Send Email from an Application using Microsoft Graph and Microsoft 365 shared mailbox without an logged in user.
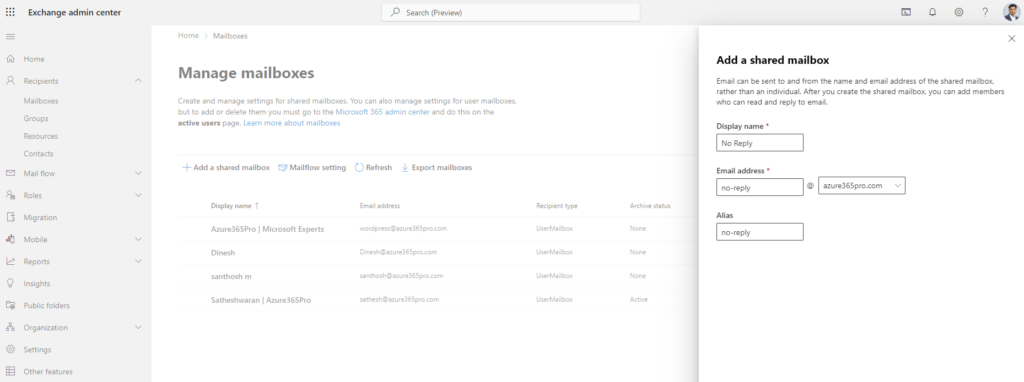
Log into Exchange Admin center and create a shared mailbox.
