Lets see how to synchronize azure active directory users by providing Azure Active Directory API Permissions with mimecast directory synchronization and configure inbound and outbound mail flow with mimecast. Currently On-Premise Exchange server Configured in Hybrid Mode and Azure AD Connect is Configured with Password hash Synchronization. We will move Mail flow to mimecast and start moving mailboxes to the cloud.This Configuration is suitable for Office 365 Cloud users and Hybrid users.
Log into the mimecast console
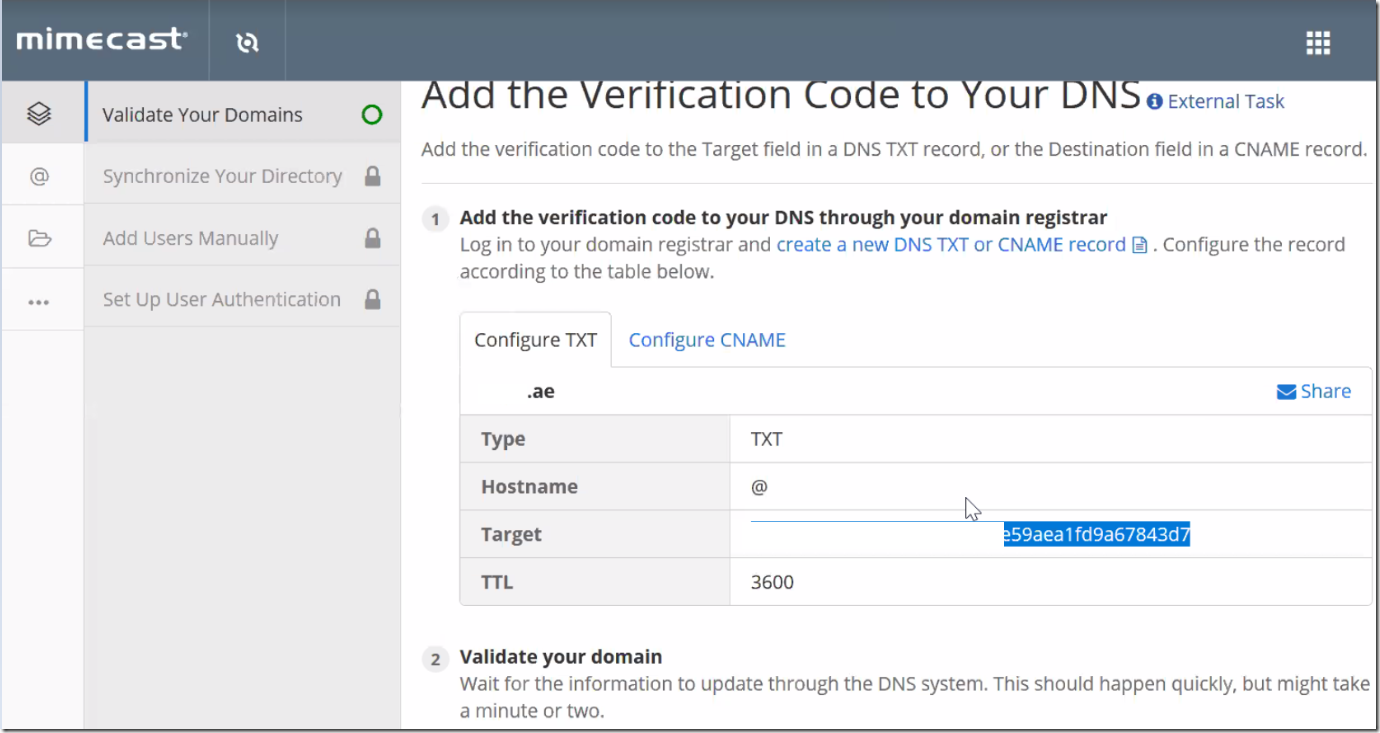
First Add the TXT Record and verify the domain.
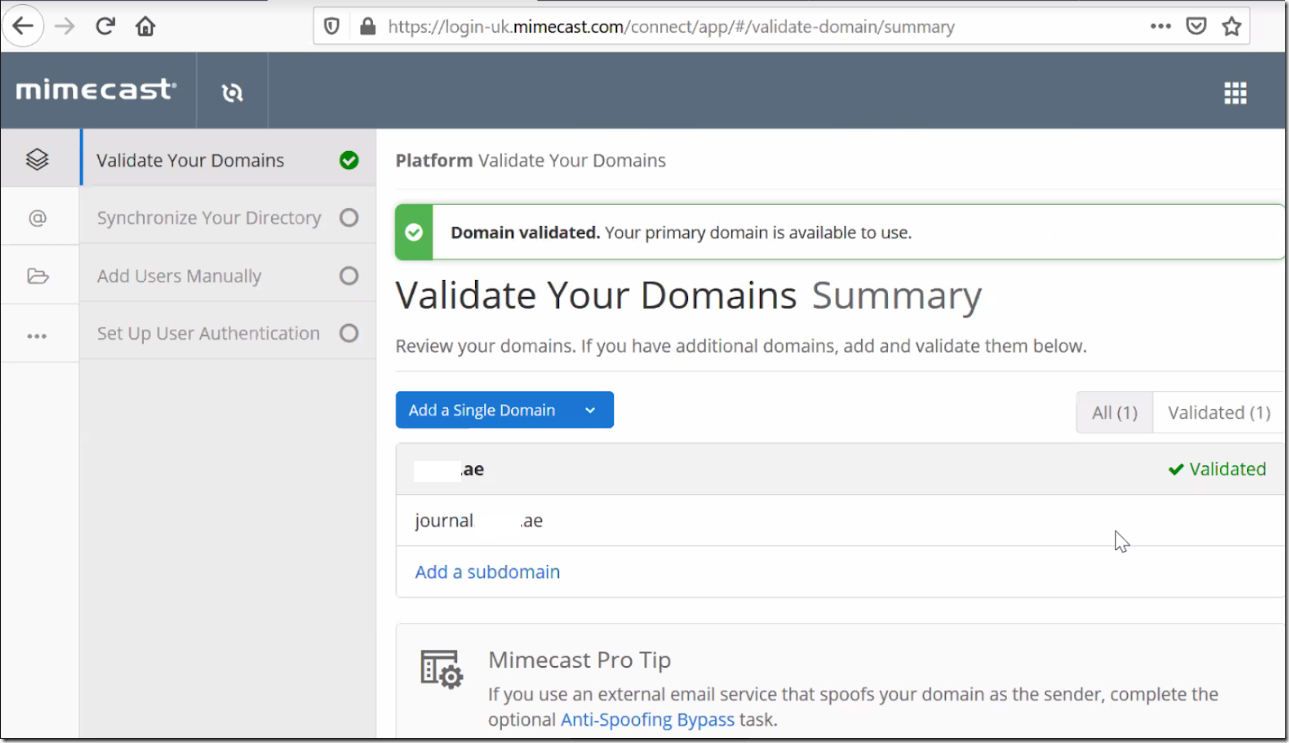
Once the domain is Validated. Choose Next.
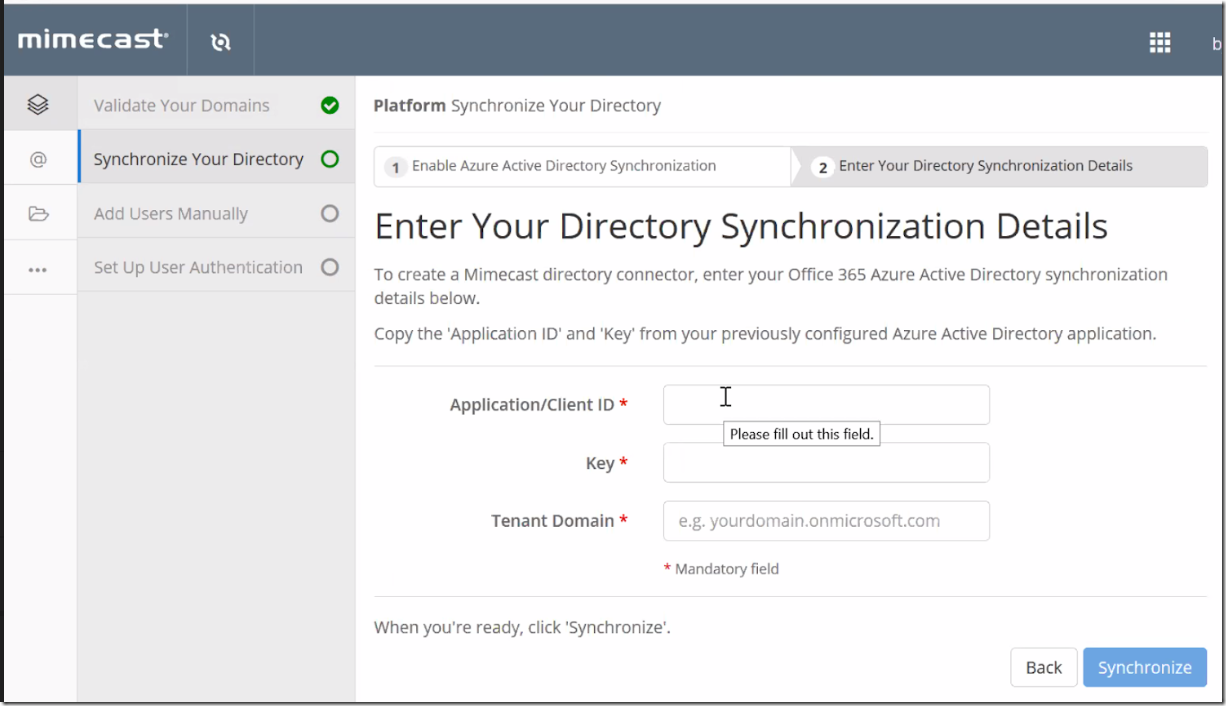
Now we need to Configure the Azure Active Directory Synchronization.
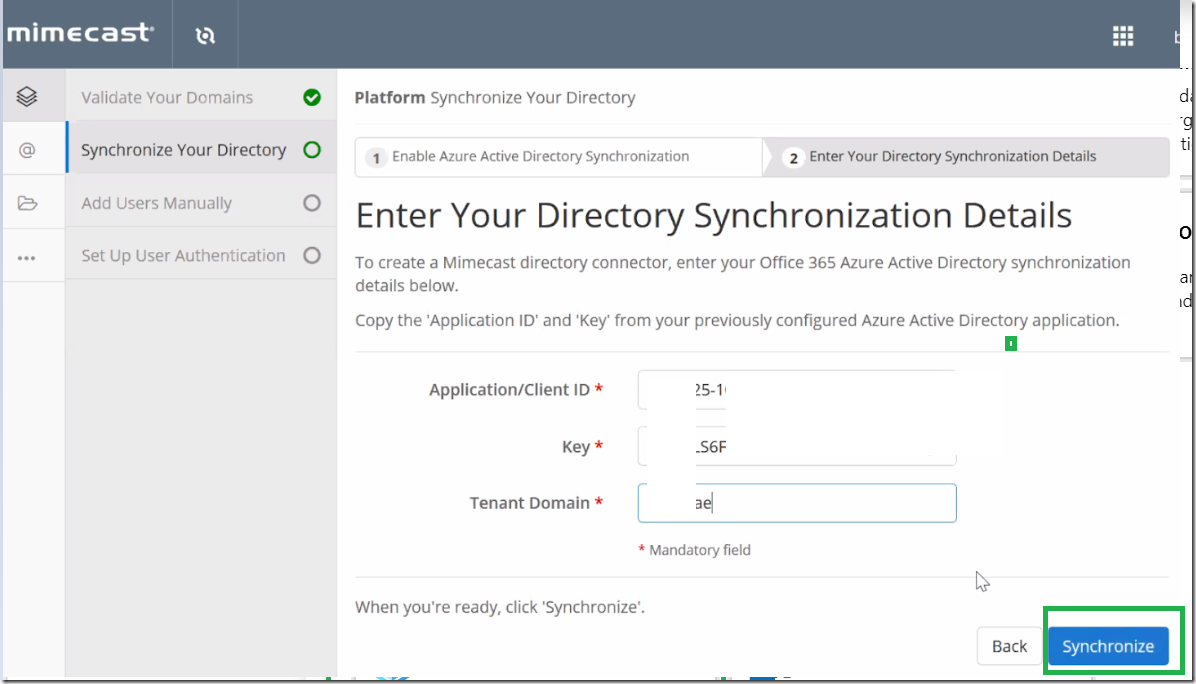
Now we need three things.
- Application/Client ID
- Key
- Tenant Domain
lets see how to configure them in the Azure Active Directory .
