Users are not able to authenticate to VPN using Azure Multi-Factor Authentication while working outside the office. We found certificate provided for automatic NPS by Azure MFA Extension requires re-registration from azure active directory tenant.
Technology: Azure AD Multi-Factor Authentication
Servers Involved: NPS, Active Directory, Certificate Authority
Tools Utilized: NPS Azure MFA Extension, PowerShell Module
Activity Followed to diagnose and provide a solution for the case is described below:
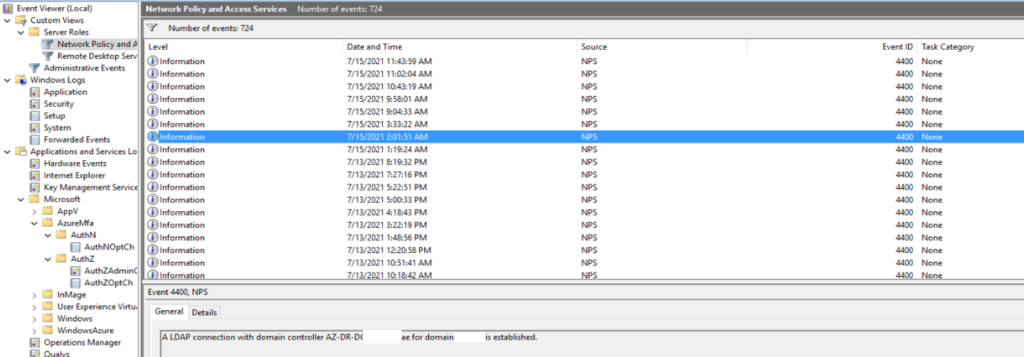
Analyzed the NPS event logs for Authentication, Identified the issues for user rejection on Azure MFA
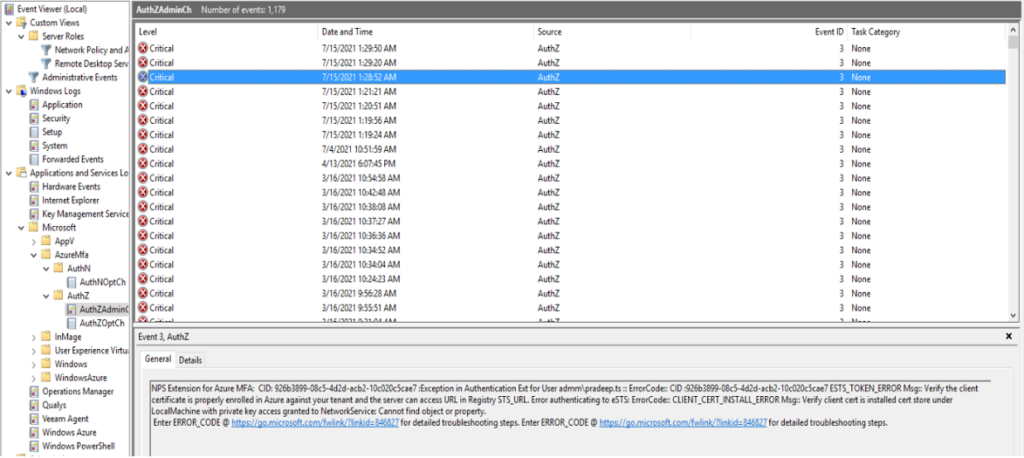
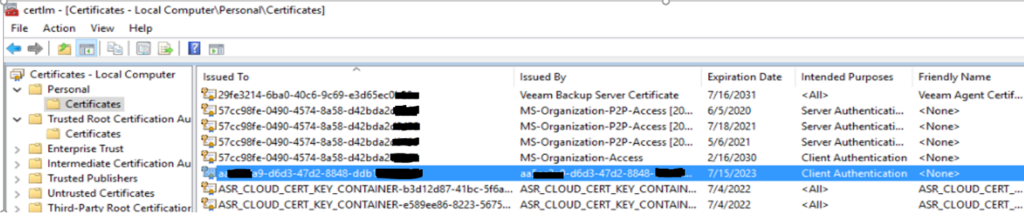
Found the certificate from the azure tenant is not renewed automatically.