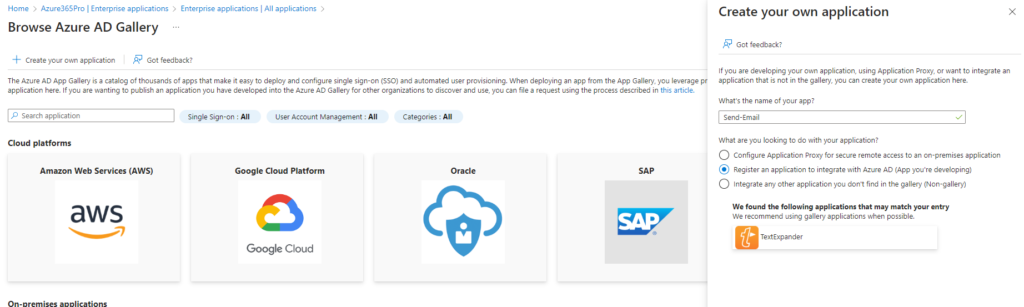
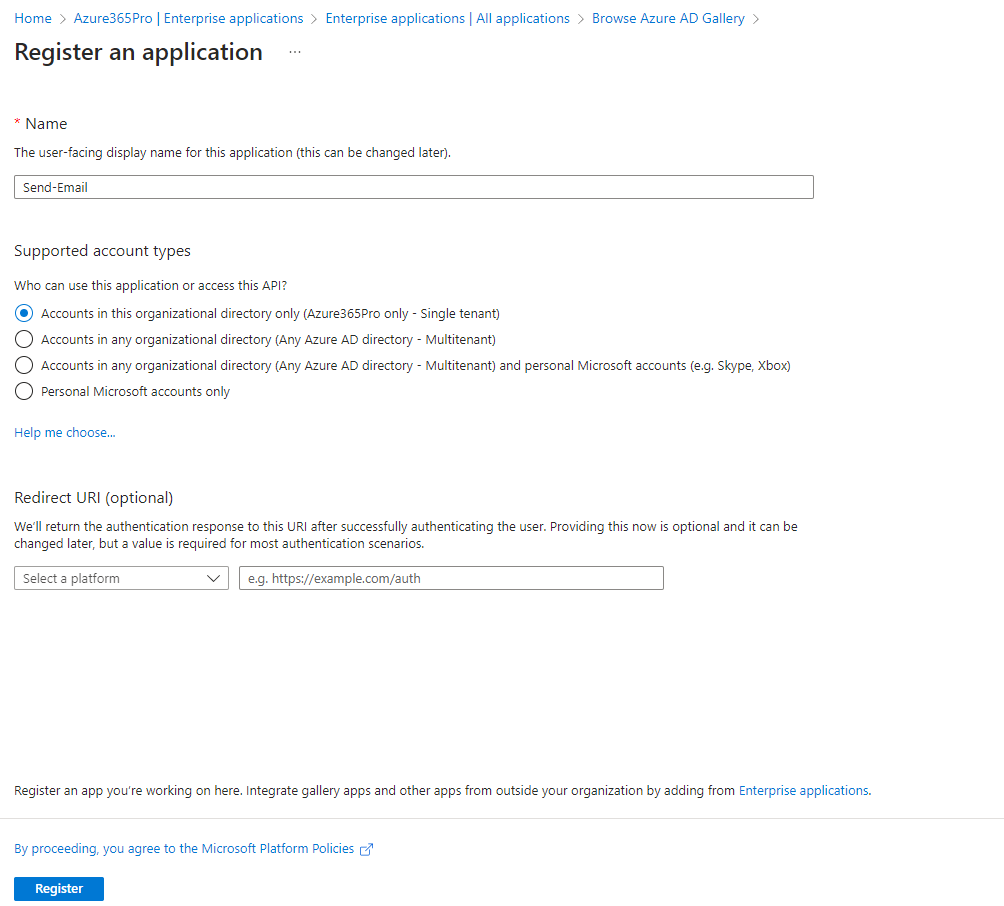
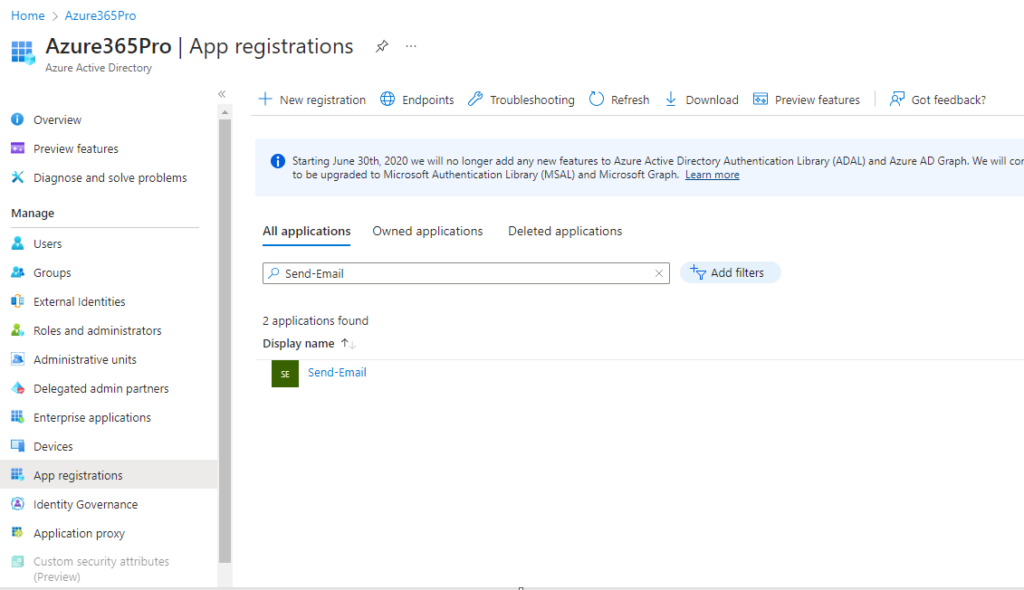
Create an Enterprise Application
