Enabling Opportunistic TLS on your Anti spam Devices
A method which can described as “best effort”. When we configure our anti spam appliance to use the option of opportunistic TLS, each time that the anti spam appliance will try to send E-mail message to the internet , our mail system/anti spam will try to verify if the other side supports TLS (START TLS) .
If the destination messaging system supports TLS, our anti spam appliance will send the mail over a secure communication channel using the TLS protocol. if the desitination messaging system doesn’t support TLS it will fall back to un-encrypted communication channel.
Same steps taken while connecting for incoming emails as well . In this environment Iron Port anti spam appliances deliver and receive email.so lets see how to set TLS as Preferred / Opportunistic so that it works smoothly without affecting production emails.
In my Scenario my domain MX is below
A Records and MX Records
mx1.azure365pro.com 195.10.10.11
mx2.azure365pro.com 195.10.10.12
mx3.azure365pro.com 195.10.10.13
mx4.azure365pro.com 195.10.10.14
PTR Records as below _
195.10.10.11 mx1.azure365pro.com
195.10.10.12 mx2.azure365pro.com
195.10.10.13 mx3.azure365pro.com
195.10.10.14 mx4.azure365pro.com
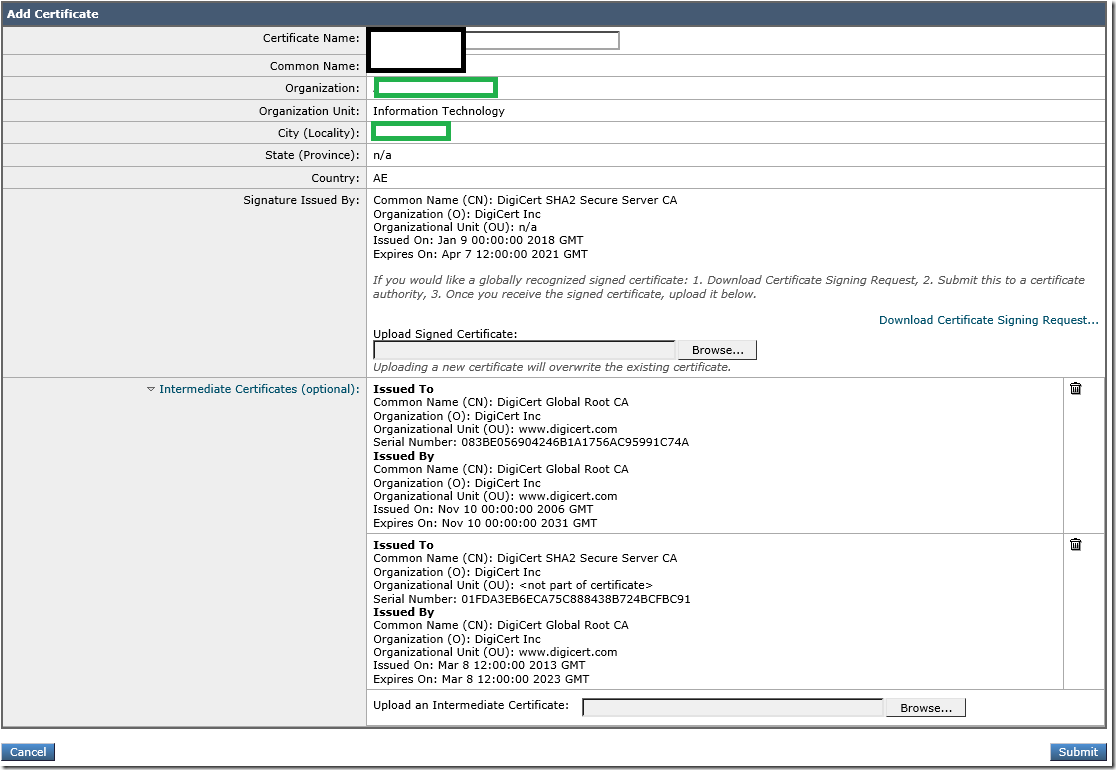
Wild Card Certificate from Digicert
*.azure365pro.com
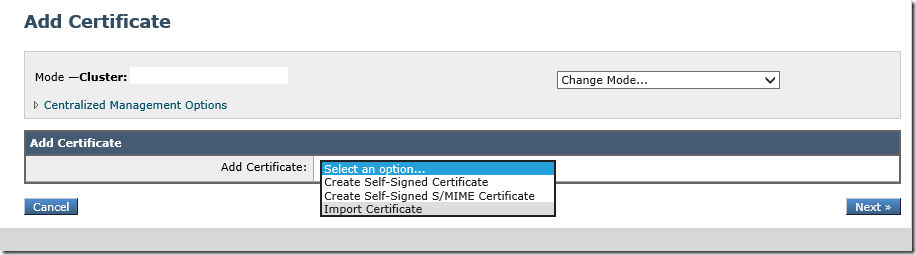
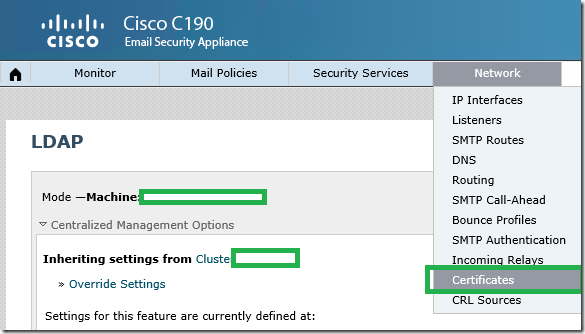
Choose Network _ Certificates
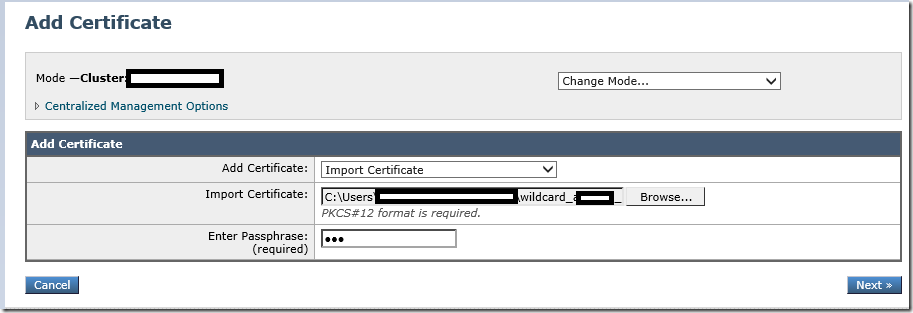
Lets Add Certificate . Choose Import Certificate
Choose the file and enter the passphrase . Click Next
Click on Submit
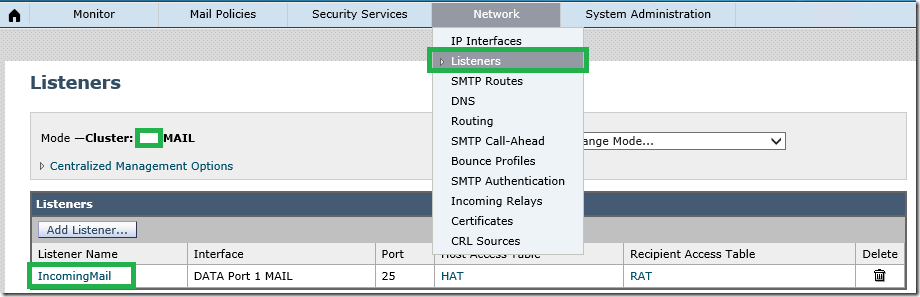
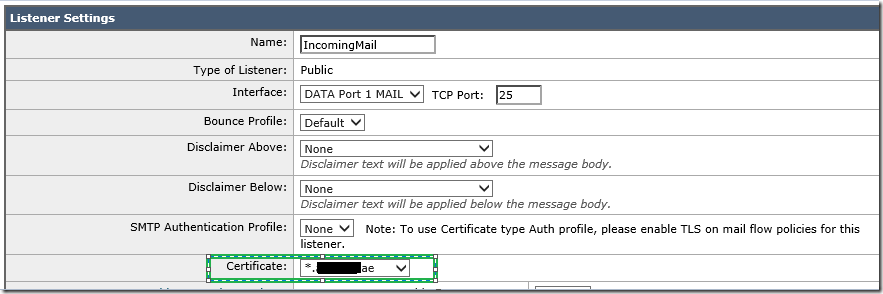
Assign the certificate on the listeners used
Choose the Certificate imported and click on Submit and Commit
Lets see how to import on the Inbound Emails First.
Choose the certificate click submit and commit.
