Let’s see how to configure single sign-on with SAP Success Factor as there is some incorrect documentation available on the internet also, every environment is different, Like using employee ID as user name and using email as the username is straightforward, but most of the SAP-based environments are using employee ID as the user name.
As you might know, SAP provides demo instances only to partners. Getting hold of trial instances is not a straightforward process.
In this scenario, we will cover that the Identity Provider will be Azure Active Directory and the Service provider will be SAP Success factor. Let’s see how to achieve seamless sign-on for users.
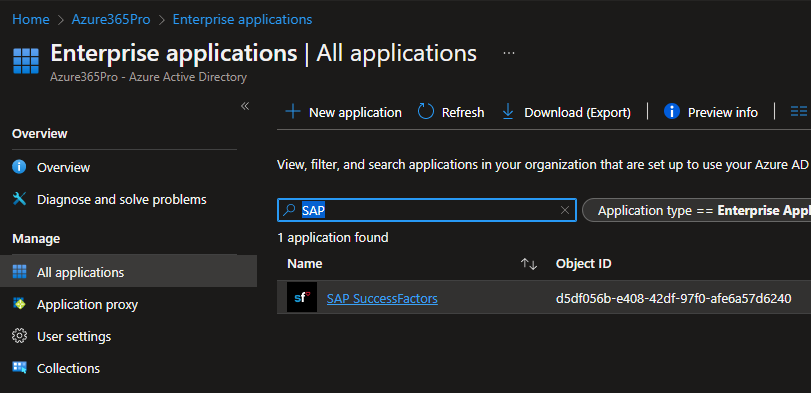
Register SAP Success Factor Enterprise Application from Azure Active Directory.
Finding these details for your instance was quite challenging, As there are a lot of tenant types in SAP Success Factor.
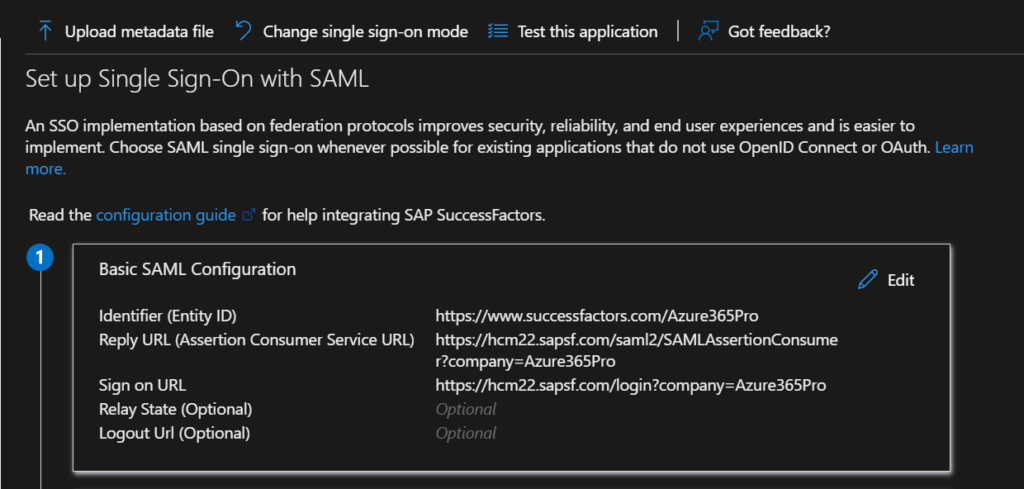
Reference URLs helped me find the Identified (Entity ID) / Reply (Assertion Consumer Service URL and Sign-on URL for my specific SAP Success Factor instance.
https://userapps.support.sap.com/sap/support/knowledge/E/2707993