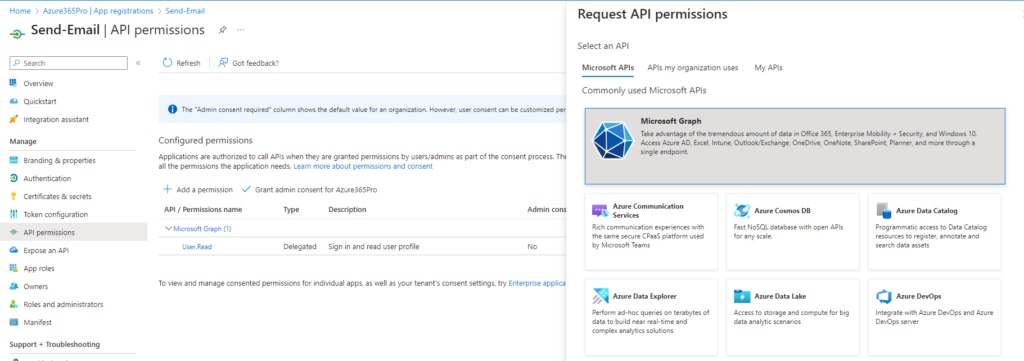
Choose Microsoft Graph
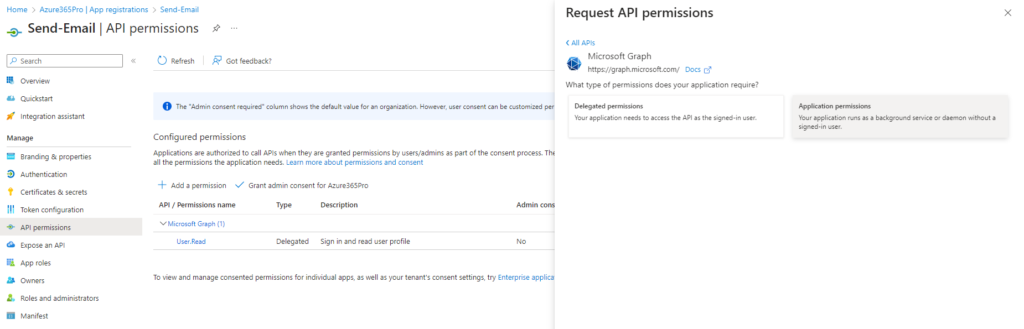
Choose Application
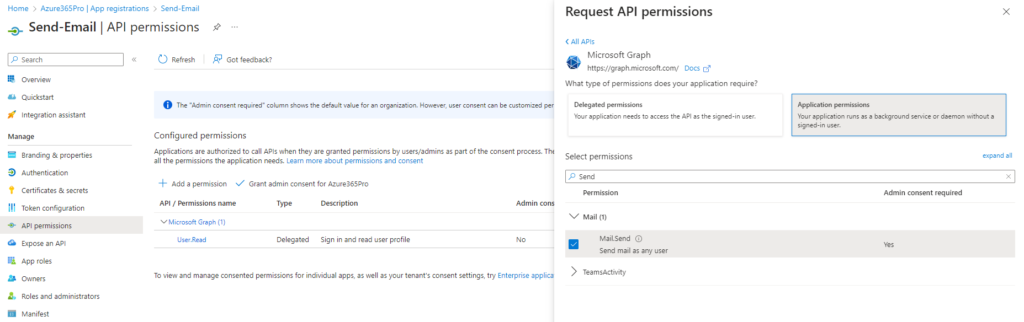
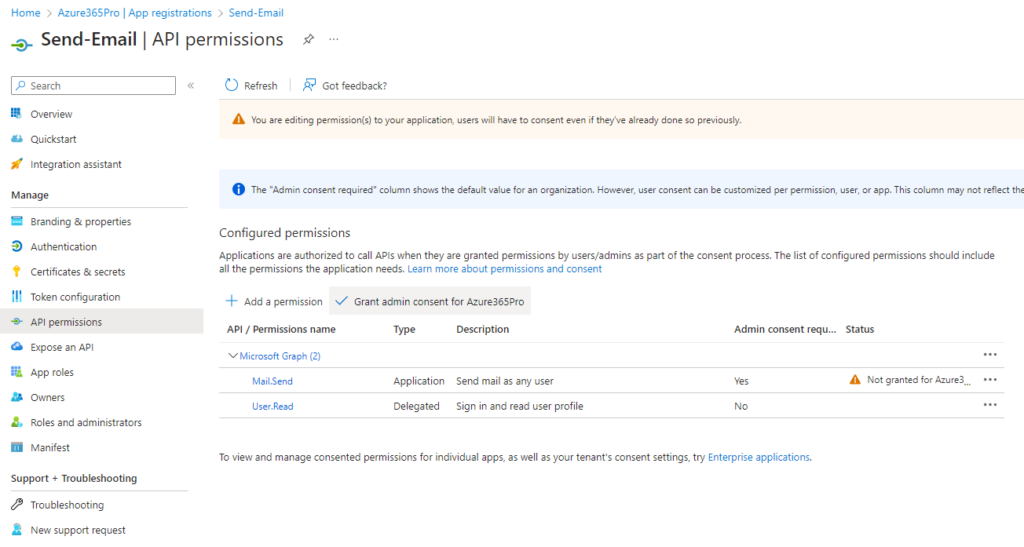