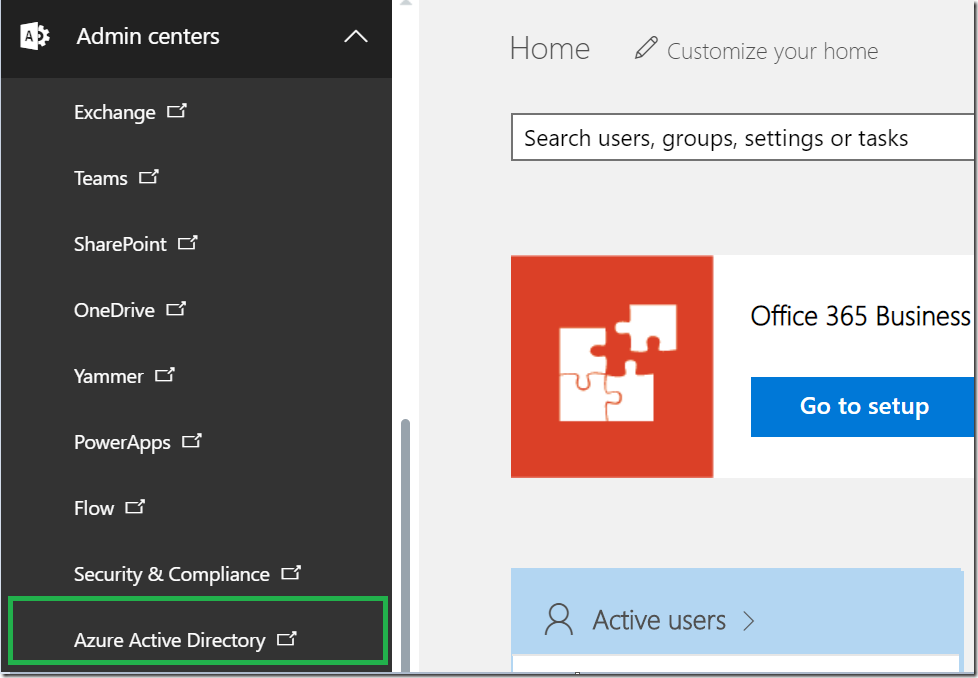
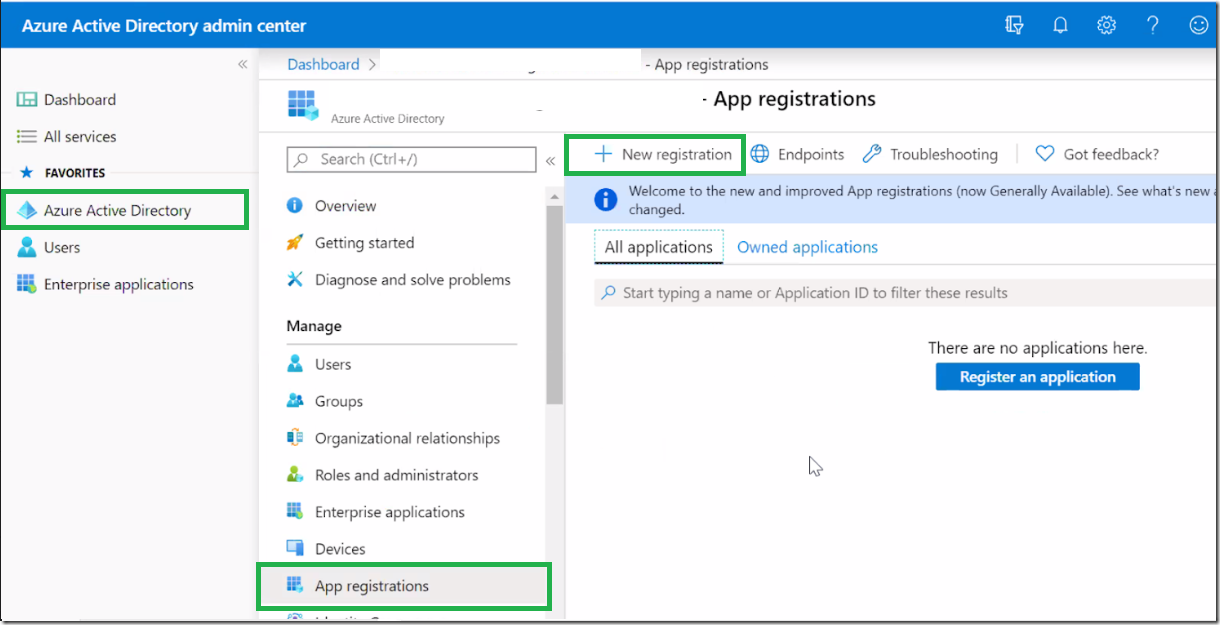
Log into Azure Active Directory Admin Center
Azure Active Directory – App Registrations – New Registration
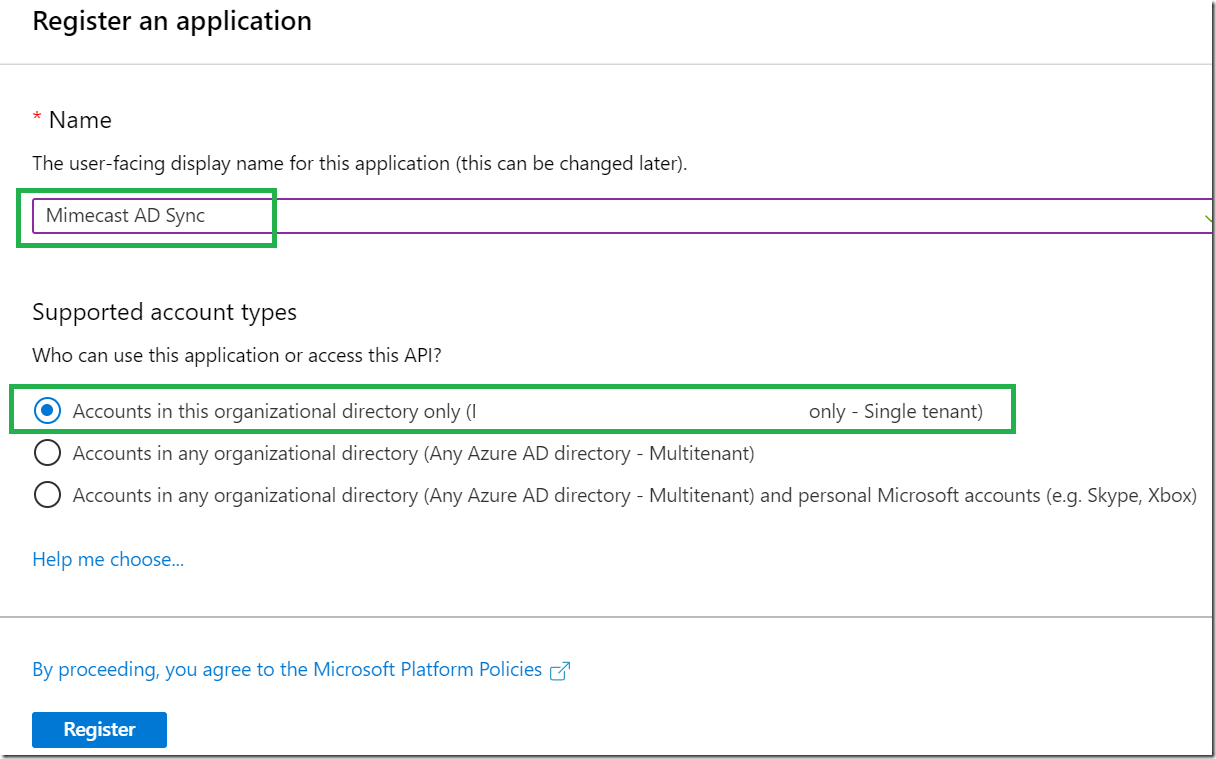
Enter a friendly Name _
Choose – Accounts in this organizational directory only (Azure365pro – Single tenant)
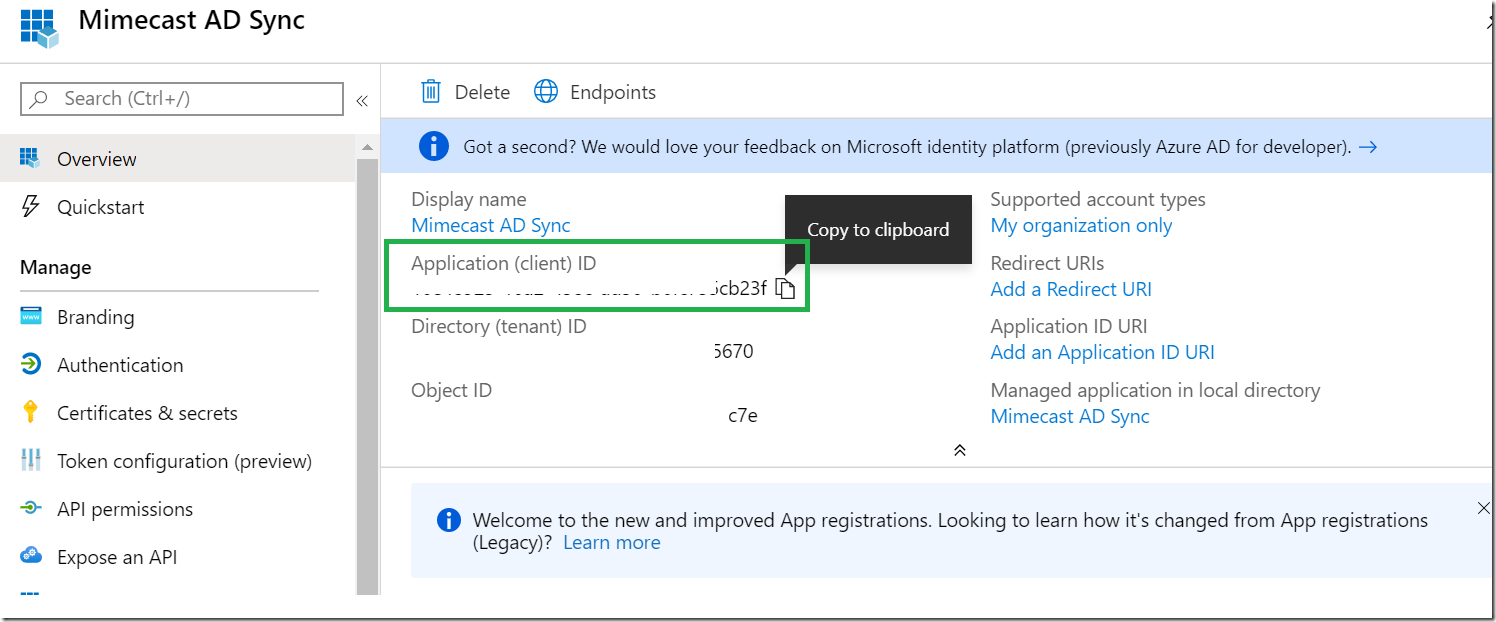
- Copy the Application (client) ID for Mimecast Console
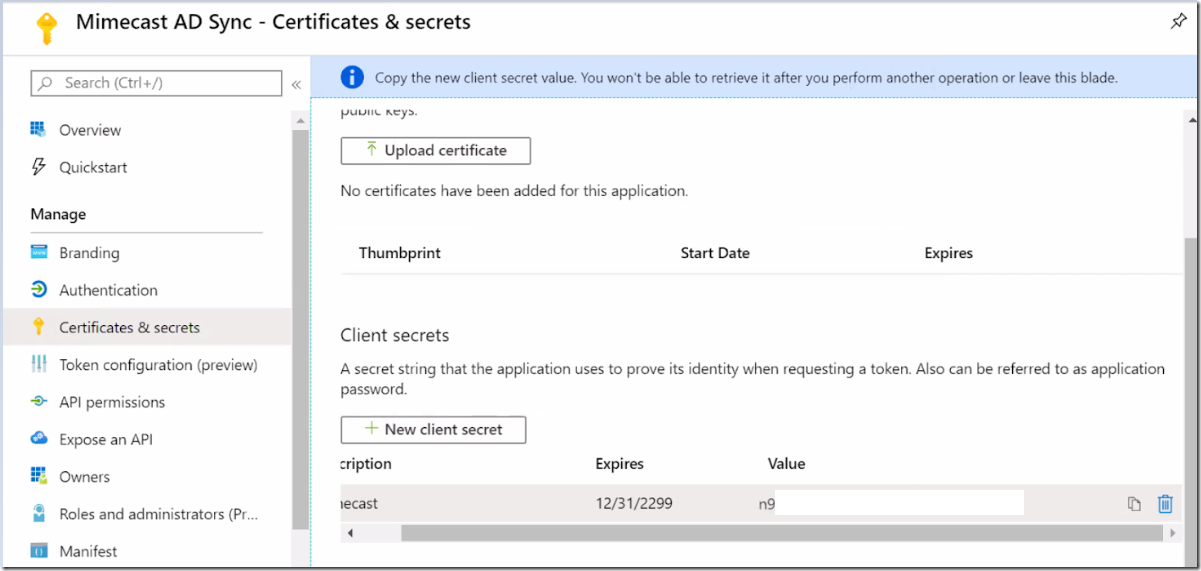
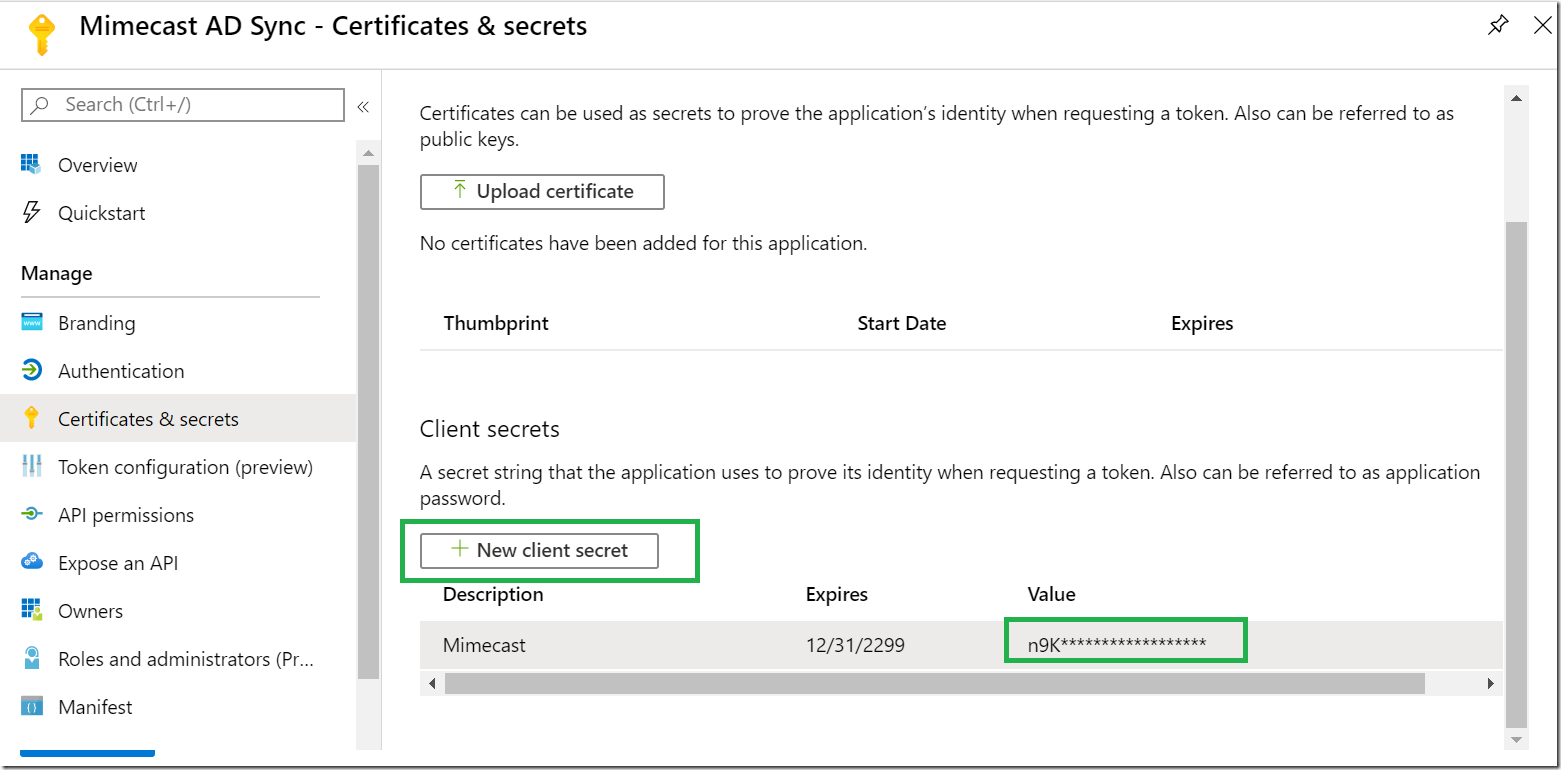
Click on Certificates and Secrets
Create Client Secret _ Copy the new Client Secret value. You won’t be able to retrieve it after you perform another operation or leave this blade.
