ICMP stands for “Internet Control Message Protocol.” It is a network layer protocol within the Internet Protocol (IP) suite, which is a set of protocols that govern how data is transmitted and received over the internet. ICMP is primarily used for communication between network devices to convey control and error messages.
- Network Reachability Testing: “Ping” is widely used to determine whether a remote host or network device is reachable over a network, including the internet. If a device responds to a “ping,” it indicates that it is online and accessible.
- Round-Trip Time Measurement: “Ping” is also used to measure the round-trip time (RTT) for a packet to travel from the sender to the target and back. This information helps assess network performance and latency.
- Network Troubleshooting: Network administrators and IT professionals use “ping” to diagnose connectivity issues. If a device does not respond to a “ping,” it may indicate a network problem or that the target device is down.
Step 1 : Lets create a Virtual machine to check Internet Control Message Protocol.
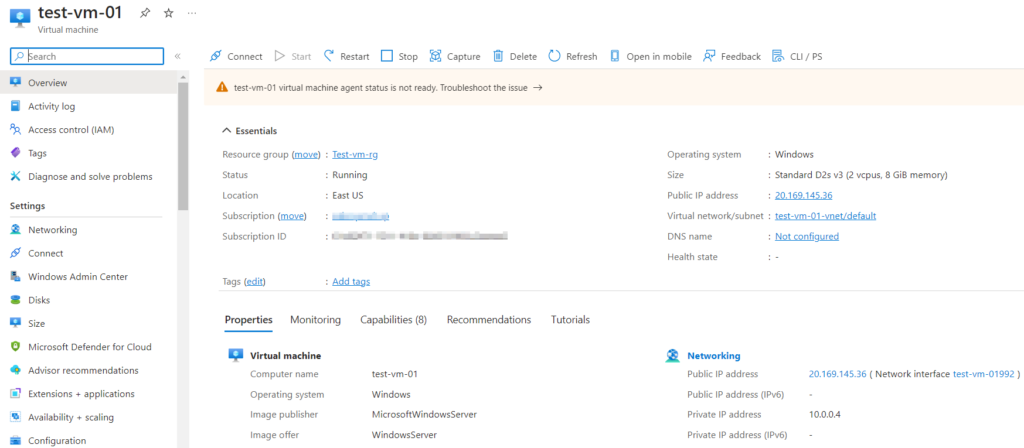
Step 2 : Checking ICMP with the ping Command from my Local machine. Following the Ping command paste the Public IP of the Virtual Machine.
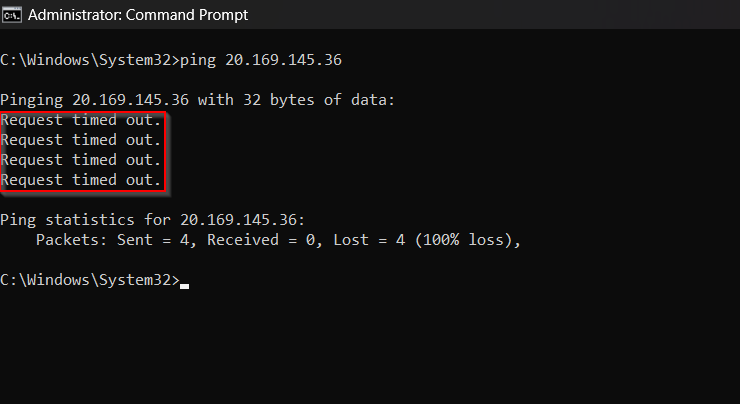
Failed to get a response message from our Virtual Machine. This is due to Network Security Group present in the Virtual Machine.
Step 2 : Lets check the Network Security Group of the Virtual Machine for Inbound Traffic Rules. Here there is no Inbound Traffic Rules to allow ICMP request.
