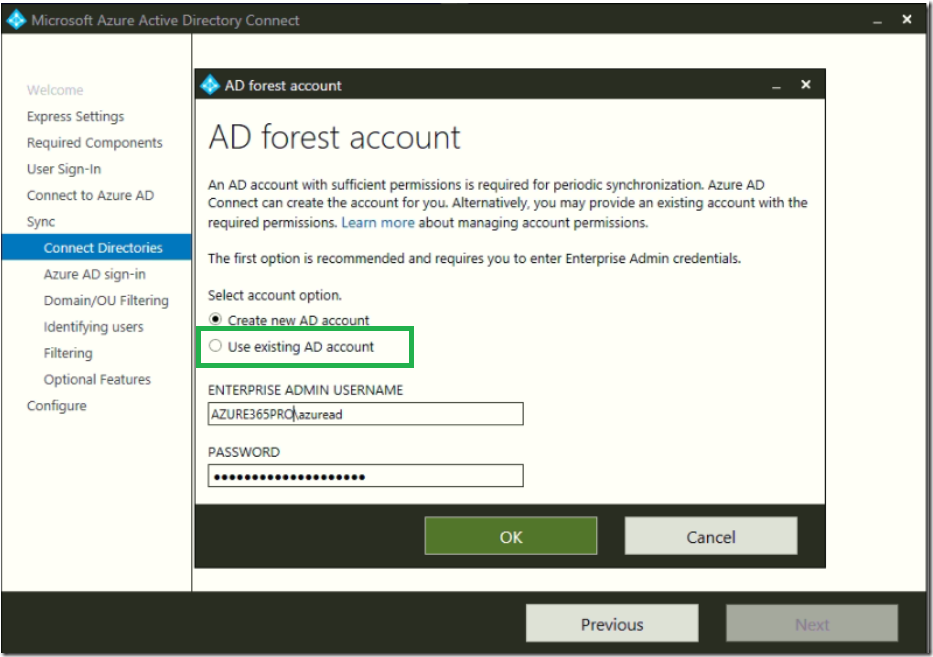
There are some scenarios where user used “Use Existing AD Account” and used a domain admin or Enterprise admin account where this account doesn’t require high privilege permissions.Lets see how to harden them by removing the enterprise admin or domain admin permission and provided only limited permissions only.
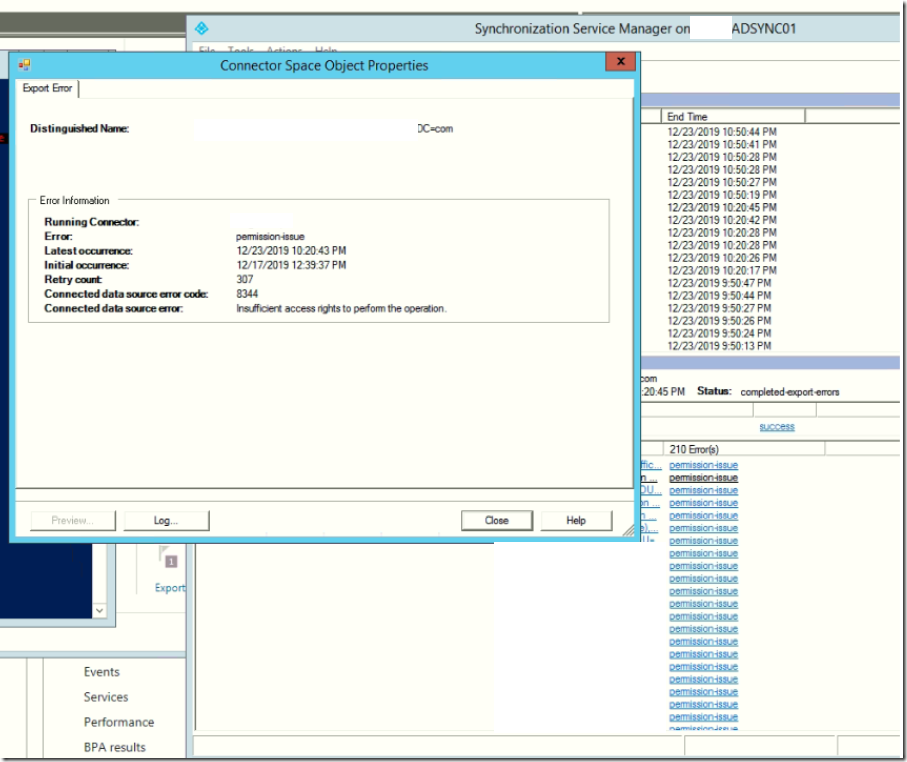
Once you remove Domain Admin Account or Enterprise Admin of this Service account. you can see AD Sync will fail because of permission issues.