Add Mail.Send Permission
Grant Admin Consent
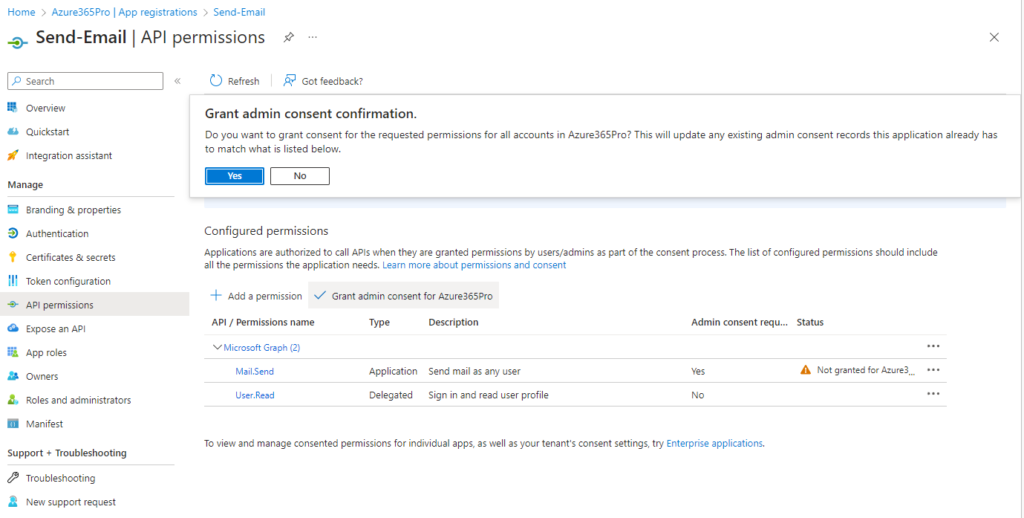
Grant Admin Consent Confirmation
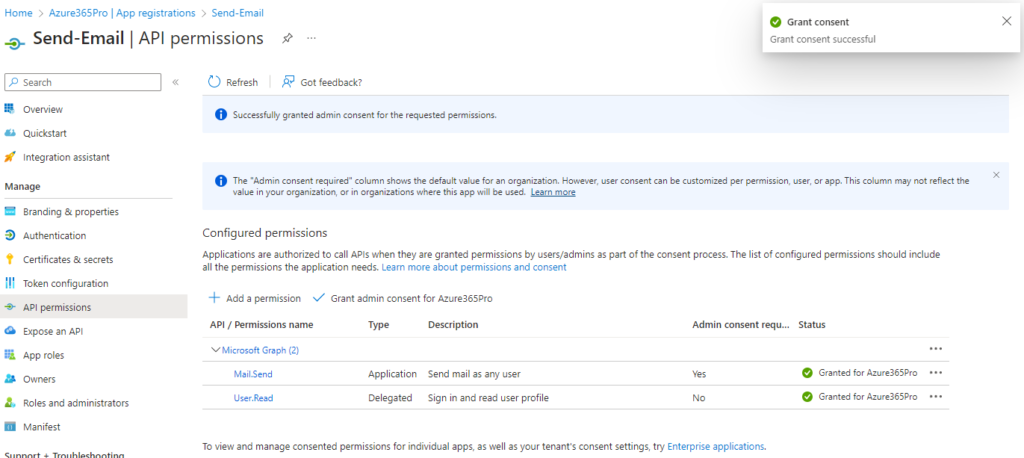
