Microsoft Certificate Authority becomes a key server if its integrated to Critical Services like Meraki,Skype for Business, RADIUS Servers ,and any cert based applications signed by domain authority.If its a virtual infrastructure. I usually take a clone of these servers to test the same. Just to make sure all going to be ok .As once you export the Certificate with keys you got to remove the Server Role and Reboot. And I feel comfortable if it imports ok on the clones. As there is kind of no go back. you can always promote the server back and Install the certificate authority as a backup plan . please note that during this period . you cannot re issue or renew or revoke the certificate.
- Backup Certificate Authority.
- Backup Certificate Authority Registry.
- Backup Custom Files if modified.
- Uninstall Certificate authority and Domain controller
- Install Certificate authority Server with Same name or different Name.
- Restore Certificate authority
- Restore Certificate authority Registry (Retains the old Certificate authority Name even if the server name is different)
Backup Certificate Authority – Database, Log Files, and Private Key
Open Certification Authority
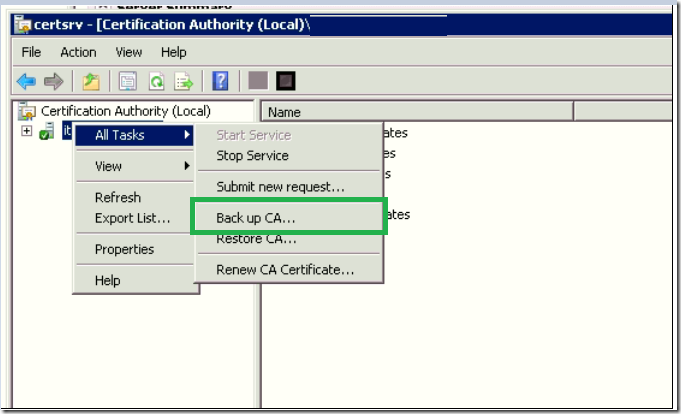
In the Certificate authority console, right-click your CA in the left pane, select All Tasks ,select Backup CA.
In the Certification Authority Backup Wizard, click Next on the welcome screen.
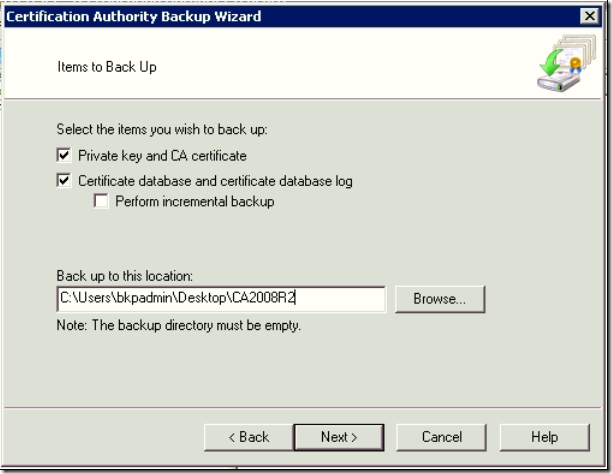
On the Items to Back Up screen, check Private key and CA certificate and Certificate database and certificate database log.
Click Browse to the Back up to this location, select an empty folder to store the backup files, and click Next to continue.
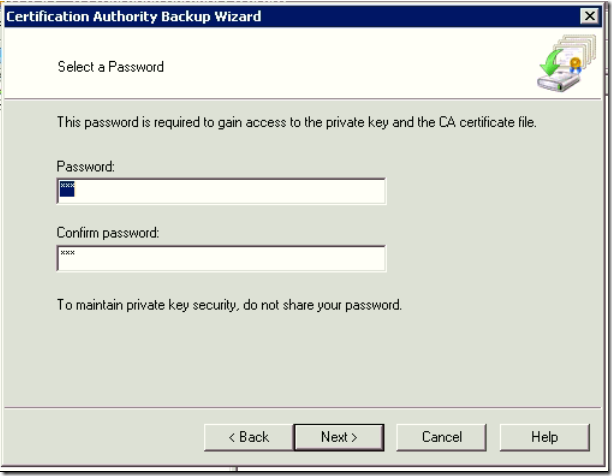
Choose a Password and Confirm Password to protect the private key and CA certificate. Click Next to continue.