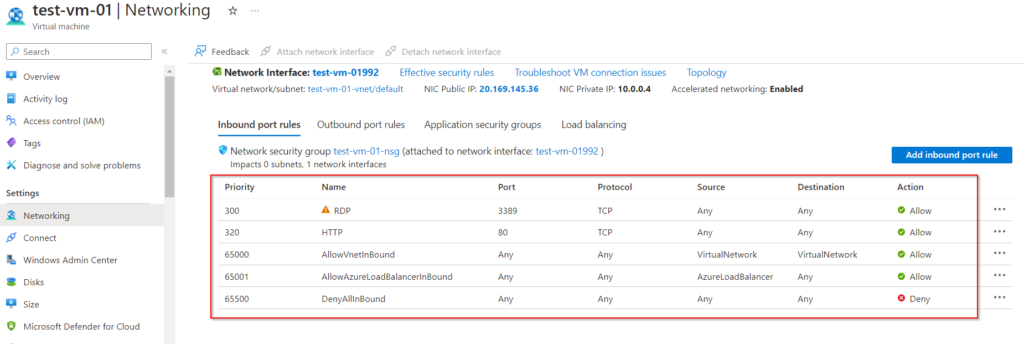
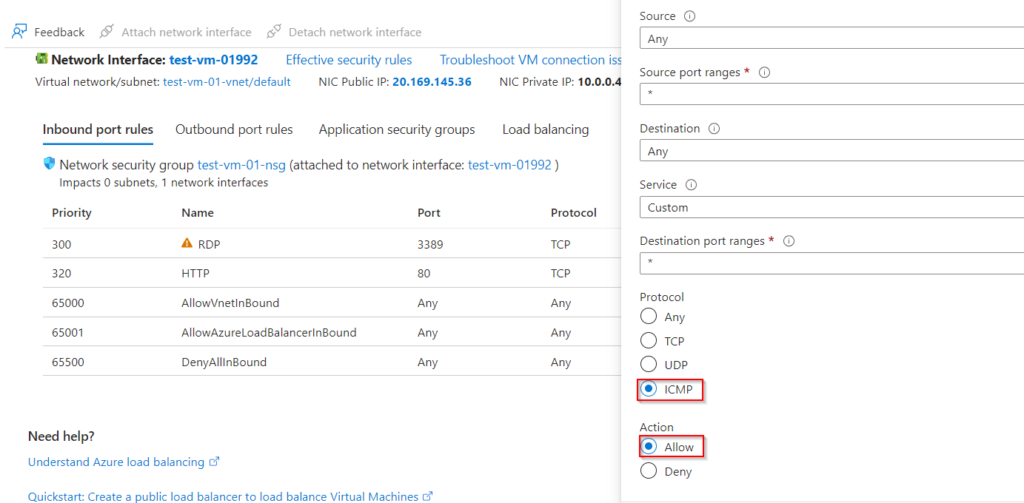
Step 3 : Now lets create a new Inbound Traffic Rule to allow Ping requests. Click on Add Inbound Rules and select ICMP, and save.
Step 4 : Now lets try sending a ping request to the Virtual Machine.
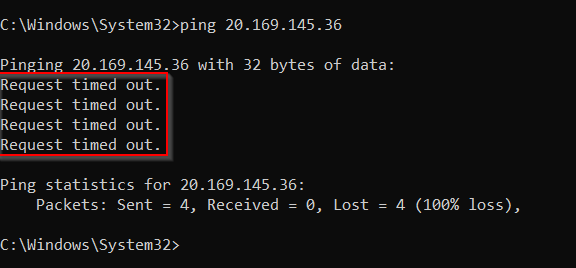
Again failed to get a response from the Virtual Machine even adding a Inbound Rule in the Network Security Group.
This use due to Firewall present in the Virtual Machine. Here the Network Security Group allows the Ping request but the Firewall in virtual machine block’s it.