So store the value in a safe place so that we can use (KEY) it in the mimecast console.
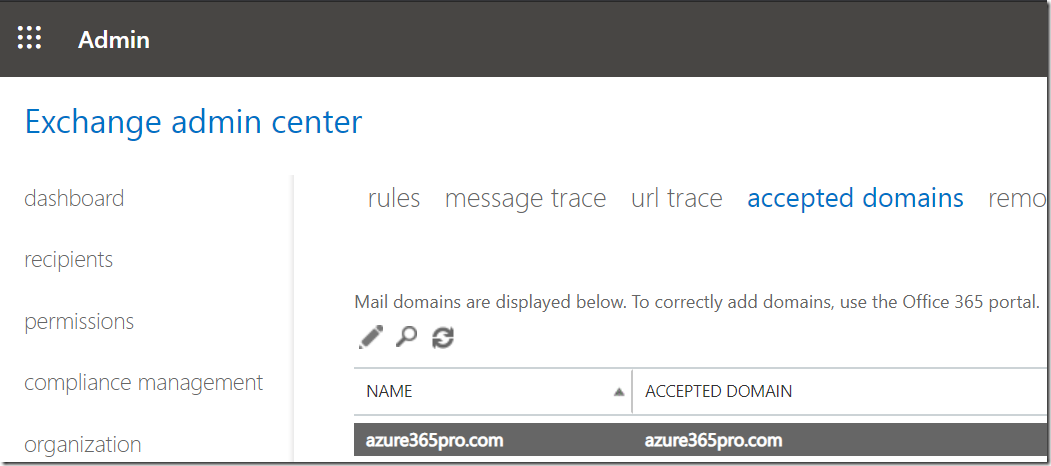
Get the default domain which is the tenant domain in mimecast console.
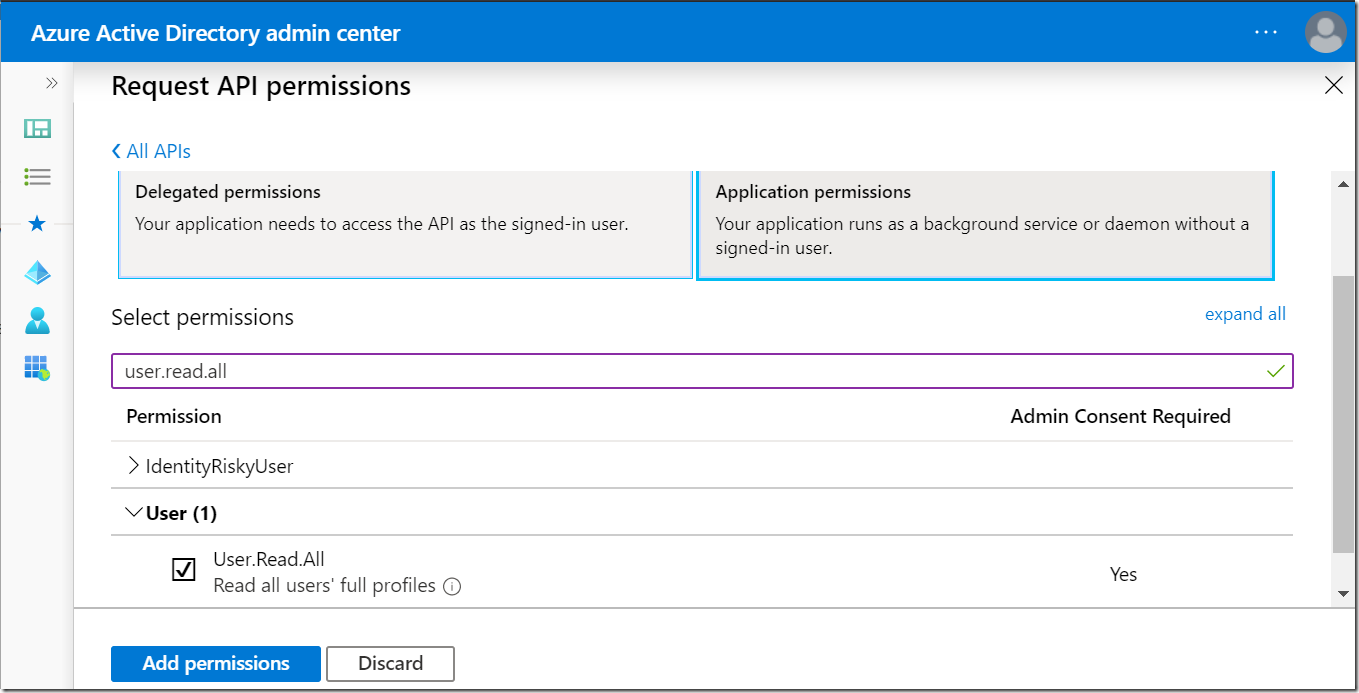
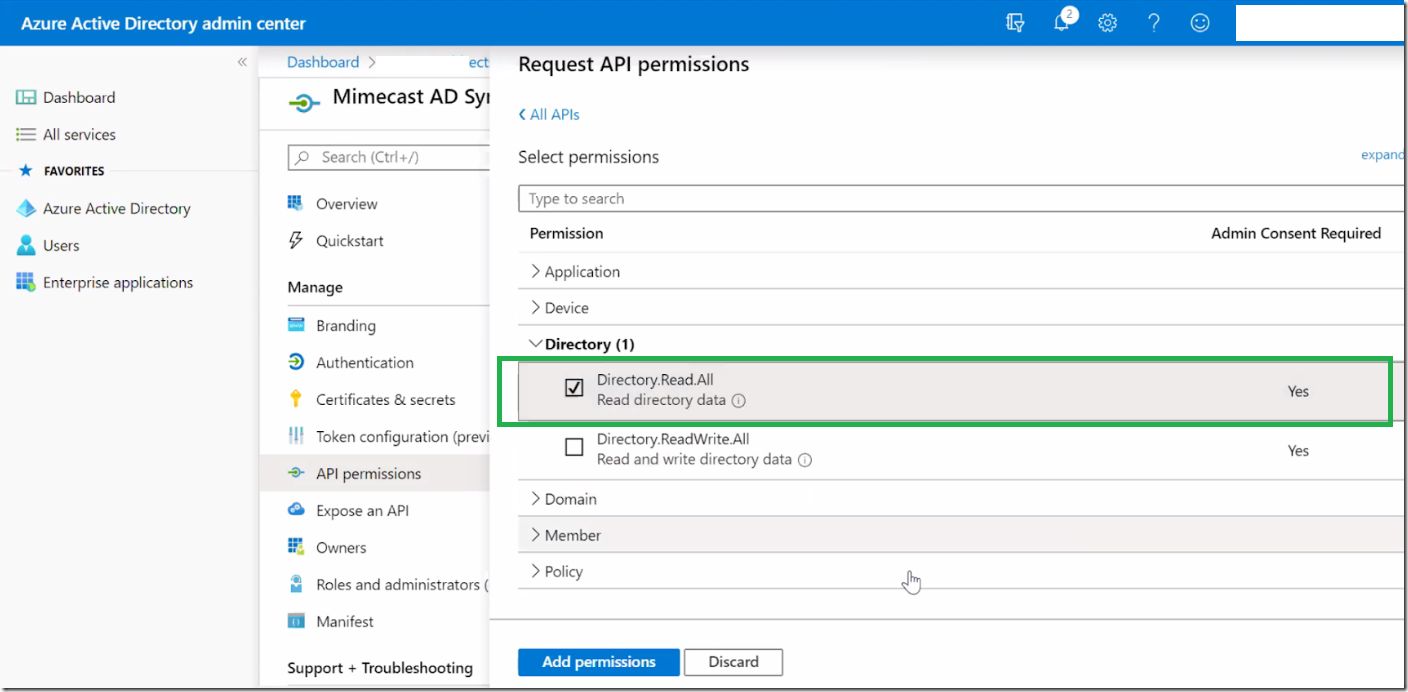
Now Add below permissions _
Microsoft Graph – Application Permissions – User.Read.All Read all users’ full profiles
Azure Active Directory Graph – Application Permissions – Directory.Read.All Read directory data
Azure Active Directory Graph – Delegated Permissions – User.Read.All Read all users’ full profiles
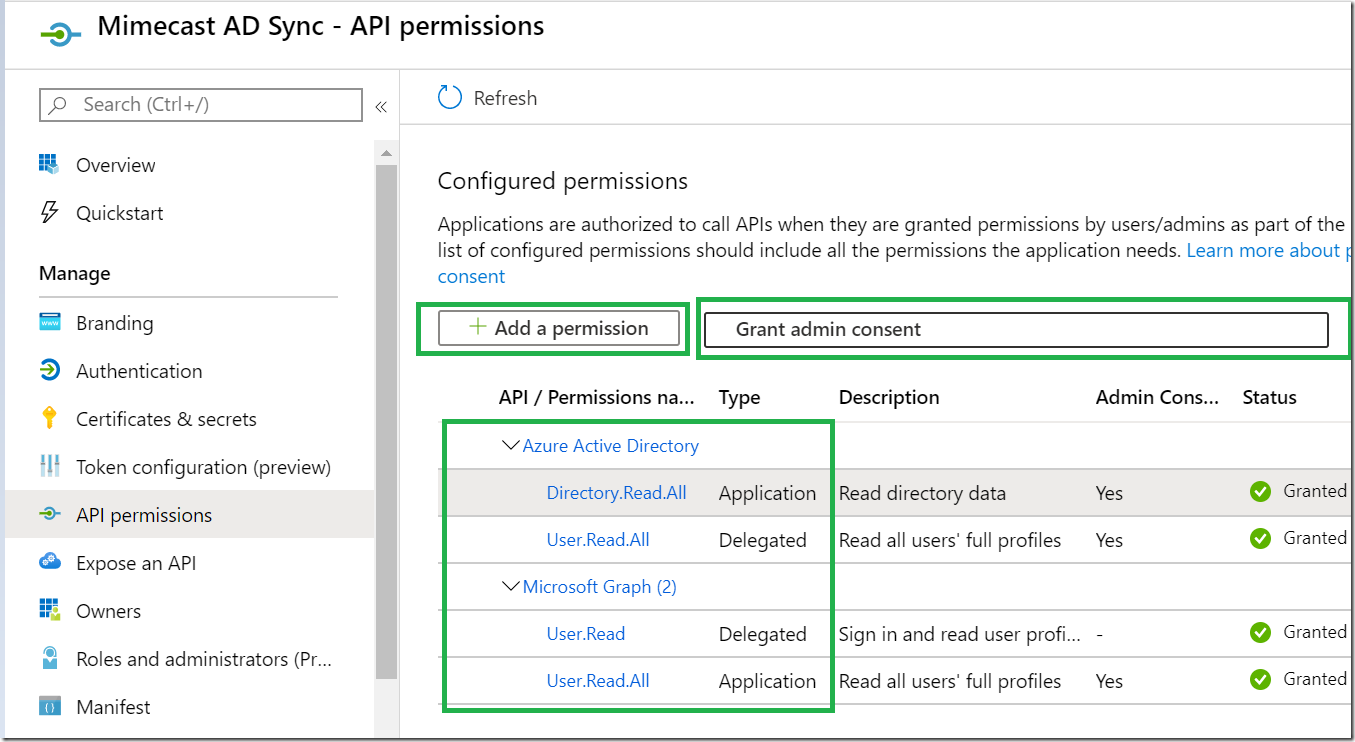
Samples _
In the End it should look like below. it will prepare for consent and Click on “Grant Admin Consent”
