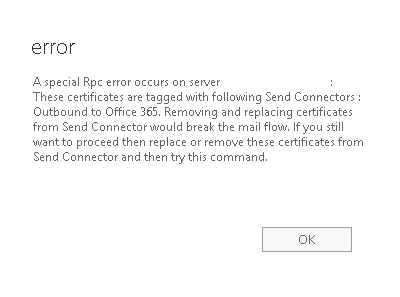
A particular Rpc error occurs on server EXCH1: These certificates are tagged with Send Connectors: Outbound to Office 365. Removing and replacing certificates from Send Connector would break the mail flow. If you still want to proceed, then replace or remove these certificates from Send Connector and then try this command.
$cert = Get-ExchangeCertificate -Thumbprint XXXXXX
$tlscertificatename = "<i>$($cert.Issuer)<s>$($cert.Subject)"
To Replace Send Connector –
Set-SendConnector "Outbound to Office 365" -TlsCertificateName $tlscertificatename
To Replace Receive Connector –
Set-ReceiveConnector "EX2016Server\Client Frontend EX2016Server" -TlsCertificateName $tlscertificatename
if you don’t update receive connector, you can see hybrid mail flow stops with TLS error
Reason: [{LED=450 4.4.317 Cannot connect to remote server [Message=451 5.7.3 STARTTLS is required to send mail] [LastAttemptedServerName=83.0.59.81] [LastAttemptedIP=83.0.59.81:25] [DX2ARE01FT002.eop-are01.prod.protection.outlook.com]};{MSG=451 5.7.3 STARTTLS is required to send mail};{FQDN=83.0.59.81};{IP=83.0.59.81};. OutboundProxyTargetIP: 83.0.59.81.



I ran into this problem today, and unfortunately this did not fix the issue. Here is how i fixed it.
First (fail) I re-ran the HCW and linked the send connector to the new certificate and tried to remove the old one. Still failed with the same message.
Luckily, we are still in the testing phase of O365 mail, so I just deleted the ‘Outbound to Office 365’ send connector, deleted the old certificate and re-ran the HCW.
In a full production environment, this will break mail flow, so use wisely! Hope this helps someone else out.
Thank you for the Additional inputs
Hi Satheshwaran Manoharan
I had the issue where my connector “Outbound to Office 365” was using a expired certificate,
Once I did the following
get-exchangecertificate
copied the thumbprint from new cert
get-sendconnector “outbound to office 365” |fl
verify what cert it was using
ran your Cmd
$cert = Get-ExchangeCertificate -Thumbprint XXXXXX
$tlscertificatename = “$($cert.Issuer)
$($cert.Subject)”Set-SendConnector “Outbound to Office 365” -TlsCertificateName $tlscertificatename
get-sendconnector “outbound to office 365” |fl
new certificate was applied
1376 emails began flowing
thankyou so much , your website got me up and running again.
Paul
Great. Thanks for sharing.
I tried this method and Set-SendConnector returned a message that it had completed successfully but not made any changes. Unfortunately the issuer and subject of my old and new certificates are exactly the same, so I assume Set-SendConnector isn’t able to tell the difference. What I ended up doing was temporarily setting the connector to use one of the other Exchange certificates so that the identifiers WERE different, long enough to delete the expired certificate and then set the connector back to the correct and non-expired certificate. As warned above, this will probably stop mail flow but should take only a minute or two to accomplish.
Thank you for this, I’ve spent over a week trying to figure out why we couldn’t delete our old cert after assigning the new one to the send connectors. I can confirm this works, even if it does break mail flow for a bit.
Thank you. I have spent days trying to fix this!
I need to do this, but a bit unsure as to how to temporally change the cert used on the connector to a.n.other?
I figure that you’ve already figured this out, but here’s a crash course for anyone else who is wondering, that should produce minimal downtime for the send connector:
Open up Exchange Management Shell as administrator
Then run:
Get-ExchangeCertificate | Format-List FriendlyName,Subject,CertificateDomains,Thumbprint,Services,NotAfter
This should give you a list of Certificates on the exchange server, including their Thumbprints.
Then, just run the following code, replacing NEWCERTIFICATETHUMBPRINT with the thumbprint of the new certificate, WRONGCERTIFICATETHUMBPRINT with the thumbprint of any other certificate on the server (besides the old one), and OLDCERTIFICATETHUMBPRINT with the thumbprint of the old certificate you want to replace.
$newcert = Get-ExchangeCertificate -Thumbprint NEWCERTIFICATETHUMBPRINT
$newtlscertificatename = "$($newcert.Issuer)$($newcert.Subject)"$wrongcert = Get-ExchangeCertificate -Thumbprint WRONGCERTIFICATETHUMBPRINT
$wrongtlscertificatename = “$($wrongcert.Issuer)
$($wrongcert.Subject)”Set-SendConnector “Outbound to Office 365” -TlsCertificateName $wrongtlscertificatename
Remove-ExchangeCertificate -Thumbprint OLDCERTIFICATETHUMBPRINT
Set-SendConnector “Outbound to Office 365” -TlsCertificateName $newtlscertificatename
Satheshwaran – thanks a lot.. this worked for us.. after a few hours of troubleshooting much appreciated! great work. cheers!