Now lets see how to Add Required AD Sync permissions only for the service account.
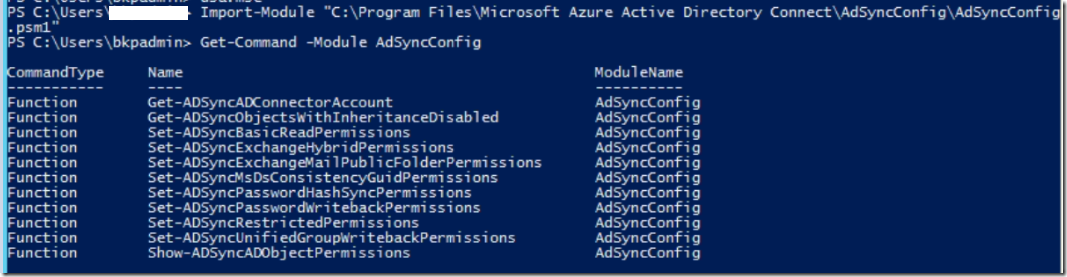
Import the required Module _ ADSyncConfig.psm1
Import-Module "C:\Program Files\Microsoft Azure Active Directory Connect\AdSyncConfig\AdSyncConfig.psm1"
Verify the module is properly loaded or not.
Get-Command -Module AdSyncConfig
Now Add the ADSyncPasswordHashSyncPermissions for the service account. You can always use –ADConnectorAccountDomain if you have multiple Azure AD Account Domains.
Set-ADSyncPasswordHashSyncPermissions -ADConnectorAccountDN 'ADAccountDN'
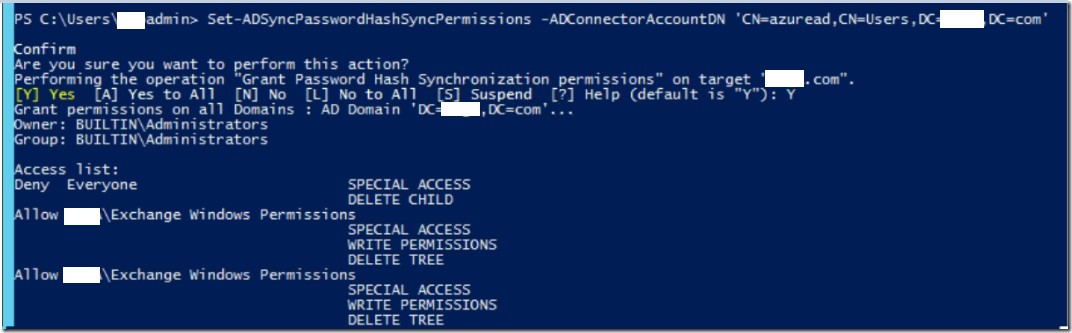
You can see its skipping AdminSDFolder by Default. So leave as it is.