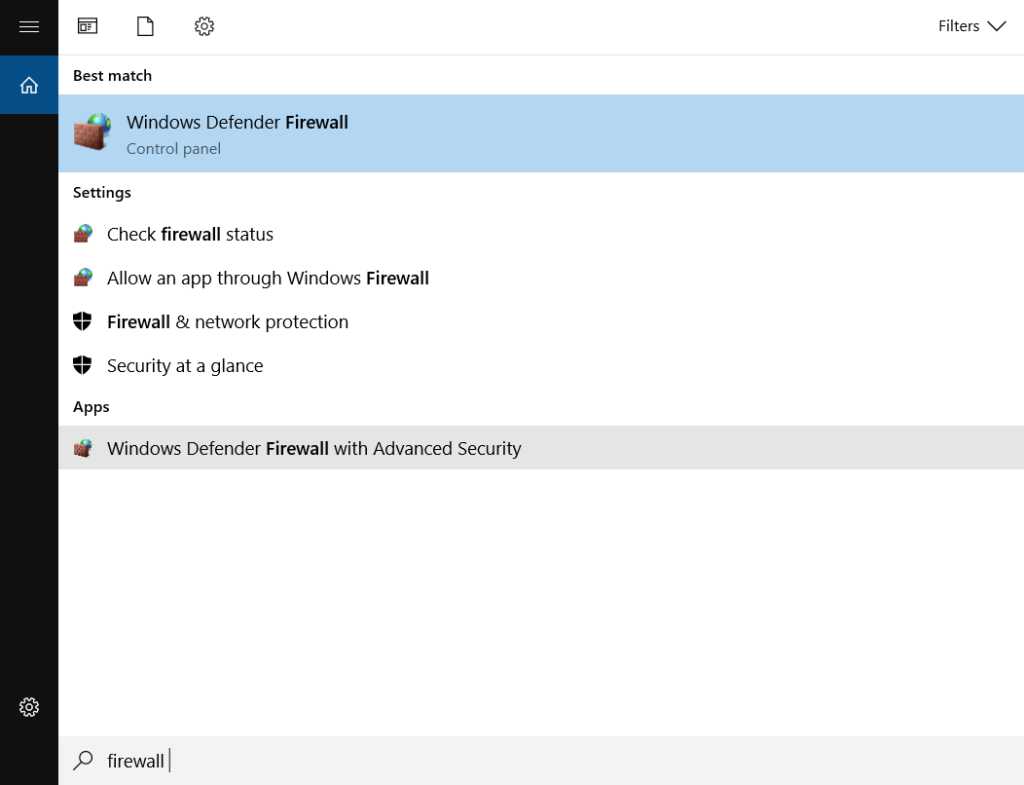
Step 5 : Now we can connect to the virtual machine and add an Inbound Rules in the Firewall of the Virtual Machine.
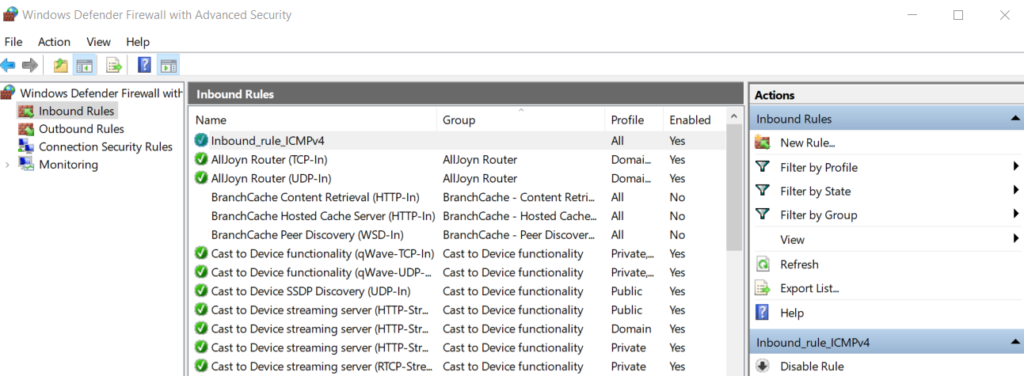
Once we login in the VM, search for Windows Firewall and click on Windows Defender with Advanced Security.
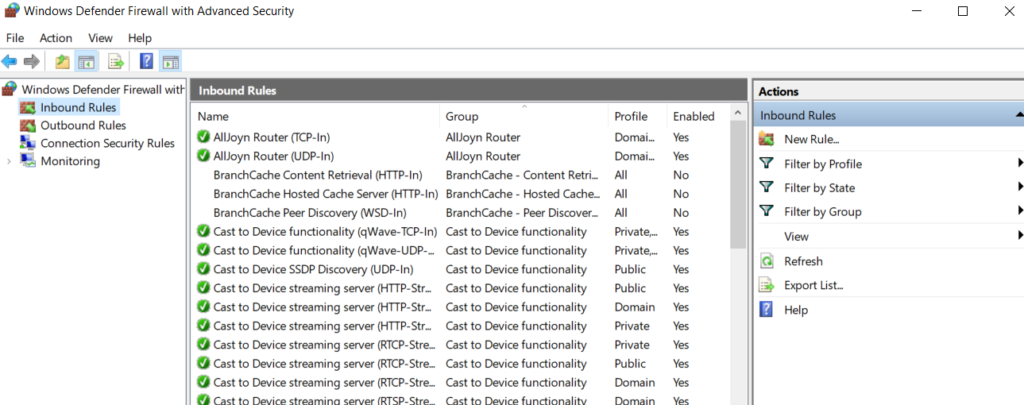
Step 6 : Select Inbound Rules and add the ICMP rule.