We had this problem in our production environment. Your instructions worked for me and saved the day. Mail flow was stopped for 30 minutes. You are a life saver. Thank you so much
You are most welcome!
Cheers thank you for the post – worked like a charm! 🙂
I am getting an error
WARNING: The source Transport servers specified for the connector aren’t in the same Active Directory site.
we have 4 servers split across two AD sites. how do I go around this error?
Thank you
Michael
Go for two send connectors with the same weight. if it’s an active/active scenario.
You saved my ass today 🙂 our sysadmin left, and I got put in charge of mail servers. Our hybridext cert expired yesterday and even though I had renewed it, I didn’t realize the send connector would need updated (since we didn’t request an identical replacement with the same thumbprint). MS documentation was way too involved for me to find this little tidbit that I needed. Thanks a million.
You are most welcome Joey. Am happy about it .
Thank you, thank you, thank you. 2 Hours on the phone with M365 support getting nowhere when I finally came across this post and it worked like a charm!
Worked perfectly thanks.
Its worked me perfectly. Thanks for the Article.
Man, thanks so much for saving my face!
Its worked me perfectly. Thanks for the Article.
This will update all send and receive connectors to the same certificate:
$cert = Get-ExchangeCertificate -Thumbprint XXXXXX
$tlscertificatename = “$($cert.Issuer)
$($cert.Subject)”$connectors = Get-SendConnector | Where-Object {$_.TlsCertificateName -ne $Null}
foreach ($connector in $connectors){Set-SendConnector -Identity $connector -TlsCertificateName $tlscertificatename}
$connectors = Get-ReceiveConnector | Where-Object {$_.TlsCertificateName -ne $Null}
foreach ($connector in $connectors){Set-ReceiveConnector -Identity $connector -TlsCertificateName $tlscertificatename}
I have no idea why there are strikethroughs in that reply – ignore them – just copy paste all the text to Powershell.
Matt I have to run this on all the exchange servers?
One is enough as its a global object
You just saved my butt today. I had two Receive Connectors that wouldn’t enable STARTTLS because they could find the old expired certificate. Used your instructions to update the TlsCertificateName and they’re now online and happy. Thanks!
Thanks you, this worked like a charm. however the old certificate is still showing that it is in use by the SMTP service, how would we find out what is using it
you can safely ignore if things are working.
I’m so glad I looked into this before trying to wing it! We indeed have the same issuer/subject as the old certificate, so it was good to have a plan going in. I appreciated the pointers on that piece, and the idea to assign a random certificate, so you can delete the old one, then set the new one.
On a different post I saw someone suggest setting it to null, and I did do that and I can confirm that it did work. Not a ton easier, but a little easier than assigning a different cert so I figured I’d mention it.
Set-SendConnector “Outbound to Office 365” -TlsCertificateName $NULL
Thanks again this was a life saver!
Items that I used to expand:
#Get the thumbprint for the new certificate:
Get-ExchangeCertificate
# This listed quite a few certificates, I didn’t know which certificate was the correct one
Get-ExchangeCertificate -Thumbprint | Format-List *
#gives more details on the certificate to validate the correct one and correct dates. before proceeding
#Send Connector – to find out for sure what you need next for the O365 connector. Used this to validate that I was using the correct send connector
get-sendconnector
#Receive Connector – to list out all the connectors and find out what exactly is needed for the “MY-EXCH01\Default Frontend MY-EXCH01”
Get-Receiveconnector
Get-ExchangeCertificate -Thumbprint thumbprintID | Format-List *
got lost in translation.
Hello, We have Hybrid wizard completed, but we are not using Office 365 to mailflow emails still going from onsite exchange, but we need send between Exchange and office 365 emails. I know our certificate expired, can I just rerun Hybrid wizard and it will replace certificate?
Good stuff man. It saved my ass. Thanks!
Hello All,
It seems the instructions got updated.
1 year ago, I took some notes, and this command was displaying at the end of the instructions.
Set-ReceiveConnector “(Exchange server name)\Default Frontend “Exchange server name)” -TlsCertificateName $tlscertificatename
Now this command it is gone from this page, and I am trying to figure out if the process has changed?
Hey Campeon, Thanks for pointing out. It got hidden for some reason. Updated now.
Nothing changed
Thanks for reply.
is this the correct syntax?
Set-ReceiveConnector “(Exchange server name)\Default Frontend “Exchange server name)” -TlsCertificateName $tlscertificatename
Thanks for reply.
is this the correct syntax? I did run the command – Get-Receiveconnector to view the correct connectors.
Set-ReceiveConnector “(Exchange server name)\Default Frontend “Exchange server name)” -TlsCertificateName $tlscertificatename