Grant is successful
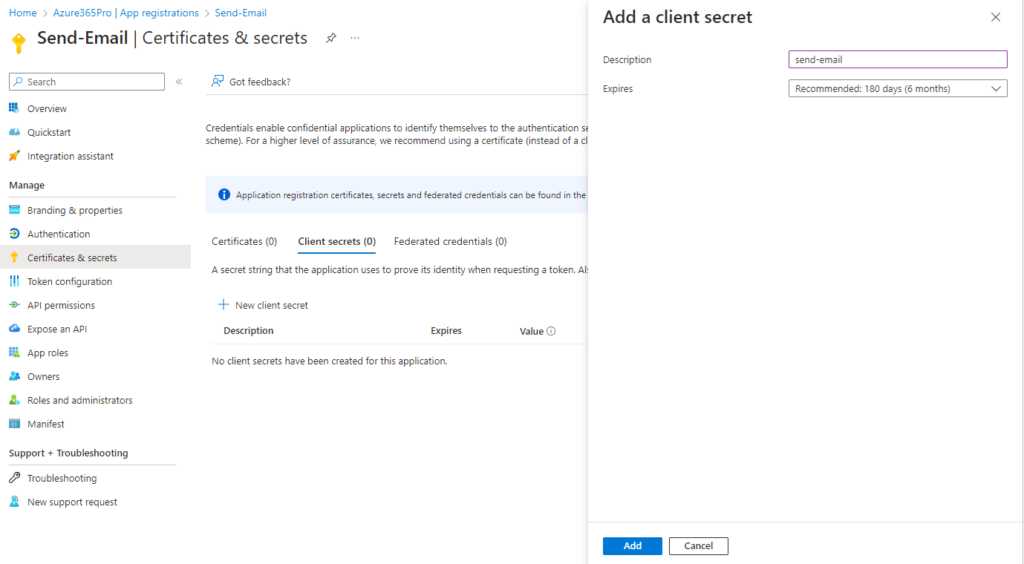
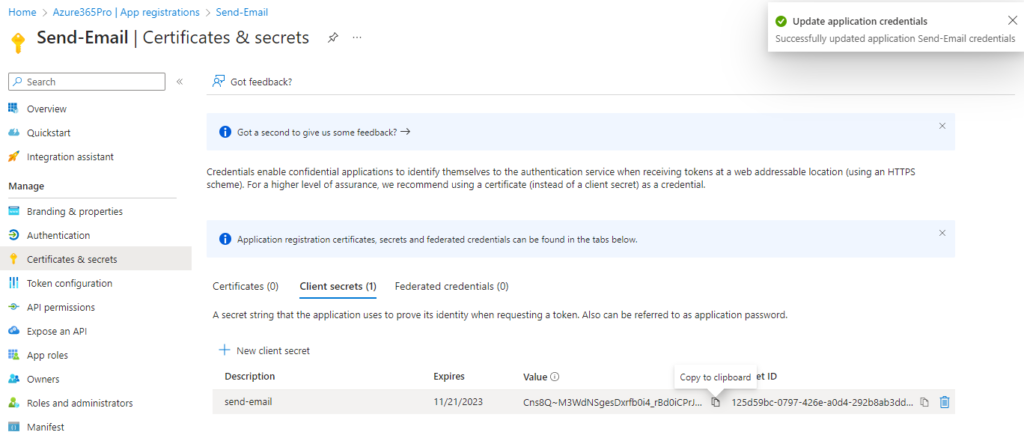
Create a Secret
Copy the secret and keep in a notepad
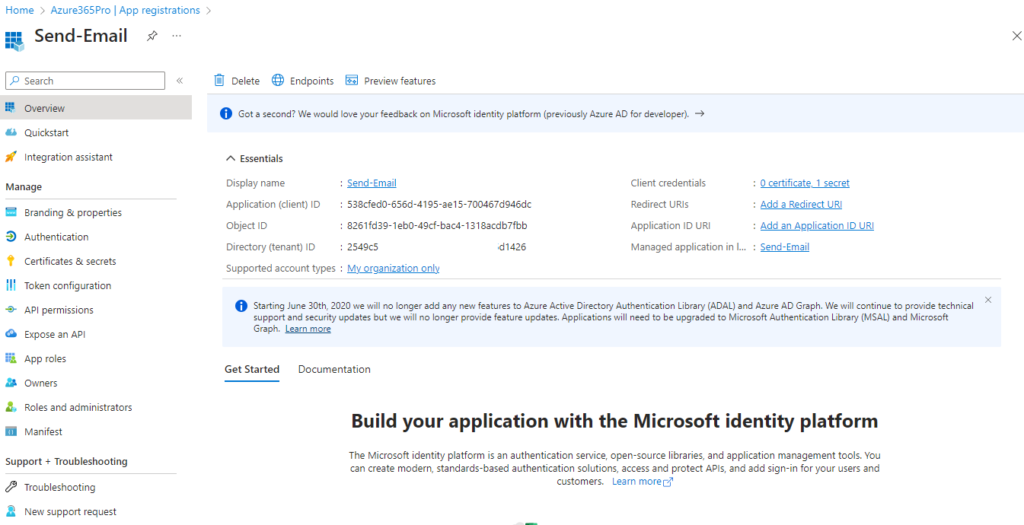