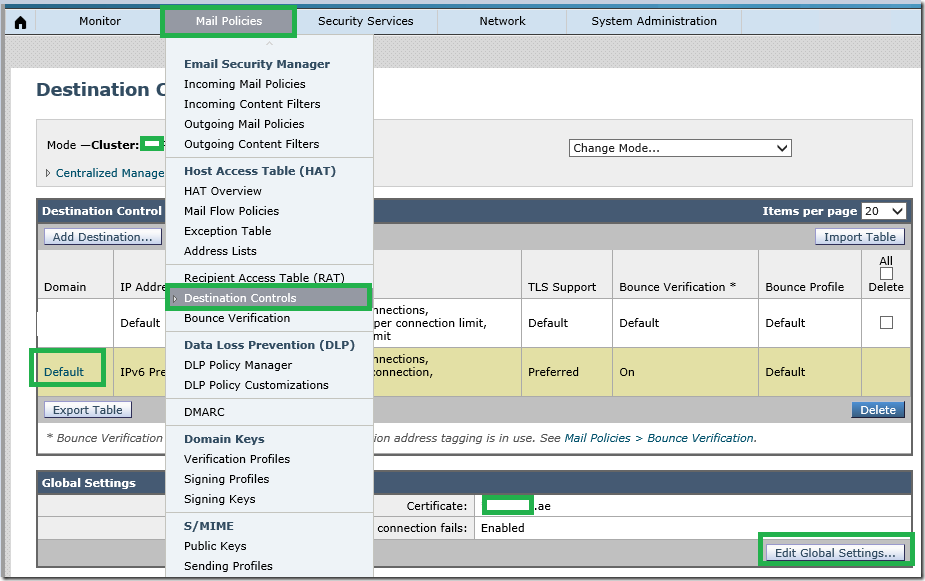
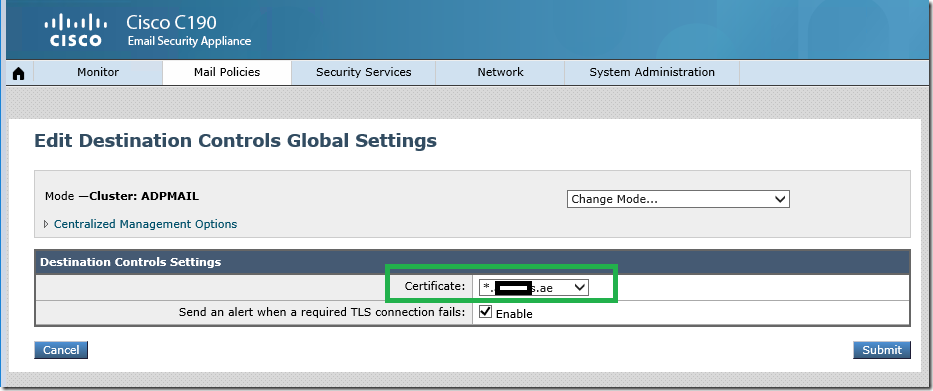
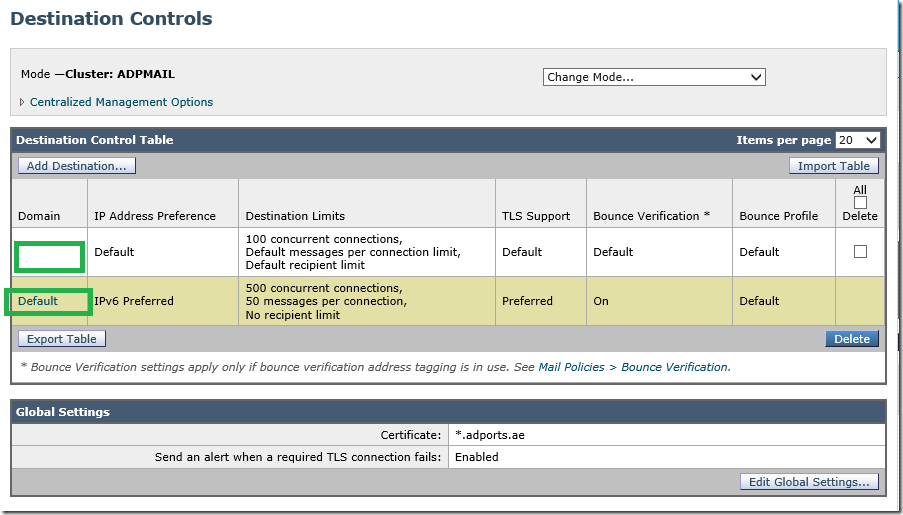
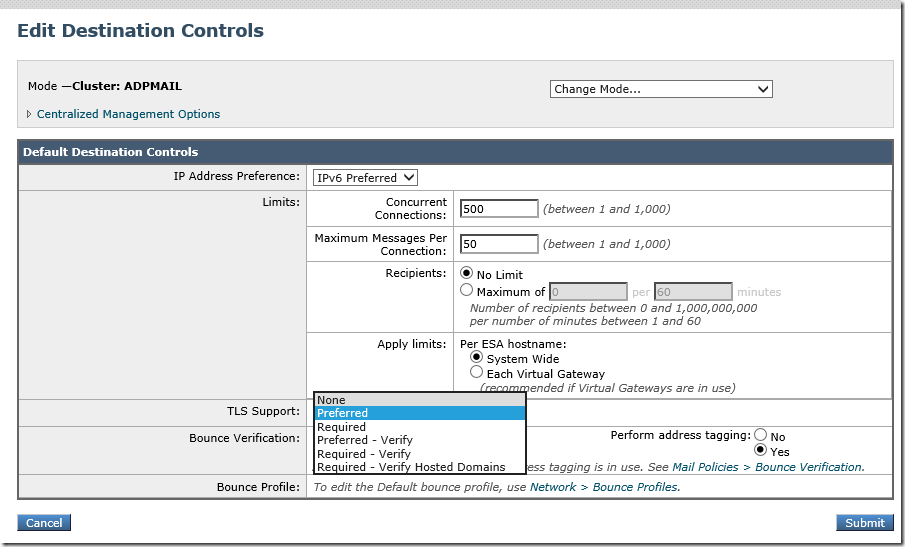
Now click on the default connector.
Set TLS Support to Preferred .
Submit and commit.