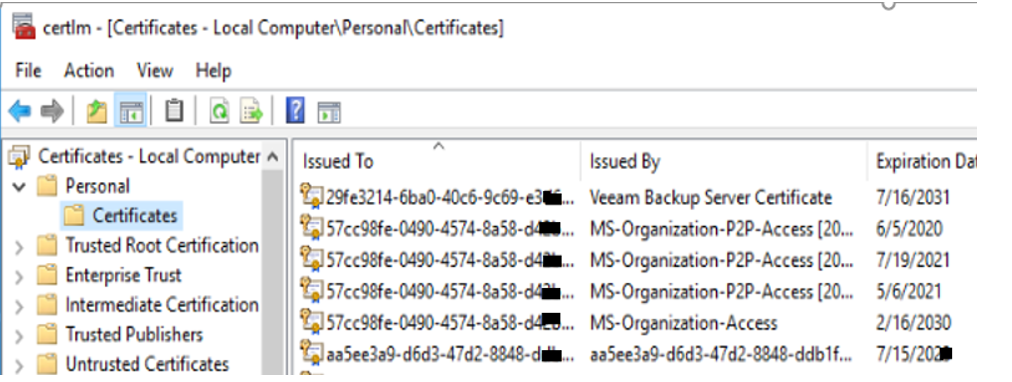
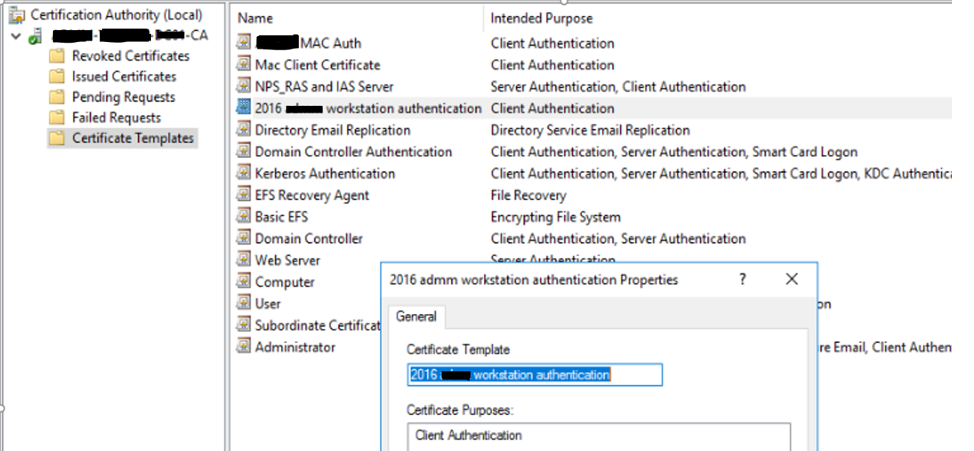
Removed the Azure AD Tenant certificate from NPS manually and created a new client certificate template from CA for regeneration of client certificate where Azure tenant can check the activity of the client.
Reinstalled the MFA extension on the NPS server
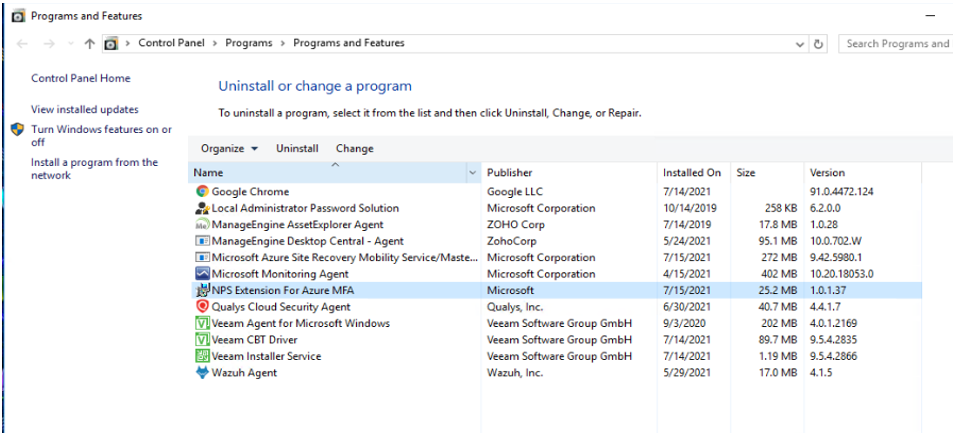
After Reinstalling the NPS Azure MFA extension, Installed all the required Repository for PowerShell modules which can lead us t register the NPS server again with azure active directory tenant
- Below are the Scripts, we performed.