Collect your Client ID – Application (Client) ID
There are two steps – Take Token – then use the token to send email.
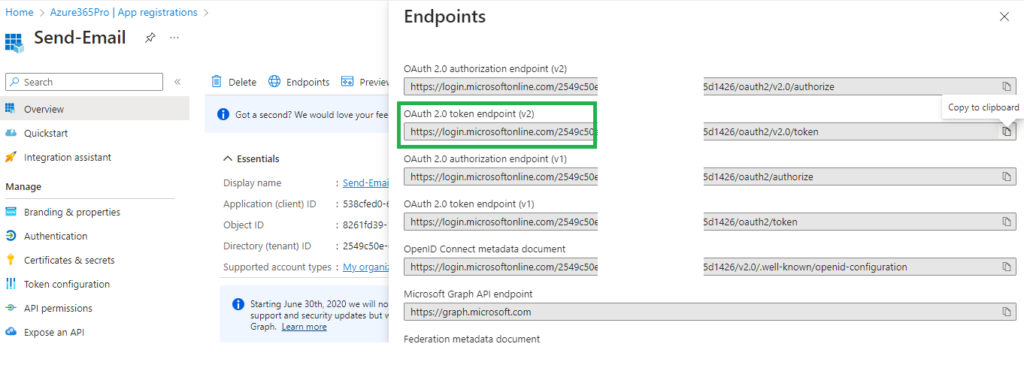
Use Postman to get Token.