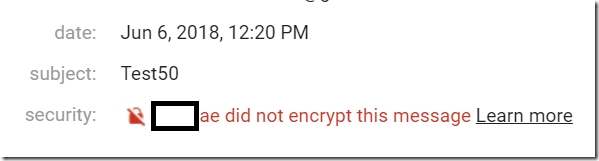
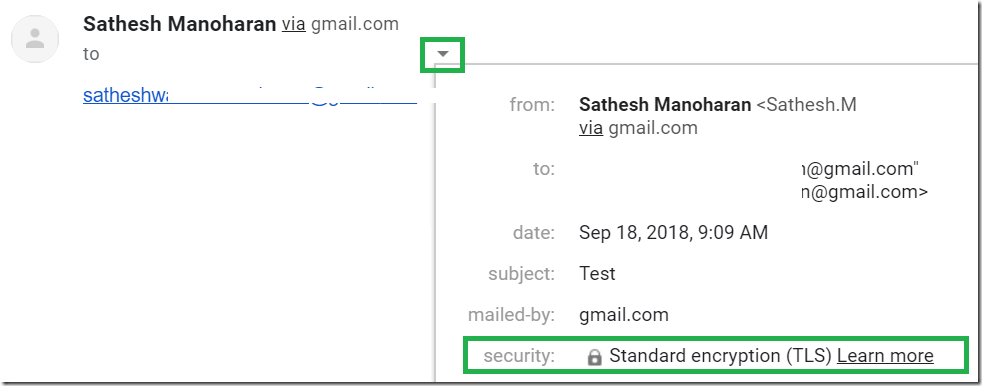
Easiest way to validate send a email to gmail . It will show you the message was transferred using TLS or unencrypted.
Before
After
Now lets see how to enable for incoming email.