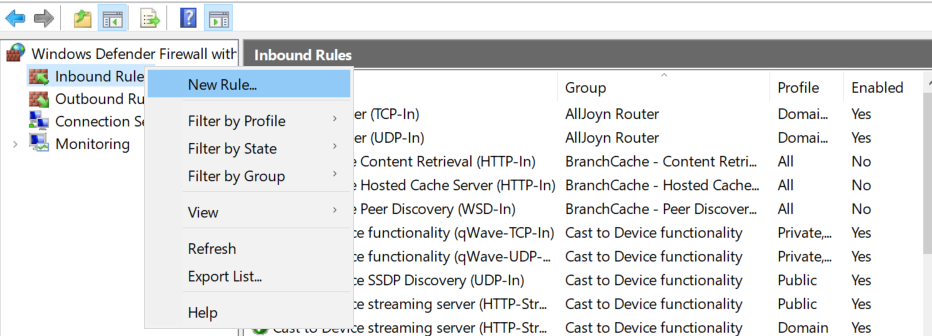
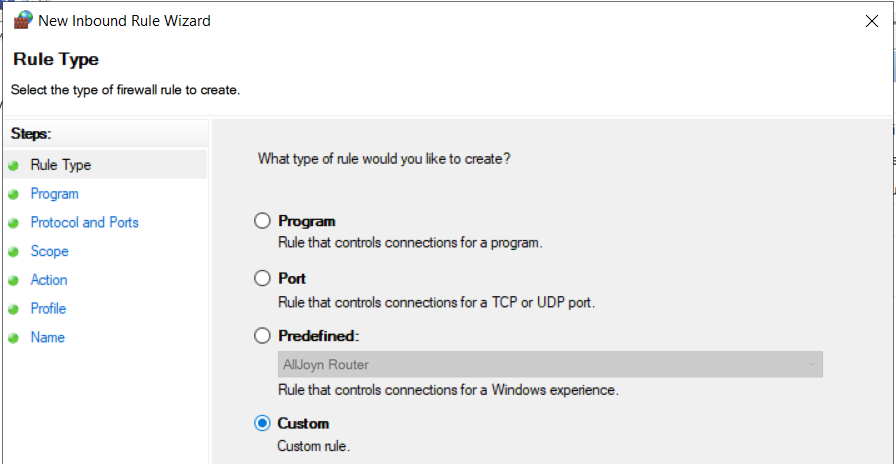
Select Custom Rule.
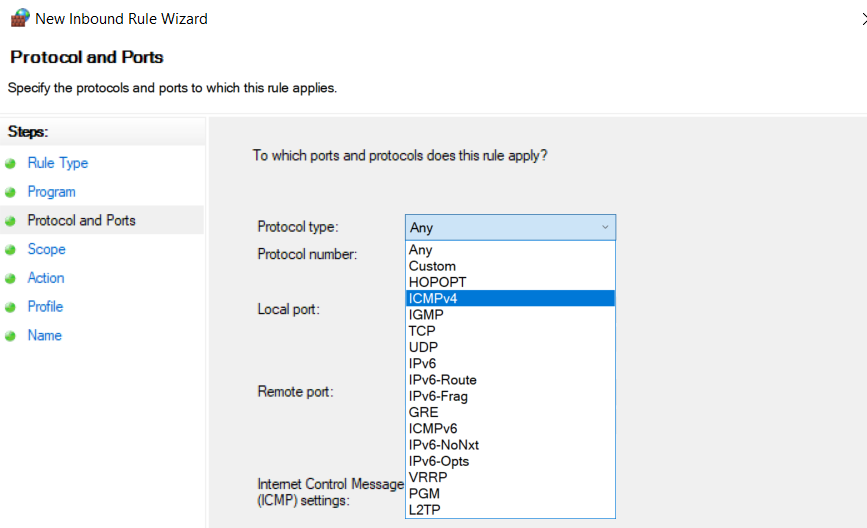
Keep other setting as default and select ICMPv4 for Protocol Type.