| grant_type | client_credentials |
| client_id | 538cfed0-656d-4195-ae15-700467d946dc |
| client_secret | Cns8Q~M3WdNSgesDxrfb0i4_rBd0iCPrJg_kodjY |
| scope | https://graph.microsoft.com/.default |
Download Postman 64 Bit and install on Windows or Mac
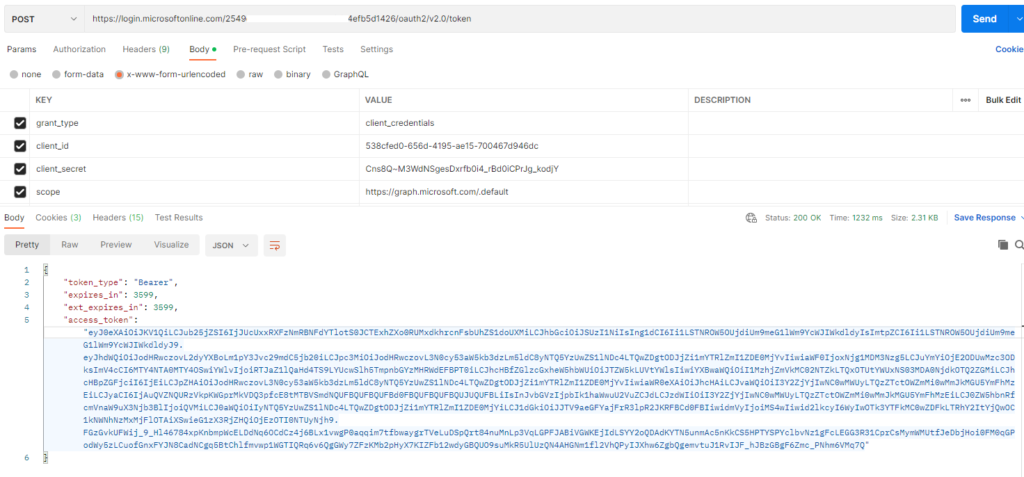
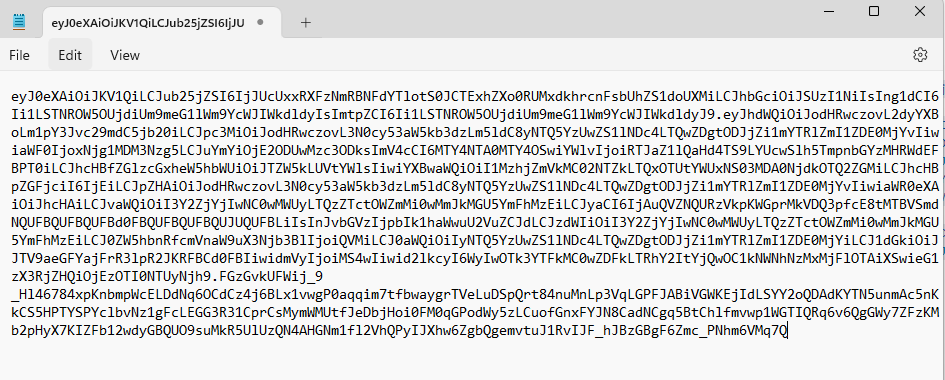
Copy the Access Token – Take it without double quotes
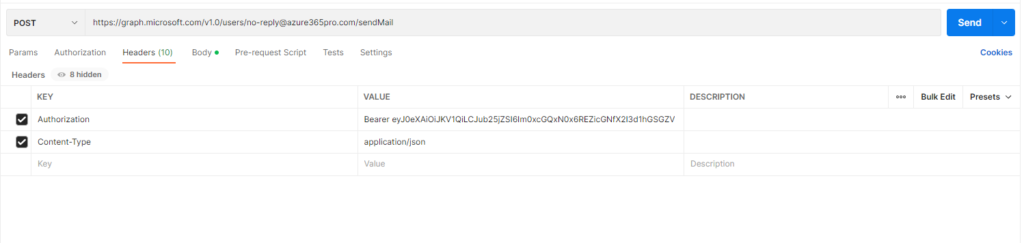
Now lets POST on graph url to send some test emails. Put this as Headers
| Authorization | Bearer REPLACE-WITH-TOKEN-VALUE-WITHOUT-QUOTES |
| Content-Type | application/json |
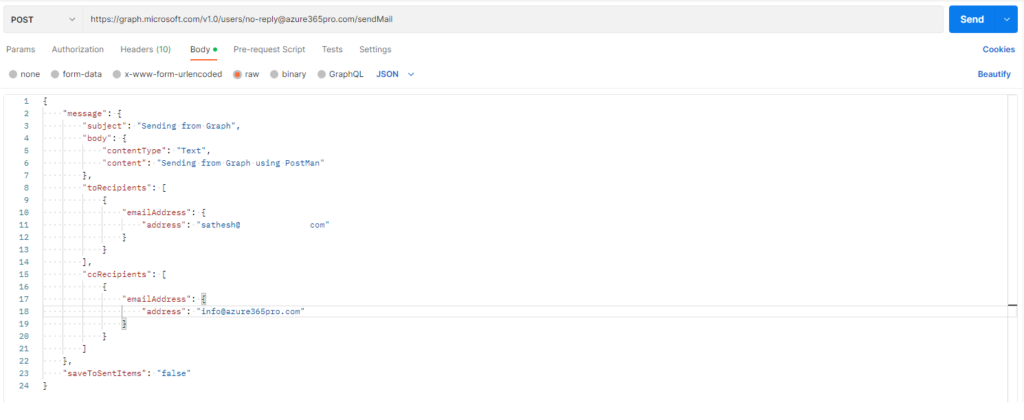
{
"message": {