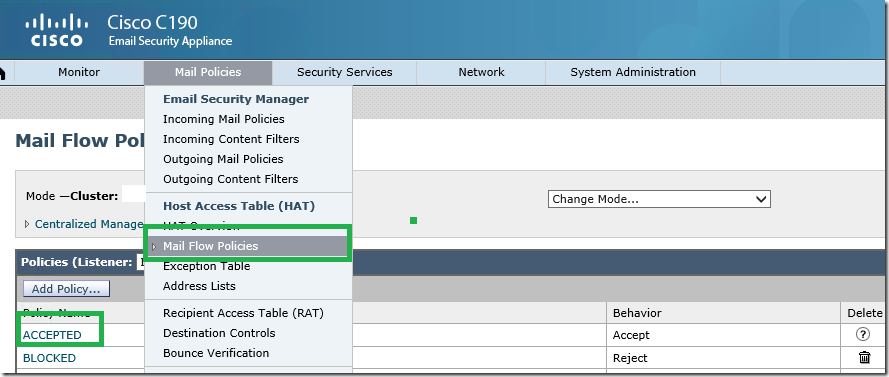
Click on Mail Policies – Mail flow policies – Accepted
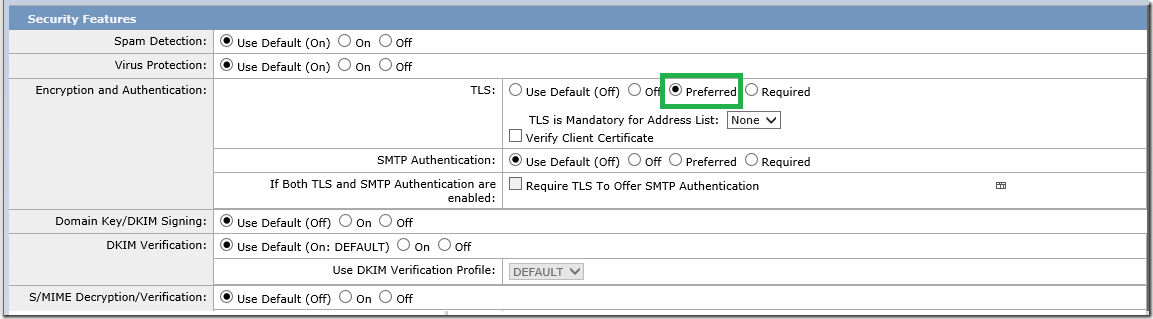
Now set TLS to Preferred . Submit and Commit.
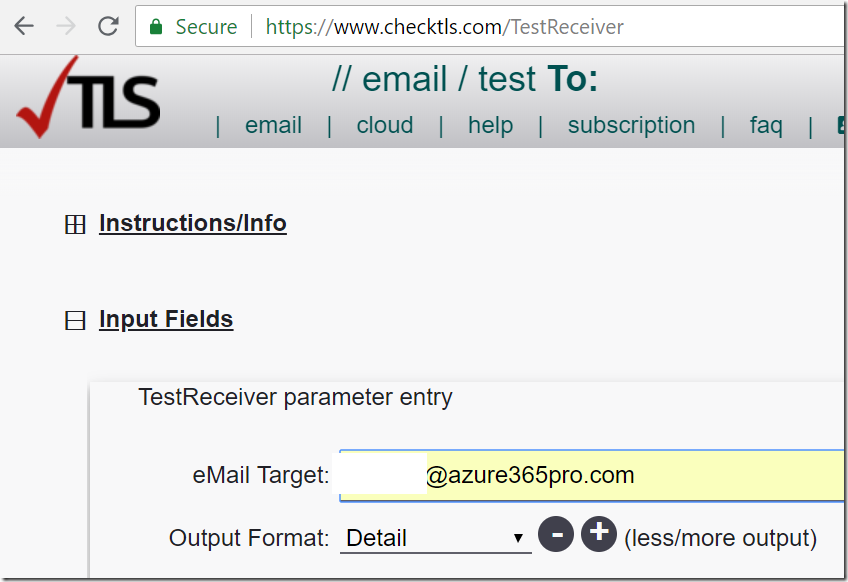
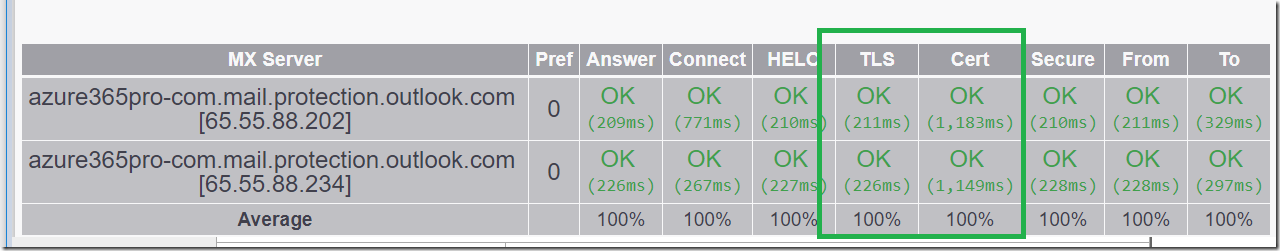
you can validate on this site.
Now we have enabled Opportunistic TLS on outbound and inbound emails.
It will be used wherever possible.