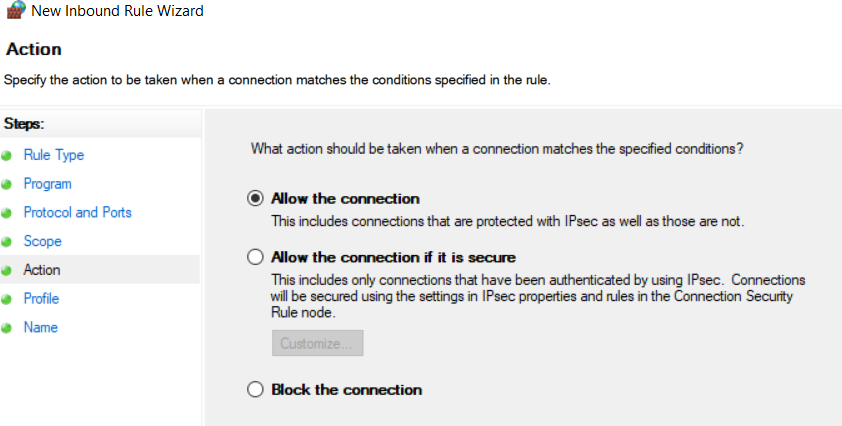
Select Allow the Connection.
Provide a Name for the Firewall Rule and Click on Finish.
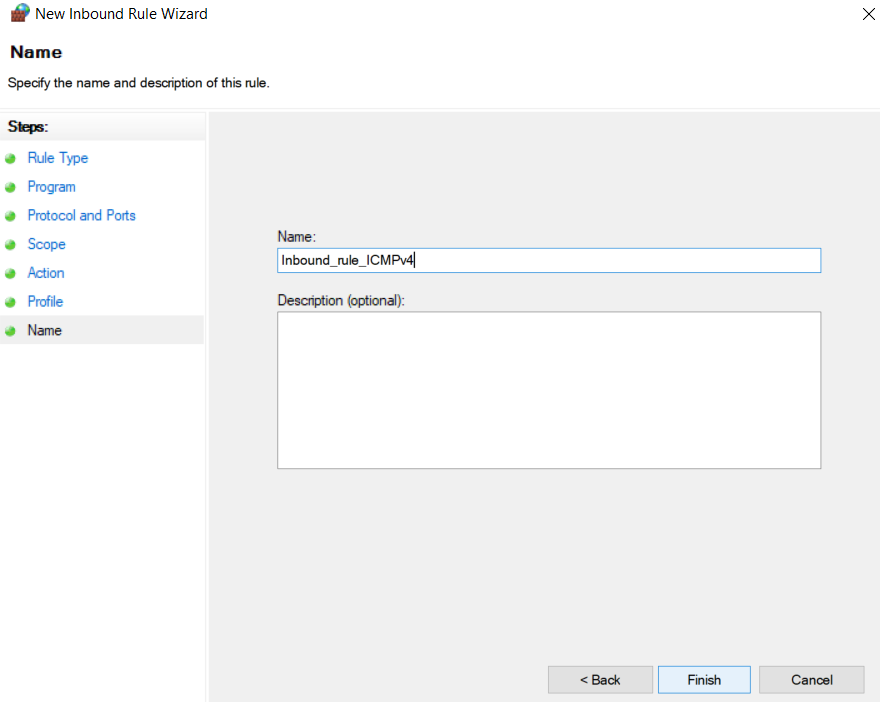
Inbound Rule is added to Windows Firewall of the Virtual machine.
Step 7 : Now let’s check for the Internet Control Message Protocol with the Ping connand.
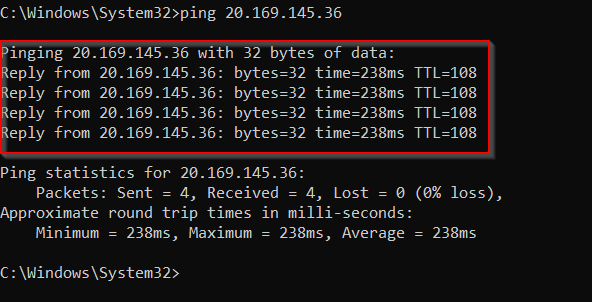
Successfully got reply message from the Virtual Machine.