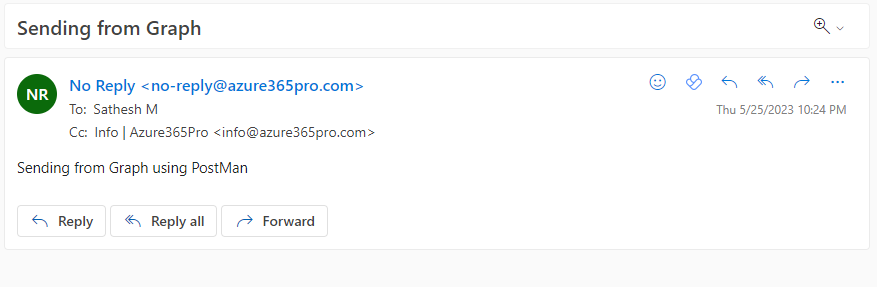
"subject": "Sending from Graph",
"body": {
"contentType": "Text",
"content": "Sending from Graph using PostMan"
},
"toRecipients": [
{
"emailAddress": {
"address": "sathesh@azure365prox.com"
}
}
],
"ccRecipients": [
{
"emailAddress": {
"address": "info@azure365pro.com"
}
}
]
},
"saveToSentItems": "false"
}
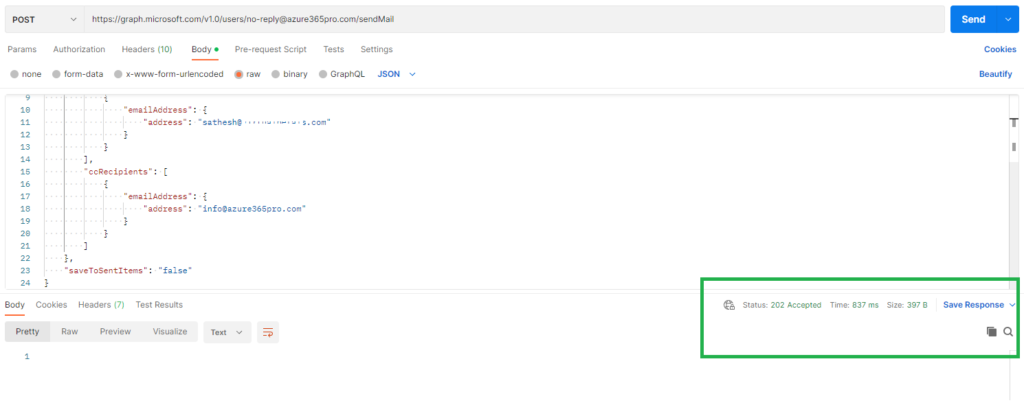
Email is generated
If the scope of permission is wide. In Enterprise scenario you can harden it using New-ApplicationAccessPolicy which i have explained in this article to reach attachments using Graph. Access Specific Office 365 Mailbox using Microsoft Graph – Azure365Pro.com