Once the permission is granted . Wait for few minutes
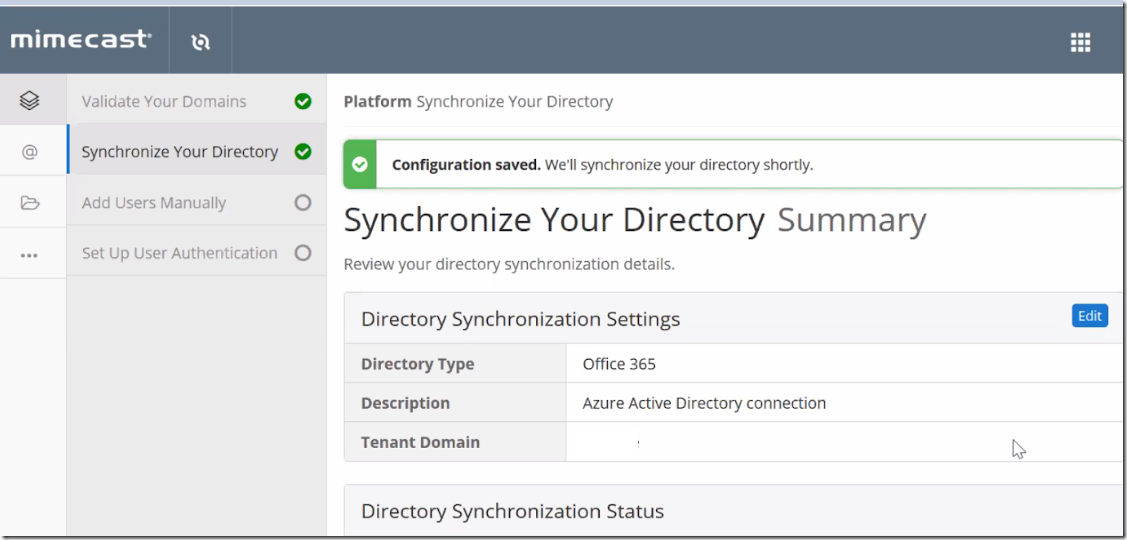
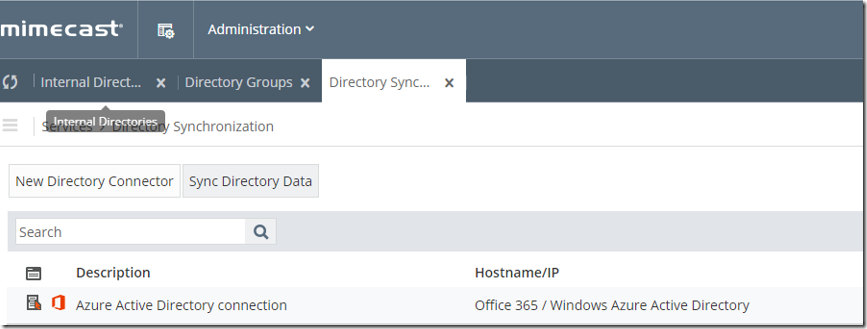
Now _ Get to the mimecast Admin Console fill in the details which we collected earlier and click on synchronize.
Now Synchronization is configured.
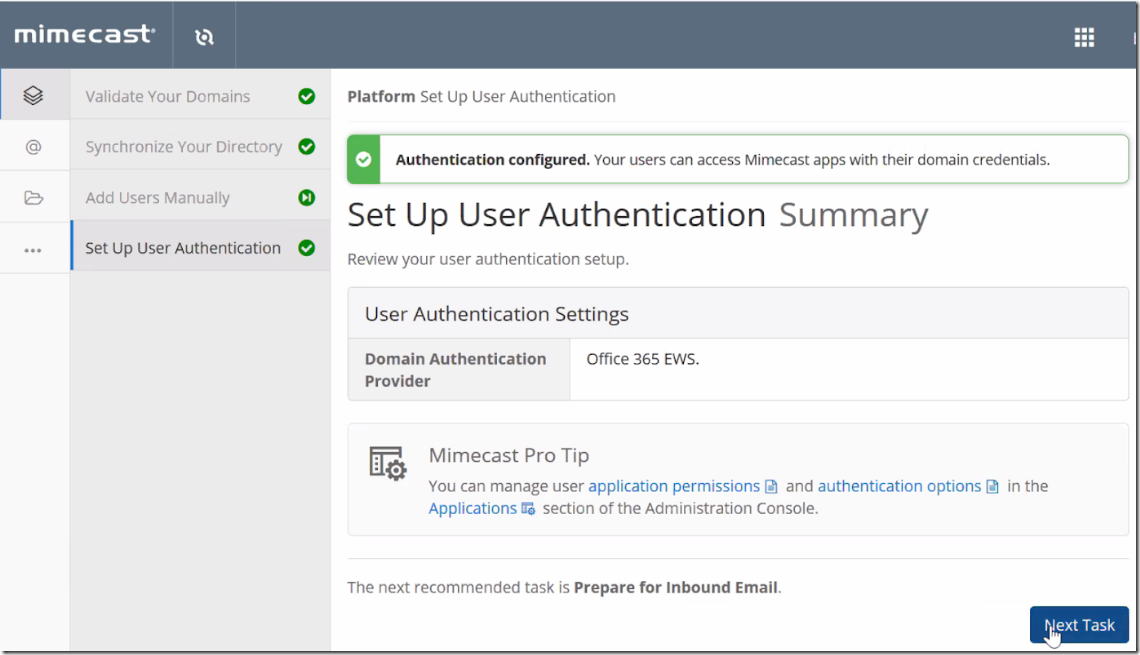
Choose Next Task to allow authentication for mimecast apps .
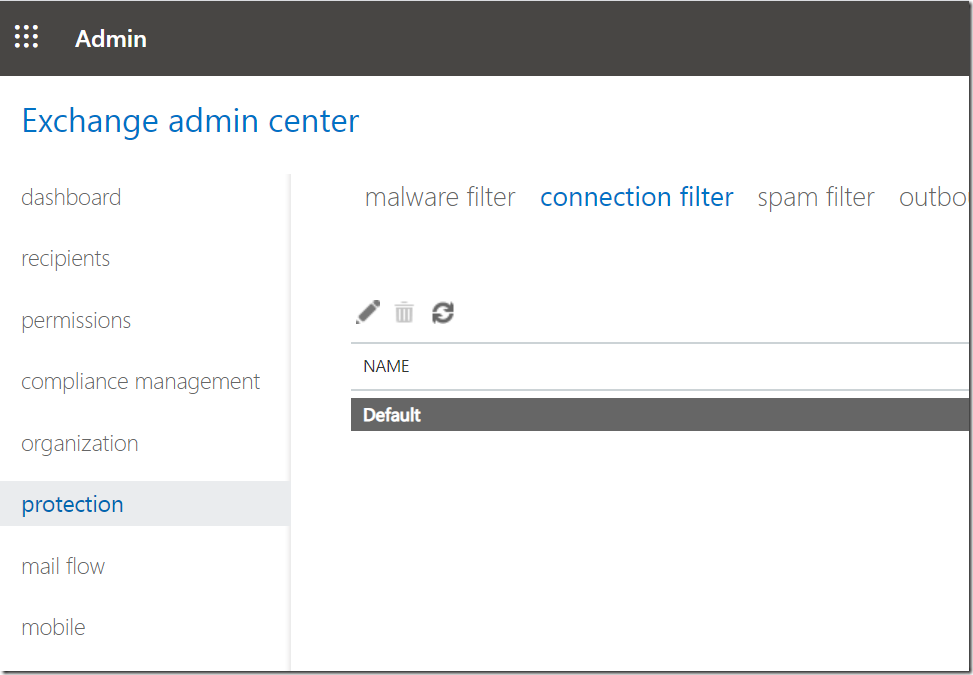
Now lets whitelist mimecast IPs in Connection Filter.
Login to Exchange Admin Center _ Protection _ Connection Filter
Choose Default _ Edit (Pen Icon)
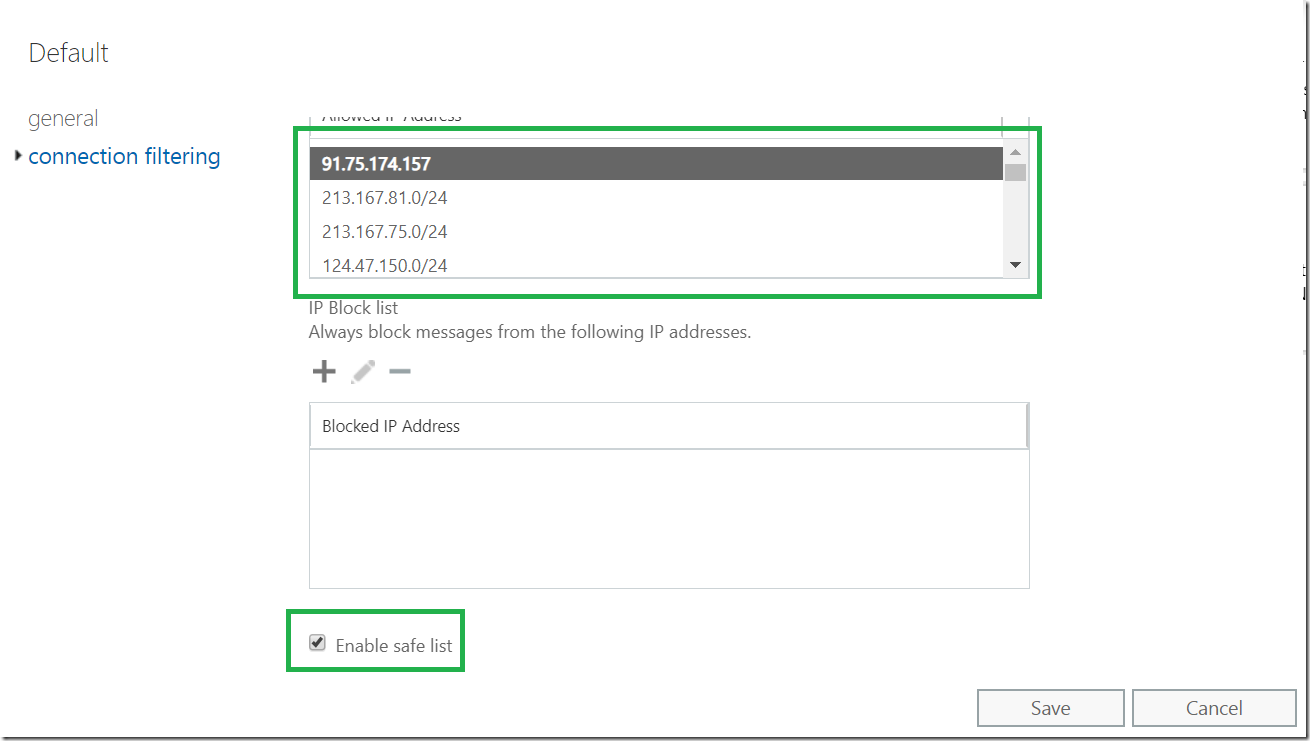
Now Choose Default Filter and Edit the filter to allow IP ranges . you can get from the mimecast console.