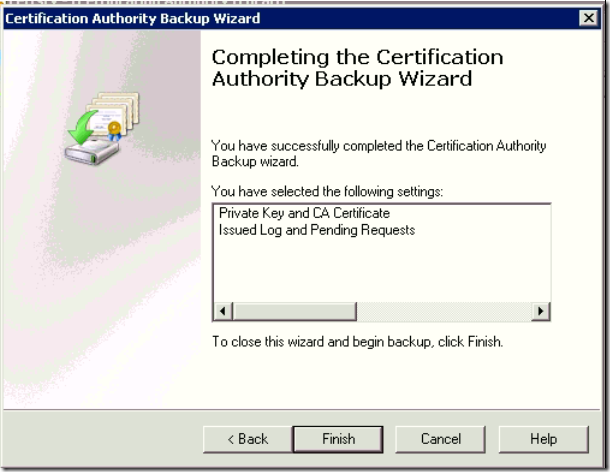
Click Finish – Completing the Certification Authority Backup Wizard
Open cmd Run as administrator.
net stop certsvc and press Enter to make sure the CA cannot issue certificates.
Backup / Export the Registry.
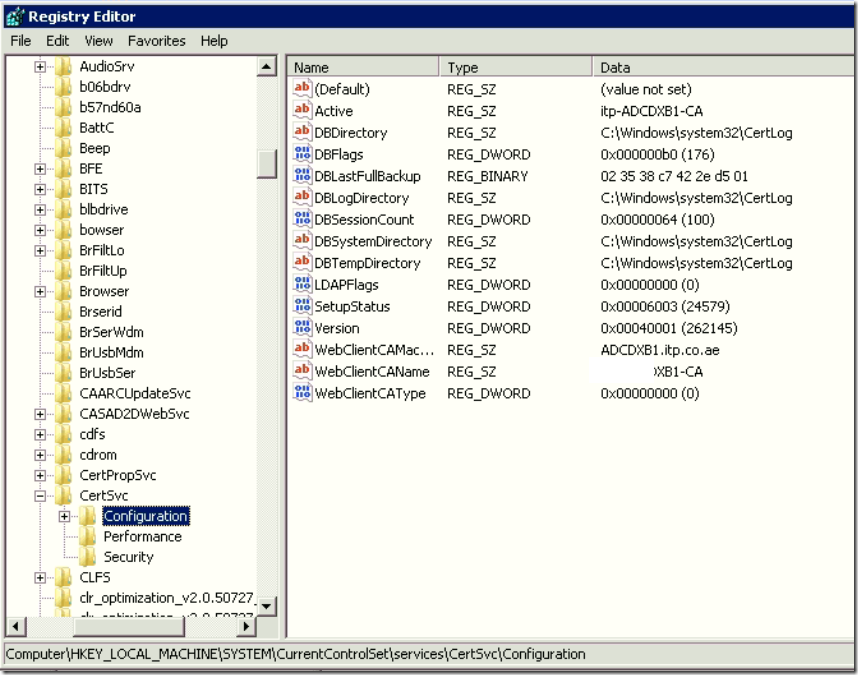
Registry key from here: HKLM\SYSTEM\CurrentControlSet\Services\CertSvc\Configuration
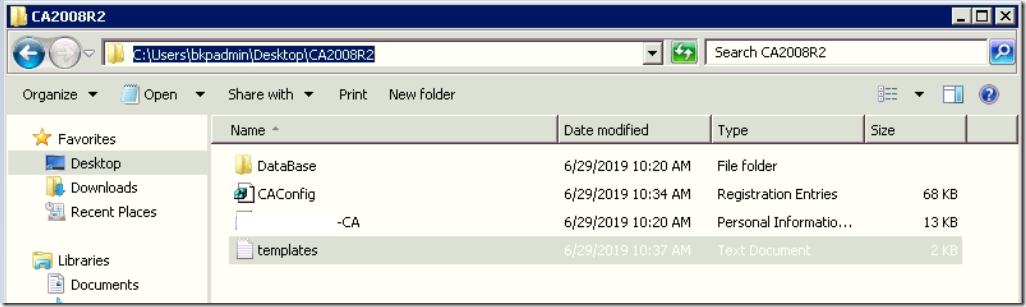
if you have any custom templates
Certificate Templates: Open the PowerShell command prompt with run as administrator, run the below mentioned command
certutil.exe –catemplates > “c:\CA2008R2\templates.txt”
If you have a customized CAPolicy.inf then copy it from %systemroot% directory.