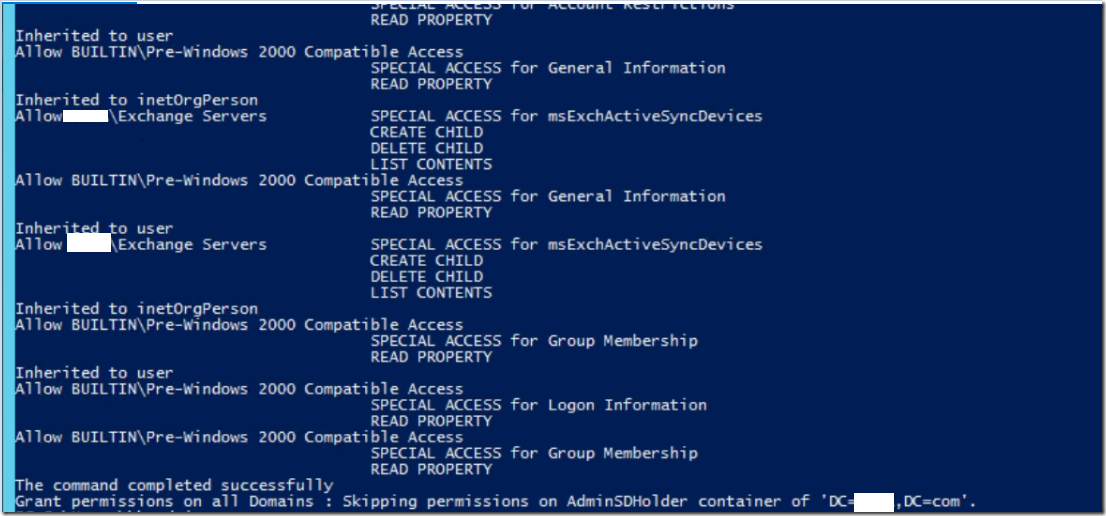
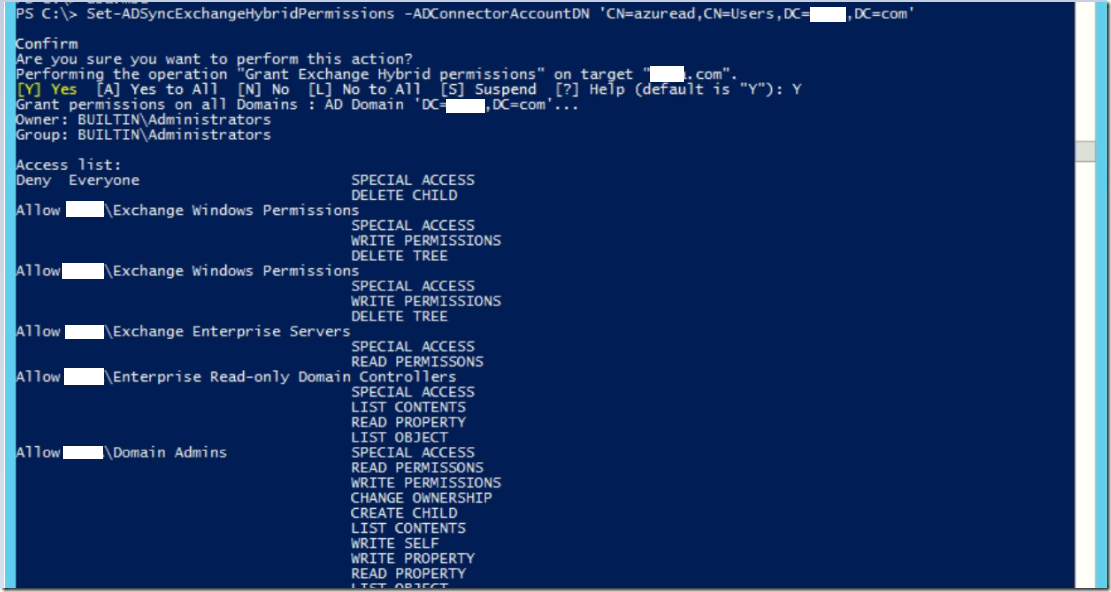
Now Add the Exchange Hybrid Permissions if you are planning to have Exchange Hybrid.
Set-ADSyncExchangeHybridPermissions -ADConnectorAccountDN 'ADAccountDN'
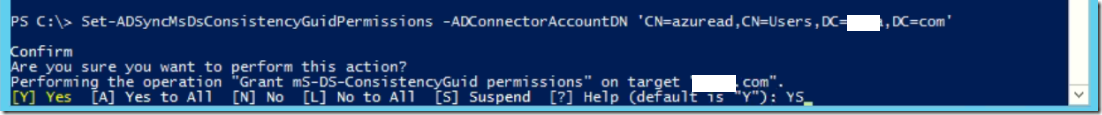
Provide ADSyncMsDsConsistencyGuidPermissions for the service account.
Set-ADSyncMsDsConsistencyGuidPermissions -ADConnectorAccountDN 'ADAccountDN'
This is a ideal scenario. which proper permission inheritance without password write back.
Refer below Microsoft Article if you wish to tighten the permissions even more further like disabling inheritance on the object and add required permissions only or add password write back permissions for the object like
Set-ADSyncPasswordWritebackPermissions –ADConnectorAccountDN 'ADAccountDN'



Thank you so much for taking the time to write this post. Just what I needed and more