or you refer below link for updated IP ranges for whitelisting inbound mail flow.
and Check Enable Safe list.
https://community.mimecast.com/s/article/Adding-Network-Ranges-to-Office-365
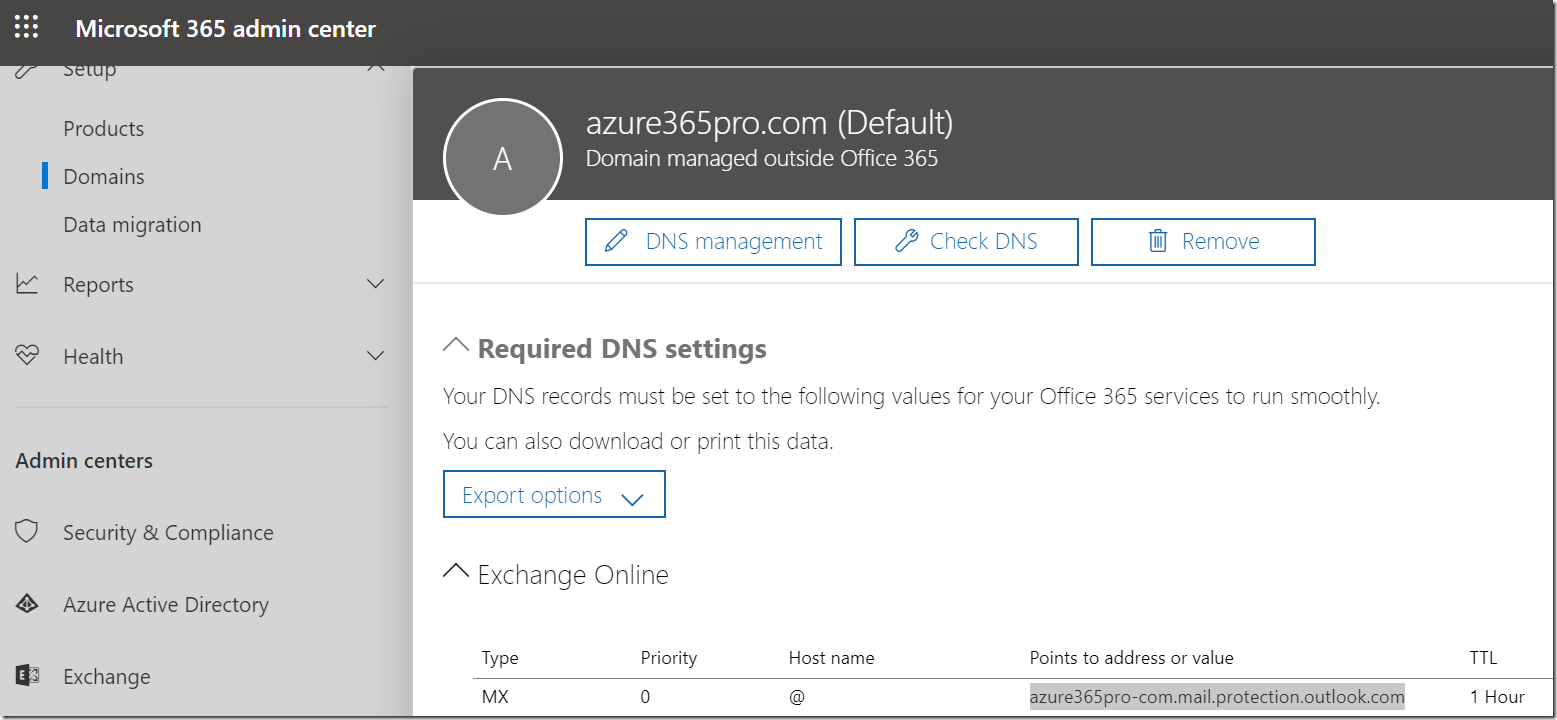
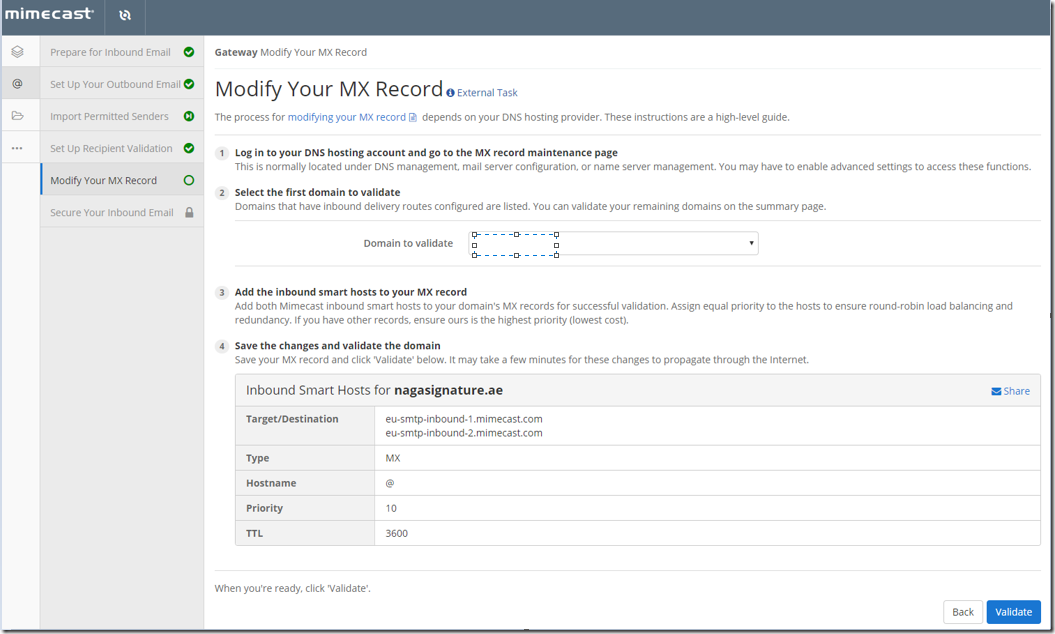
Get the mx value of the domain
Microsoft 365 Admin Center _ Domains _ MX value
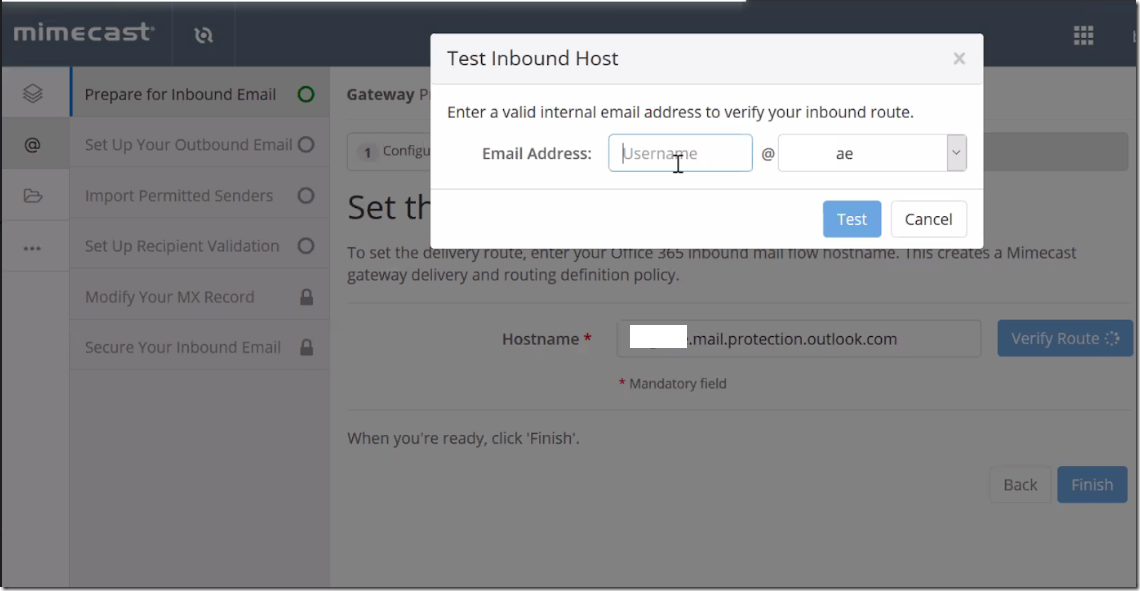
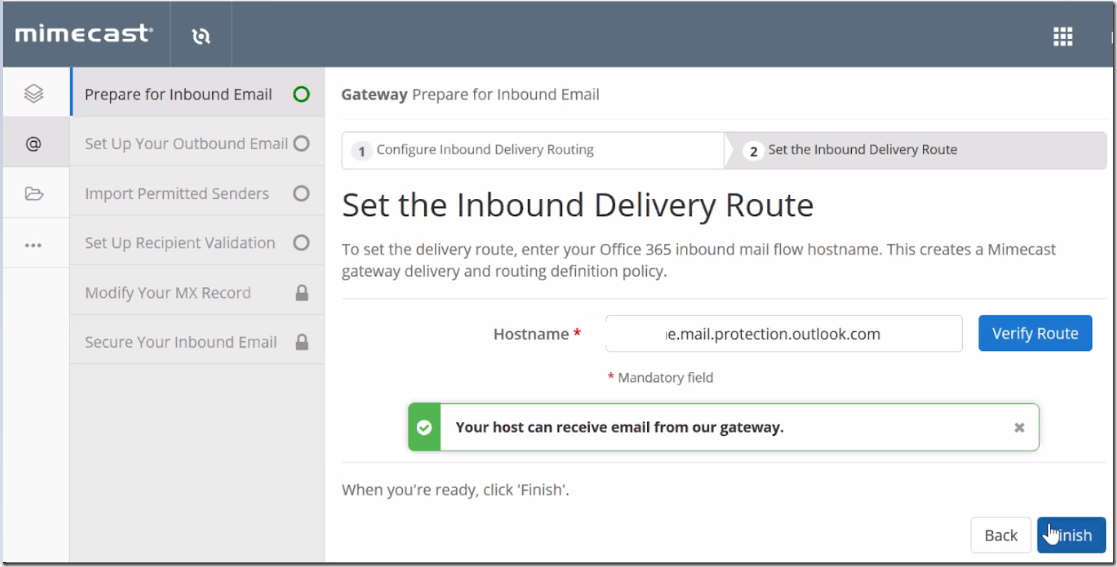
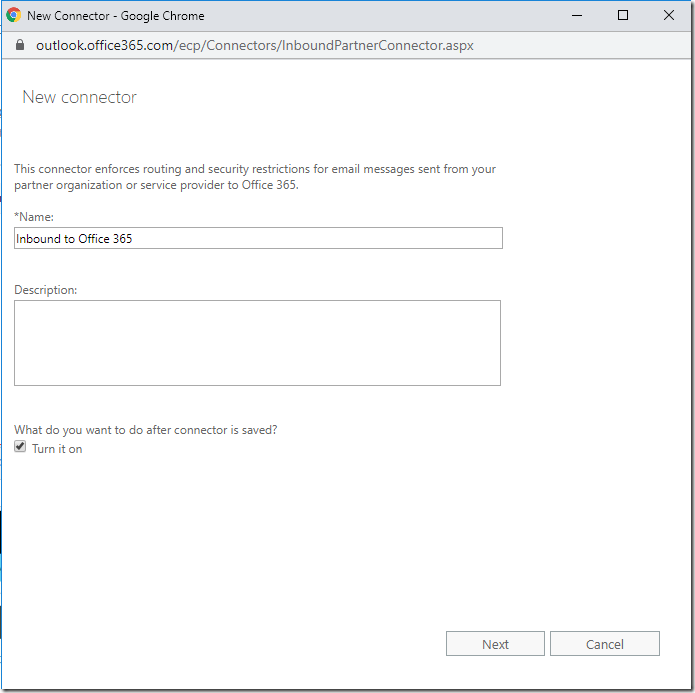
Now you can test the inbound mail flow.