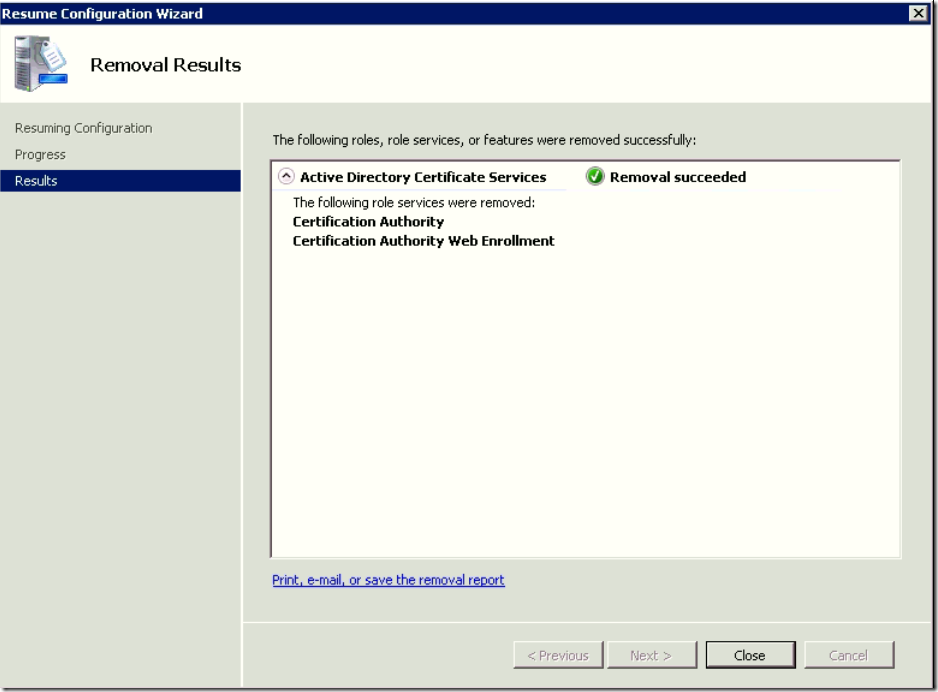
Uninstall Root CA using Server Manager and Dcpromo to demote the Domain controller
if you want to retain the same name of the server. wait for the active directory to replicate in all sites else force the Active Directory Replication.
Rename the server, change the IP and remove the server from the domain.
Now login to the new server.
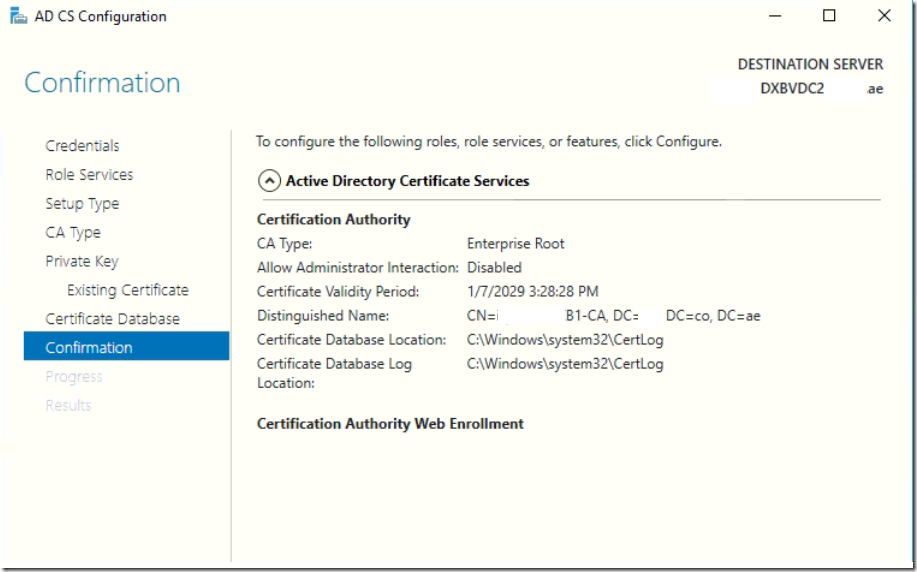
Install New Root CA server on the Private Key Wizard. DO NOT CREATE NEW PRIVATE KEY> Import the existing private key.
