1mNo group found matching specified parameters (display_name: "az-aks-admins")[0m
2021-04-14T00:59:14.4945202Z
2021-04-14T00:59:14.4947770Z [0m on modules/aks_agic/main.tf line 26, in data "azuread_group" "aks_cluster_admins":
2021-04-14T00:59:14.4948806Z 26: data "azuread_group" "aks_cluster_admins" [4m{[0m
2021-04-14T00:59:14.4949351Z [0m
2021-04-14T00:59:14.4950117Z listing Groups for filter "displayName eq 'az-aks-cluster-admins'":
2021-04-14T00:59:14.4950920Z graphrbac.GroupsClient#List: Failure responding to request: StatusCode=403 --
2021-04-14T00:59:14.4951499Z Original Error: autorest/azure: Service returned an error. Status=403
2021-04-14T00:59:14.4951962Z Code="Unknown" Message="Unknown service error"
2021-04-14T00:59:14.4952898Z Details=[{"odata.error":{"code":"Authorization_RequestDenied","date":"2021-04-14T00:59:10","message":{"lang":"en","value":"Insufficient
2021-04-14T00:59:14.4953543Z privileges to complete the
2021-04-14T00:59:14.4954191Z operation."},"requestId":"fa522586-9c44-4851-9d85-0f2d7a733d23"}}]
2021-04-14T00:59:14.4955045Z [0m[0m
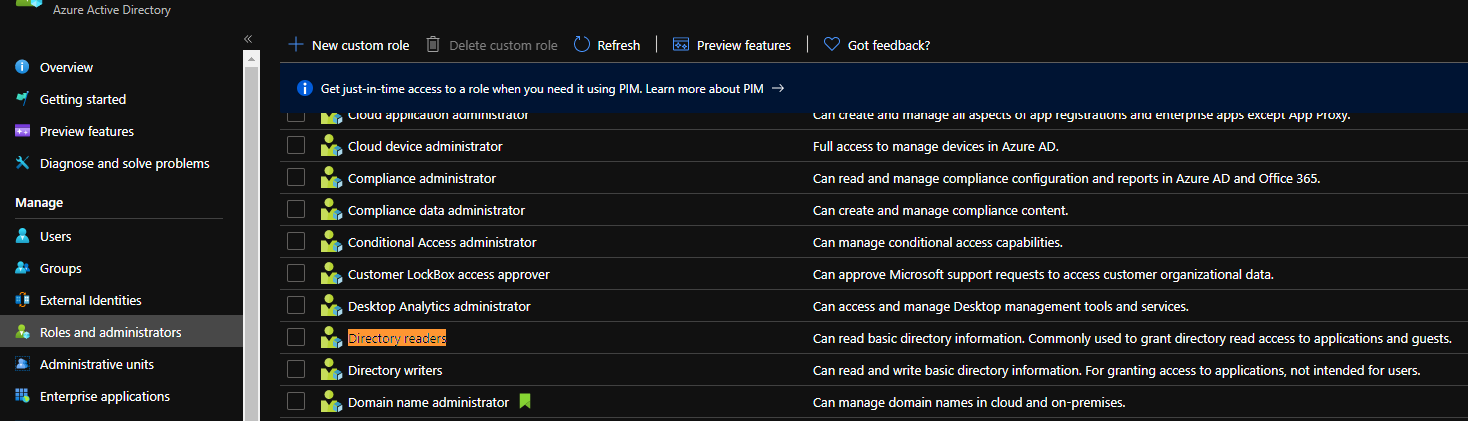
Add the service principles used in – Directory Readers group
Which should allow reading azure ad groups