Now inbound to Office 365 works fine.
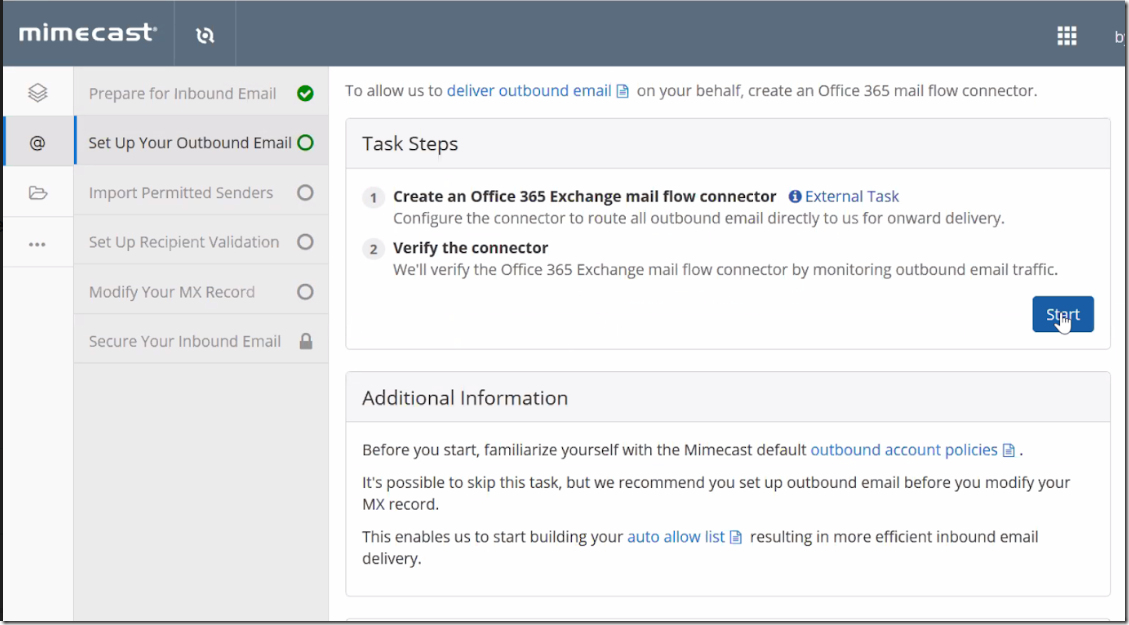
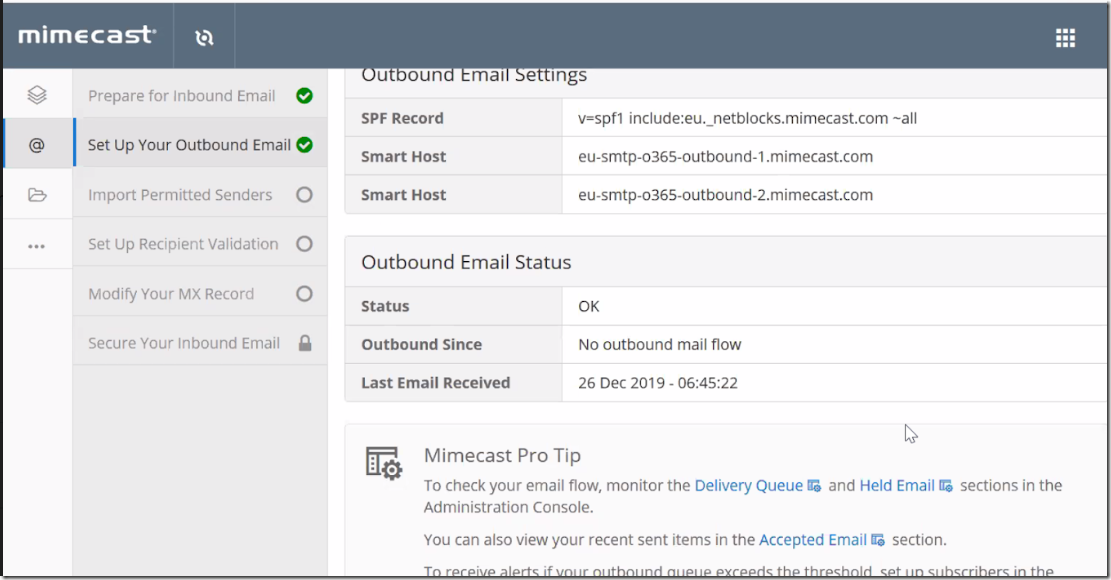
Lets do the outbound email now.
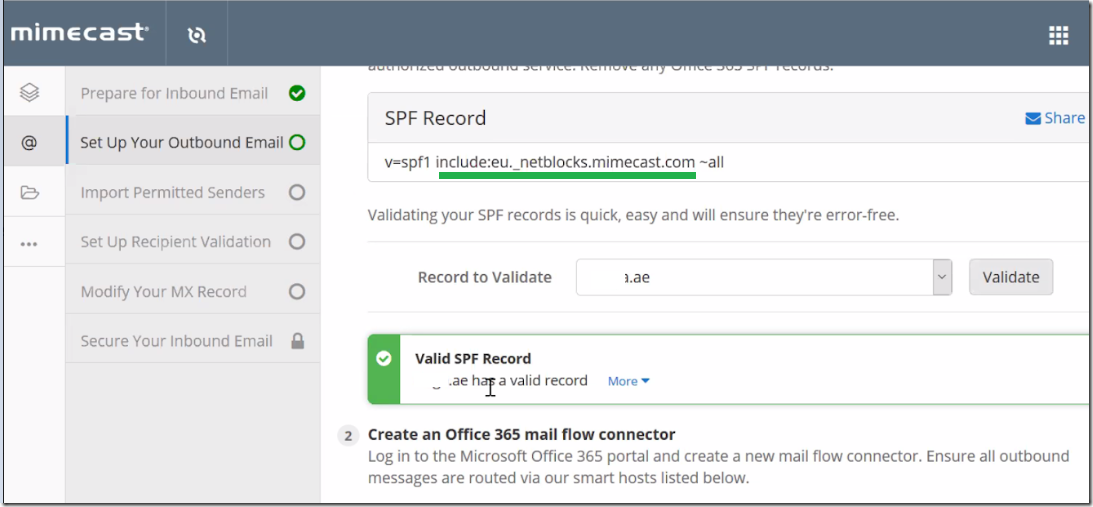
Configuring SPF.
In my case its a hybrid. So mails are going out via on-premise servers as well
So I added only include line in my existing SPF Record.as per the screenshot.
my spf looks like v=spf1 include:eu._netblocks.mimecast.com a:mail.azure365pro.com ip4:148.50.16.90 ~all
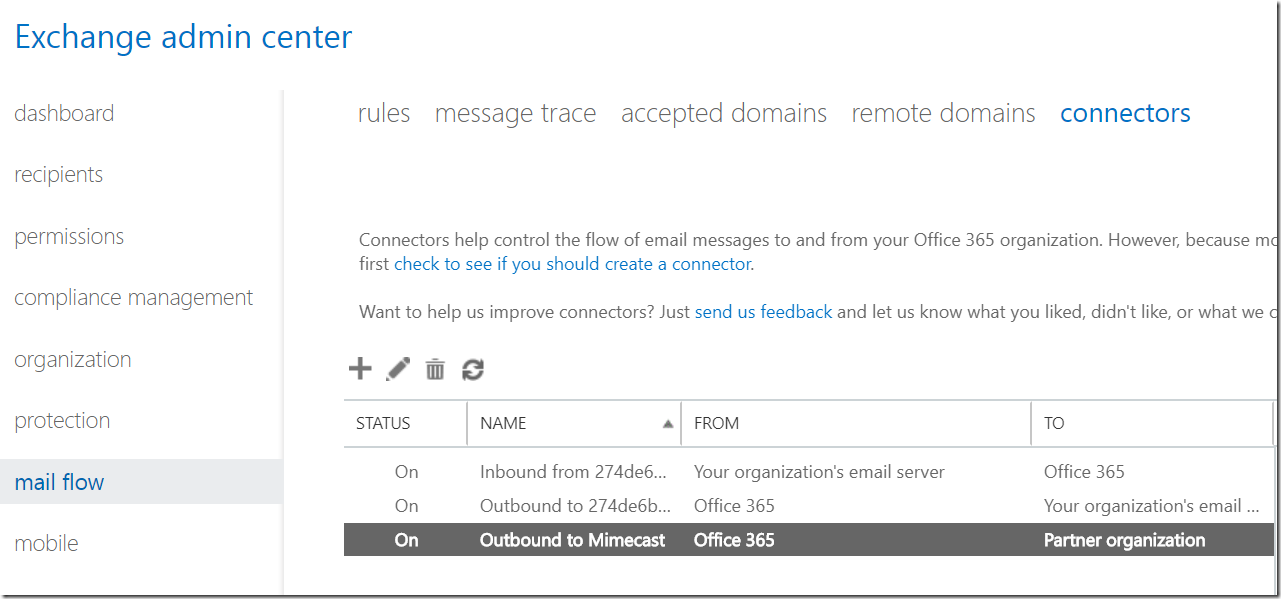
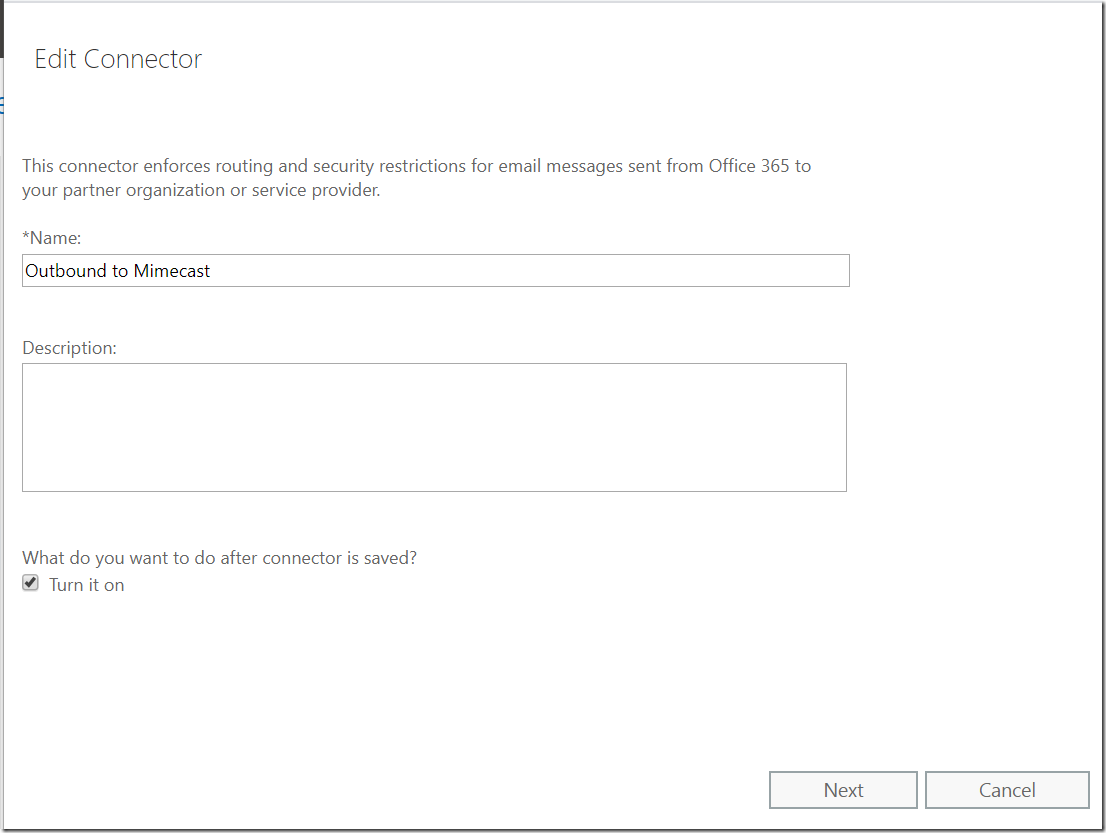
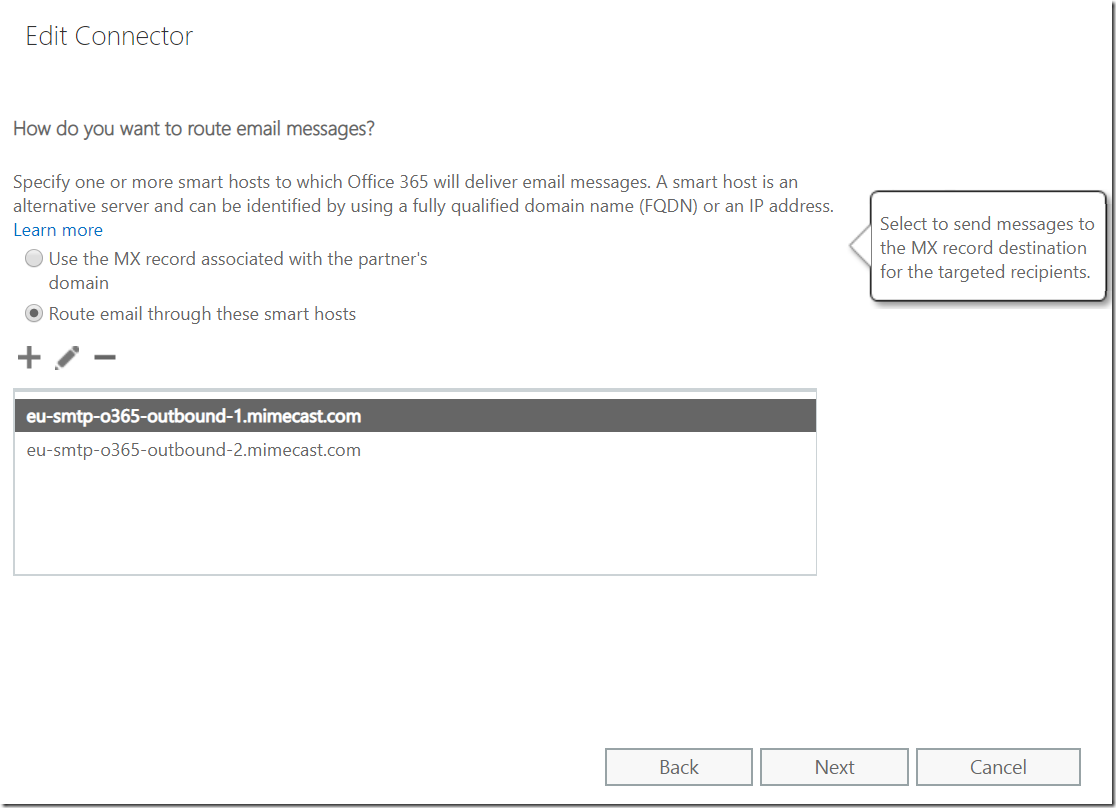
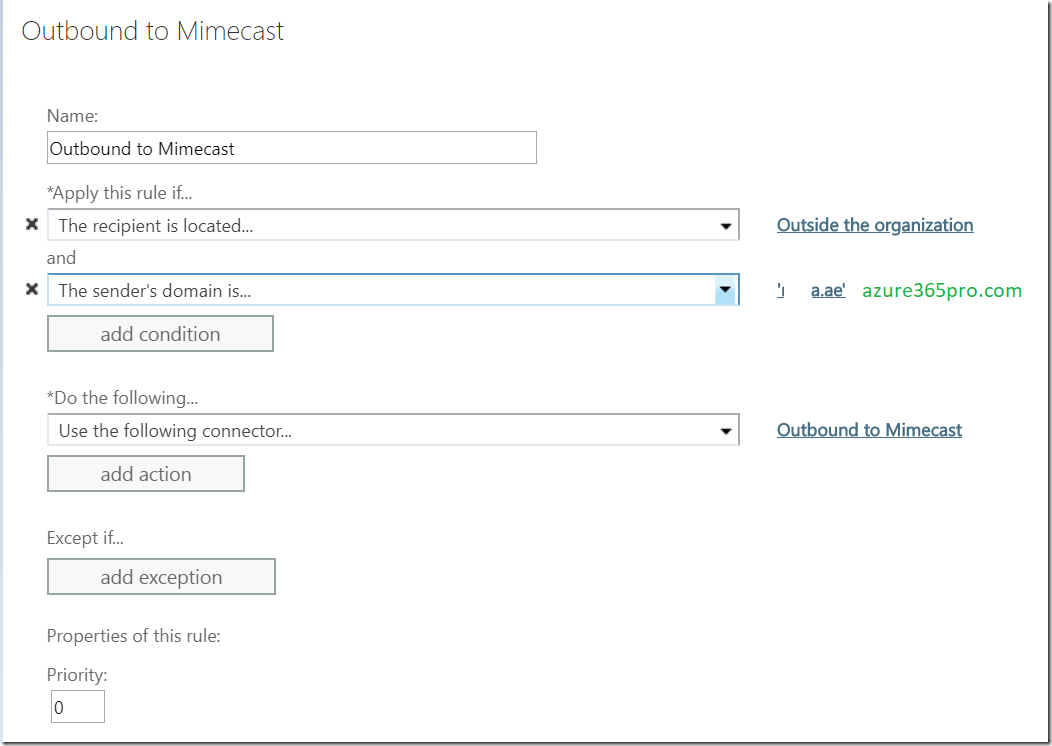
Lets create a connector to force all outbound emails from Office 365 to Mimecast