Type the password for the file when prompted, then confirm it.
Give the same name as old Root CA . if you wish to have a different Server name. it will still work . But when you import the registry the Old CA Name will be retained.
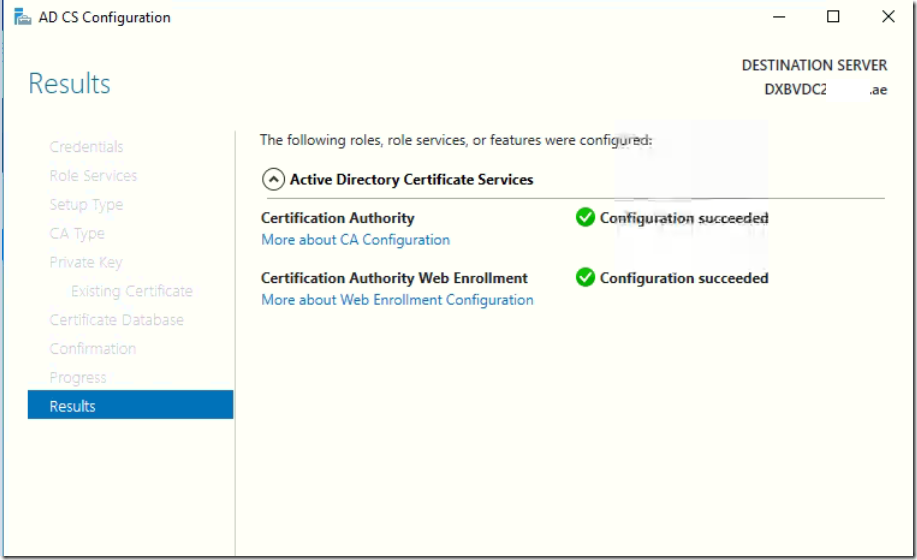
Now Configuration Succeeded without any issues.
Restore the Root CA backup
Open Certification Authority.
In the CA console, right-click your new CA in the left pane, select All Tasks from the menu and then Restore CA.
If you are prompted to stop the Active Directory Certificate Service, click OK continue.
In the Certification Authority Restore Wizard, click Next on the welcome screen.
On the Items to Restore screen, check Private key and CA certificate and Certificate database and certificate database log.
Click Browse to the backup copied location to restore from this location. Give one level up than backup location where the backup files are located, click OK in the Browse for Folder window and then Next to continue in the wizard. Click Finish
You should now be prompted to restart the AD CS service. Click Yes to confirm the operation.
open cmd prompt as administrator
net stop certsvc
-Double click on the copied registry file. When prompted click yes to update the registry.
Typical installation . Will not have templates neither custom .inf file. you can safely skip the below step. if you haven’t done any customization.
Restore Template if you had exported .
On the PowerShell, run the below command This command will add the DirectoryEmailReplication template in AD to the list of CA templates, if it doesn’t already exist. You can get a list of the templates by opening the catemplates.txt file saved as part of the backup procedure.
certutil -setcatemplates +DirectoryEmailReplication.
Restore Policy INF: If we found a customized CAPolicy.inf then copy it to %systemroot% directory
Restart the Certificate Authority Server.