PS C:\Program Files\Microsoft\AzureMfa\Config> Register-PSRepository -Name PSGallery1 -SourceLocation https://www.powershellgallery.com/api/v2/ -InstallationPolicy Trusted PS C:\Program Files\Microsoft\AzureMfa\Config> Set-PSRepository -Name PSGallery -SourceLocation https://www.powershellgallery.com/api/v2/ -InstallationPolicy Trusted PS C:\Program Files\Microsoft\AzureMfa\Config> Get-PSRepository Name InstallationPolicy SourceLocation ---- ------------------ -------------- PSGallery Untrusted https://www.powershellgallery.com/api/v2 PSGallery1 Trusted https://www.powershellgallery.com/api/v2/
Deleted the untrusted PowerShell repository
PS C:\Program Files\Microsoft\AzureMfa\Config> Unregister-PSRepository -Name "PSGallery" PS C:\Program Files\Microsoft\AzureMfa\Config> Get-PSRepository Name InstallationPolicy SourceLocation ---- ------------------ -------------- PSGallery1 Trusted https://www.powershellgallery.com/api/v2/
Ran the MFA extension script to pull the certificate from azure ad
PS C:\Program Files\Microsoft\AzureMfa\Config> .\AzureMfaNpsExtnConfigSetup.ps1
Authenticated with the same key and id
PS C:\Program Files\Microsoft\AzureMfa\Config> .\AzureMfaNpsExtnConfigSetup.ps1 VERBOSE: Using the provider 'PowerShellGet' for searching packages. VERBOSE: The -Repository parameter was not specified. PowerShellGet will use all of the registered repositories. VERBOSE: Getting the provider object for the PackageManagement Provider 'NuGet'. VERBOSE: The specified Location is 'https://www.powershellgallery.com/api/v2/' and PackageManagementProvider is 'NuGet'. VERBOSE: Searching repository 'https://www.powershellgallery.com/api/v2/FindPackagesById()?id='MSOnline'' for ''. VERBOSE: Total package yield:'1' for the specified package 'MSOnline'. VERBOSE: Performing the operation "Install-Module" on target "Version '1.1.183.57' of module 'MSOnline'". VERBOSE: The installation scope is specified to be 'AllUsers'. VERBOSE: The specified module will be installed in 'C:\Program Files\WindowsPowerShell\Modules'. WARNING: Version '1.1.183.17' of module 'MSOnline' is already installed at 'C:\Program Files\WindowsPowerShell\Modules\MSOnline\1.1.183.17'. To install version '1.1.183.57', run Install-Module and add the -Force parameter, this command will install version '1.1.183.57' in side-by-side with version '1.1.183.17'. Connecting to Microsoft Azure. Please sign on as a tenant administrator. Starting Azure MFA NPS Extension Configuration Script Tenant ID currently registered with Azure MFA NPS Extension is: aa5e***9-d6d3-47d2-8848-***** Enter new Tenant ID to change or press Enter to keep the current value: Generating client certificate Thumbprint Subject ---------- ------- 6F0E906DE97D71FBBCCB0DFEE9937A400F4B27CA CN= aa5e***9-d6d3-47d2-8848-*****, OU=Microsoft NPS Extension Client Certificate successfully generated Client Certificate associated with Service Principal: 98**6a1-7f43-403b-***** Starting registry updates Completed registry updates Client certificate : CN= aa5e***9-d6d3-47d2-8848-*****, OU=Microsoft NPS Extension successfully associated with Azure MFA NPS Extension for Tenant ID aa5e***9-d6d3-47d2-8848-***** Granting certificate private key access to NETWORK SERVICE Successfully granted to NETWORK SERVICE Restarting Network Policy Server (ias) service WARNING: Waiting for service 'Network Policy Server (ias)' to stop... WARNING: Waiting for service 'Network Policy Server (ias)' to stop... Configuration complete. Press Enter to continue...:
you can see the Client Certificate successfully generated.
Client Certificate successfully generated Client Certificate associated with Service Principal: 98**6a1-7f43-403b-*****
Re-registered the NPS server for a connection establishment with DC where the new establishment is connected successfully and obtained with active directory registration
New azure MFA Tenant certificate generated successfully and registered with Azure AD Tenant.
Users started receiving Azure Multi-Factor Authentication Prompts.