At this point we will create connector only . Only the transport rule will make the connector active.
Outbound to Mimecast
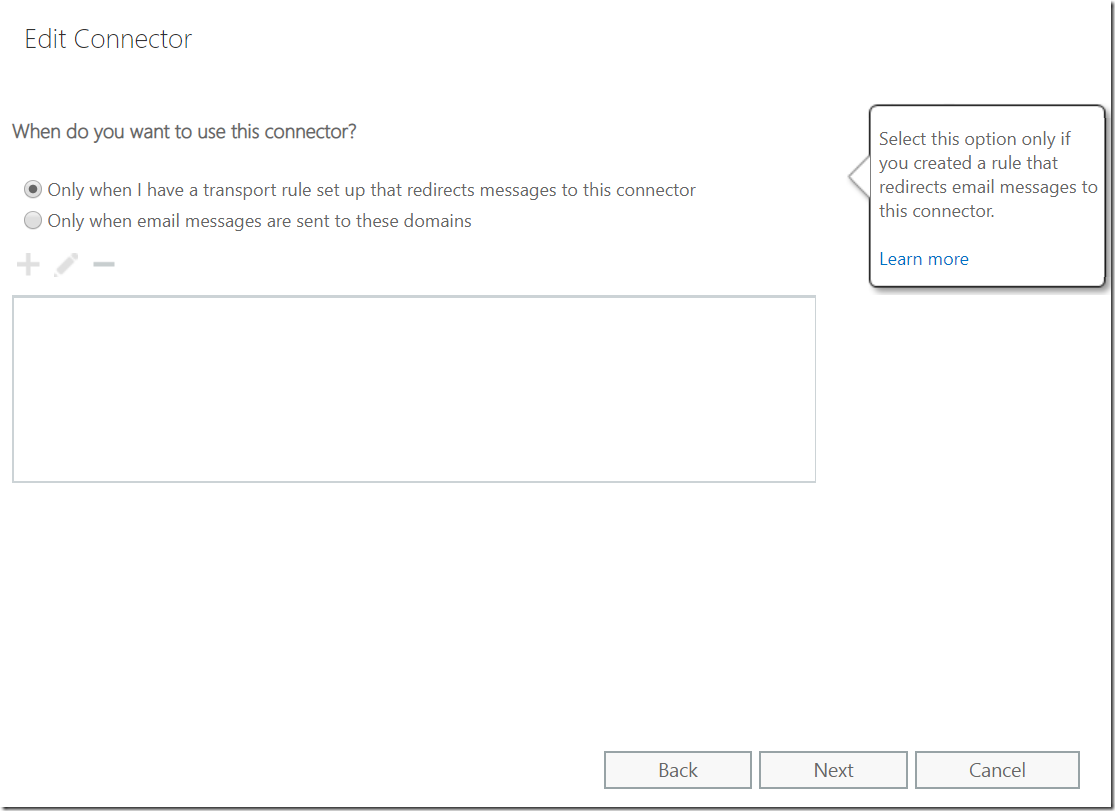
Choose – Only when i have a transport rule set up that redirects messages to this connector
Choose – Next
- Route email through these smart hosts
Get the smart hosts via mimecast administration console.
Leave it default.
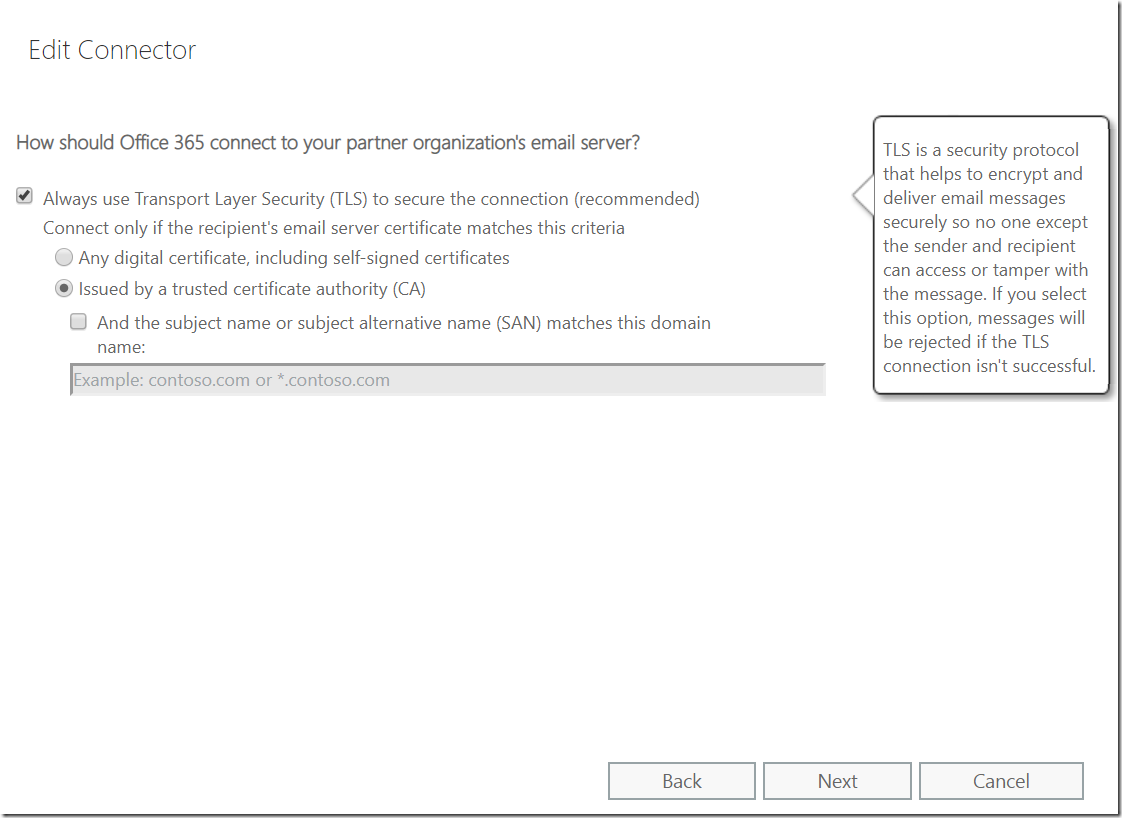
Choose “Always use Transport Layer Security (TLS) to secure the connection (recommended)
Issued by a trusted certificate authority (CA)
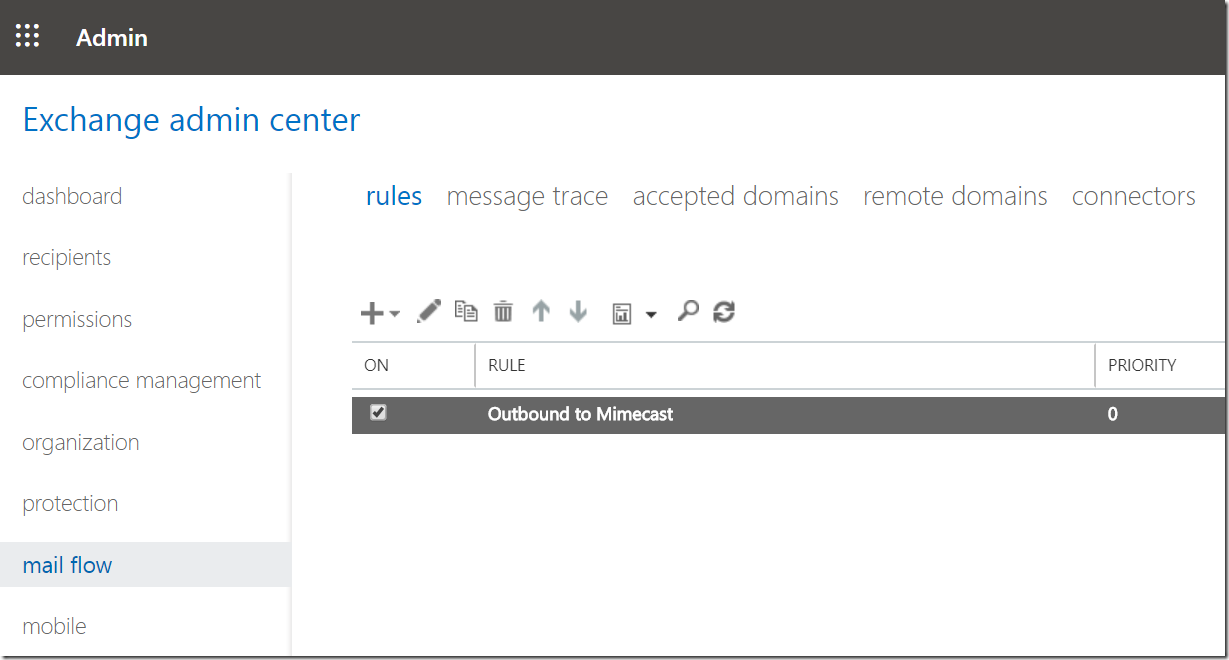
Now create a transport rule to utilize this connector.
Once you turn on this transport rule . your mail flow will start flowing through mimecast. Its recommended to move your outbound mail flow first for a week so that it can do the learning then move your mx to mimecast to have very few false positives. Still its going to work great if you move your mx on the first day.
Now you are good to move your MX record.
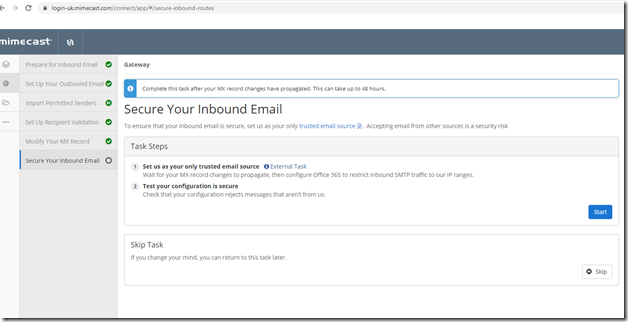
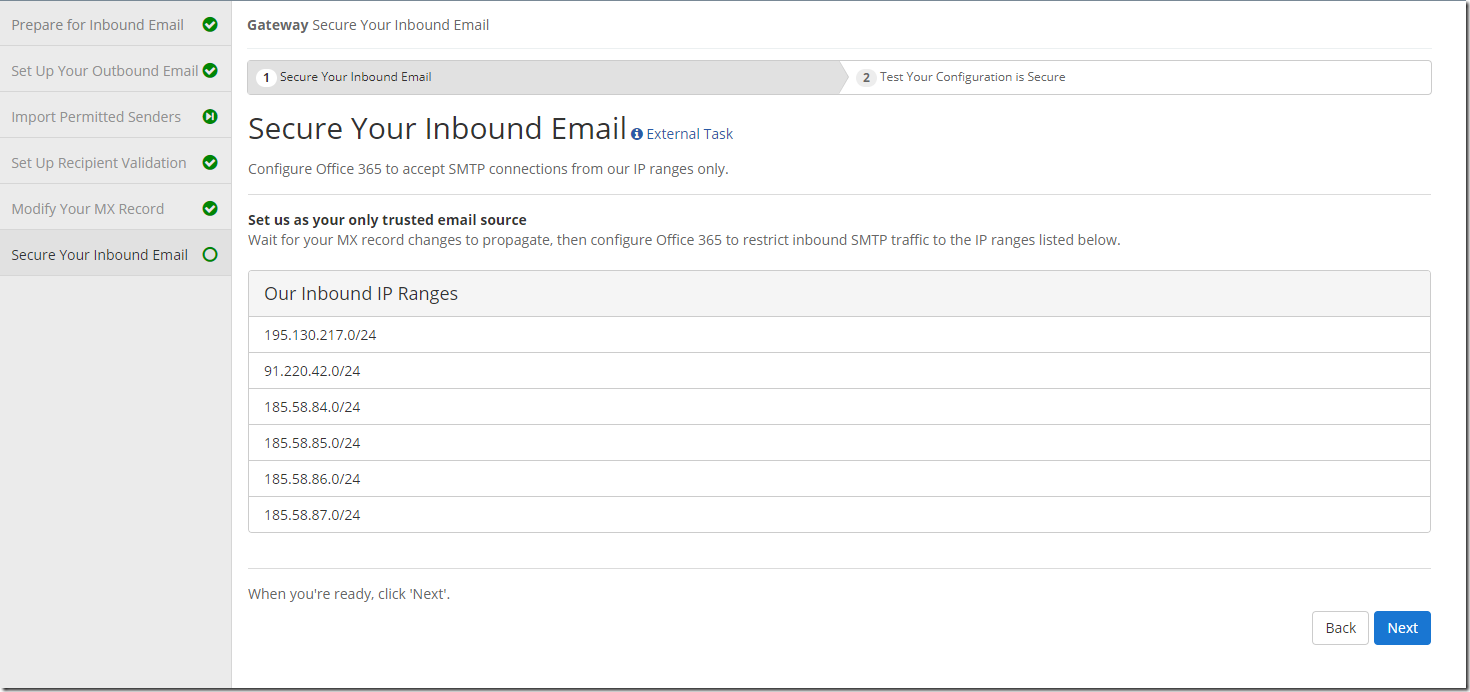
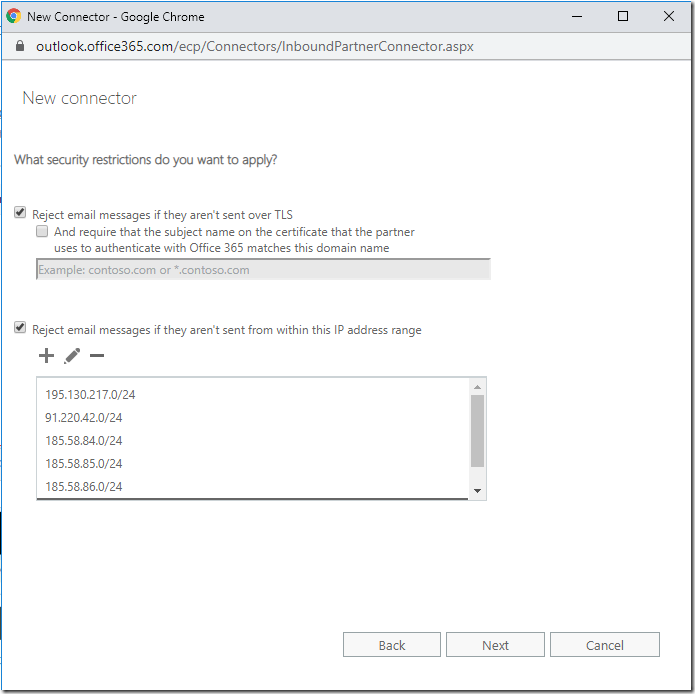
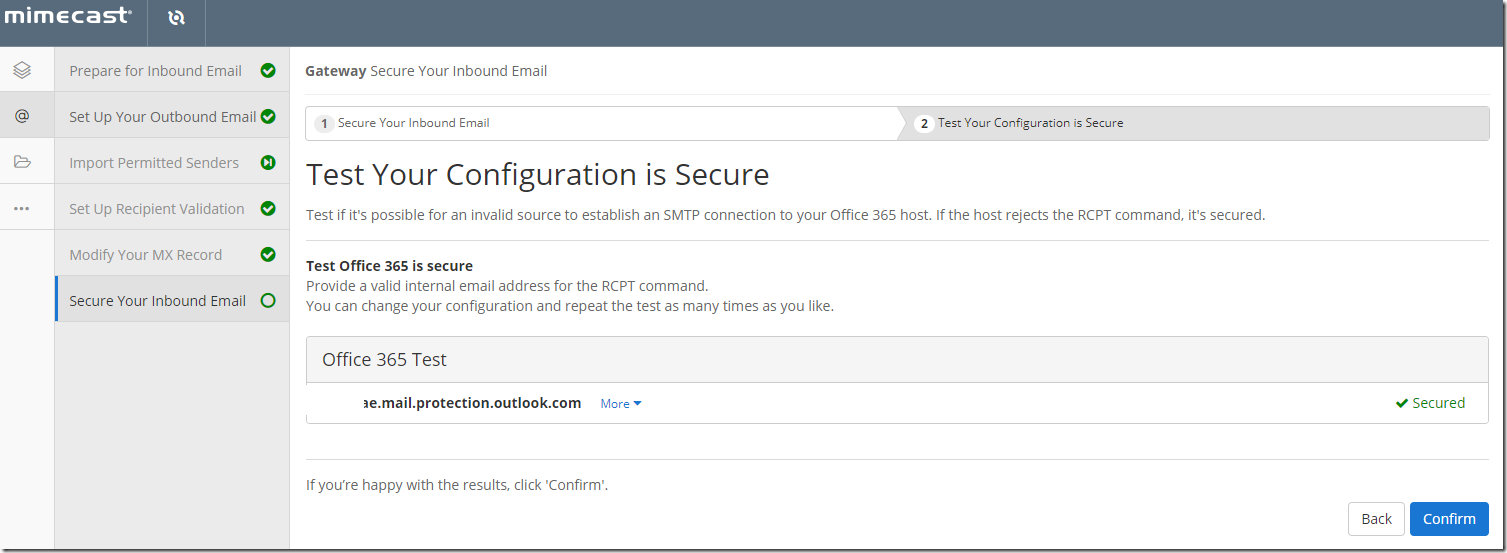
Now Secure your inbound email
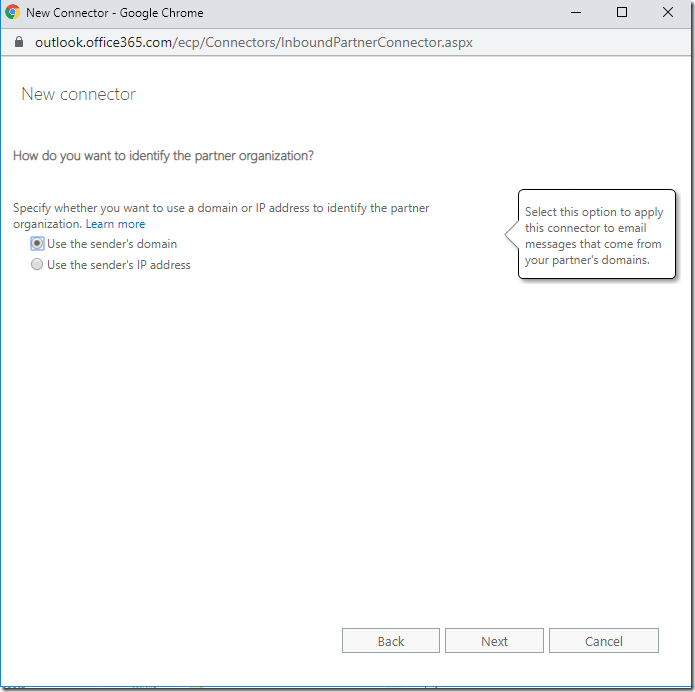
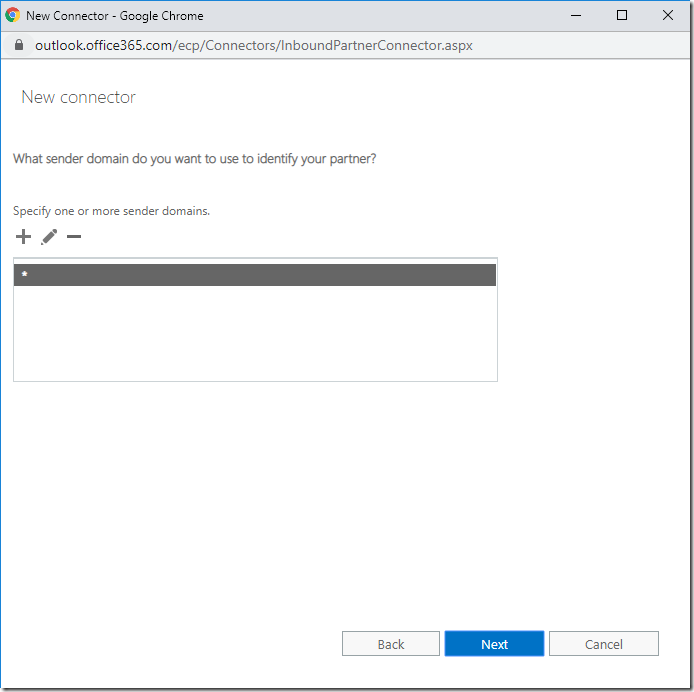
Use the Sender’s domain
Add the listed IP ranges
Whenever you wish to sync Azure Active Director Data



Thanks, I used part of your guide to setup the Mimecast / Azure App permissons.
You are most welcome!