https://userapps.support.sap.com/sap/support/knowledge/en/2747798
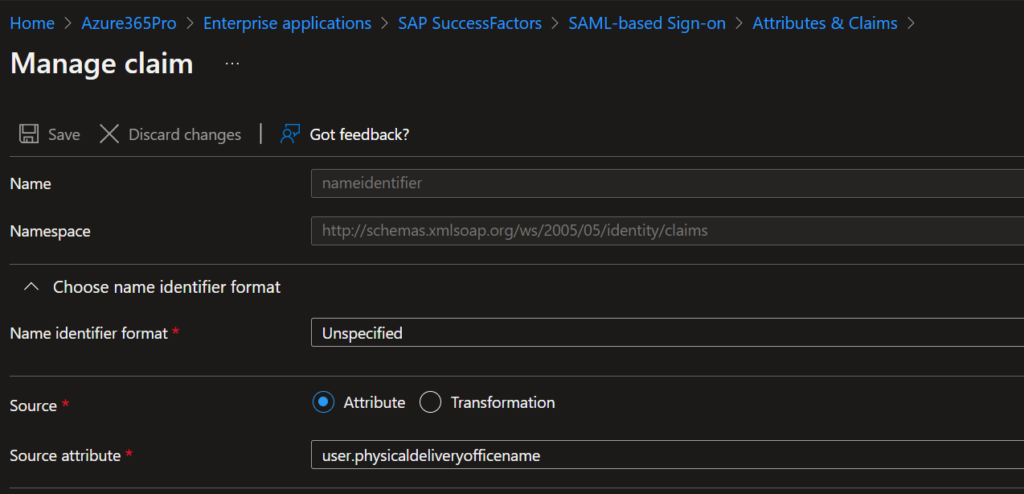
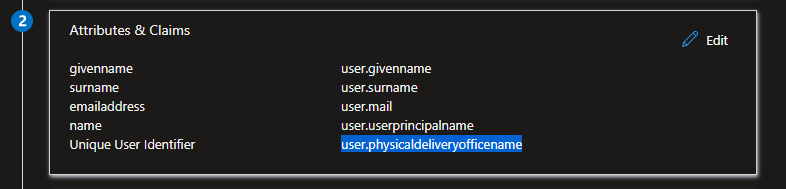
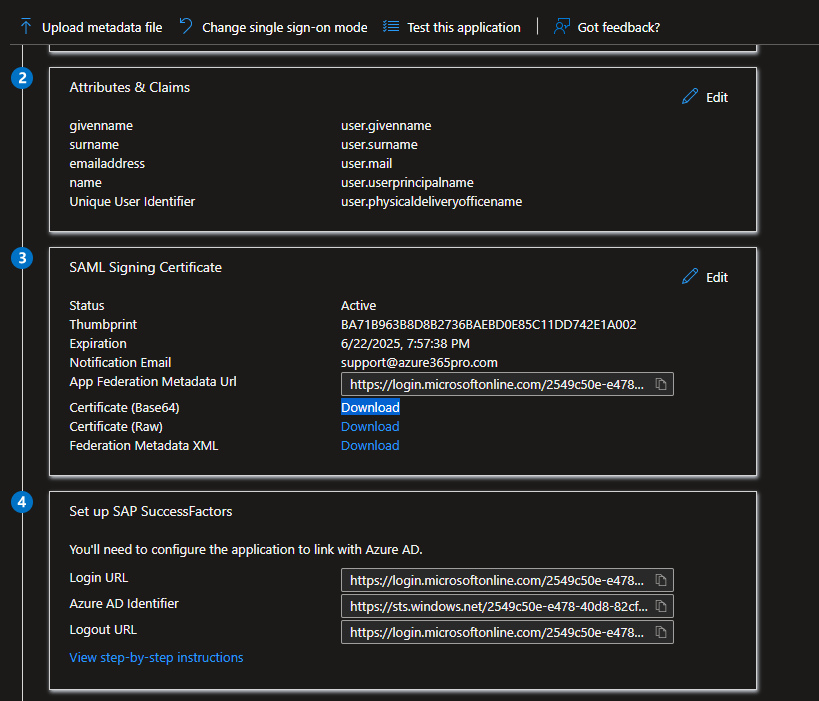
Changed my unique Name Identified to physical delivery office name as employee ID is stored in this particular attribute
Please note Destination (SAP Success Factore is Configured with Employee ID as username) as you may see most of the SAP Systems are configured with employee ID as user name.
Certificate (Base64) / Login URL / Azure AD Identifier / Logout URL can be used on SAP Success Factor
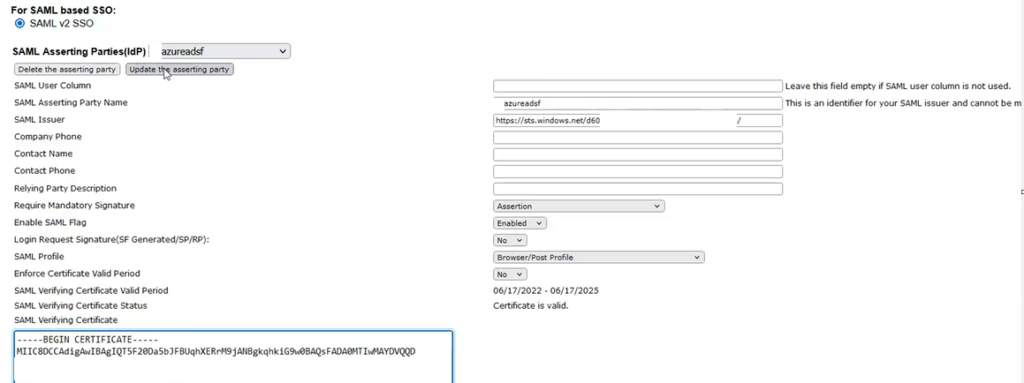
Configure SAP Success Factor in Provisioning Mode to enable Single Sign-on in your instance.
- Configure SAML Asserting Party Name
- SAML Issuer
- Require Mandatory Signature
- Enable SAML Flag
- Login Request Signature (SF Generated/SP/RP)
- SAML Profile
- Enforce Certificate Valid Period
- SAML Verifying Certificate
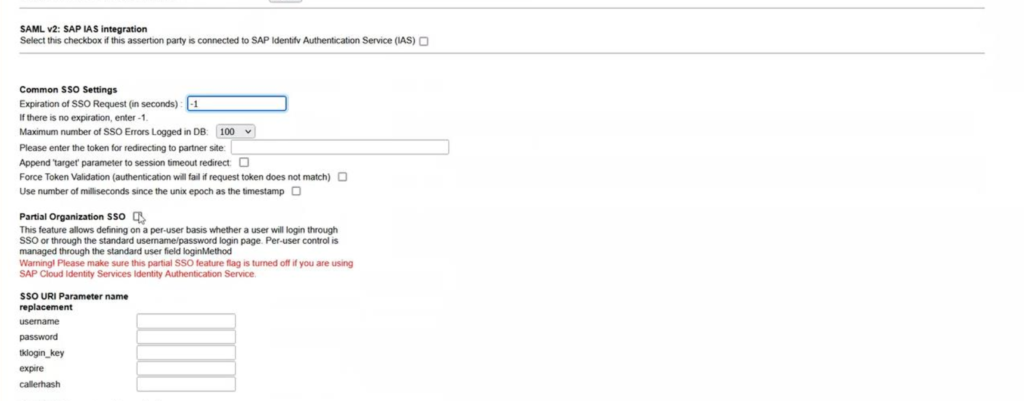
Expiration of SSO Request
Enable Partial Organization SSO – Until you thoroughly test the Single Sign ON with Azure Active Directory.
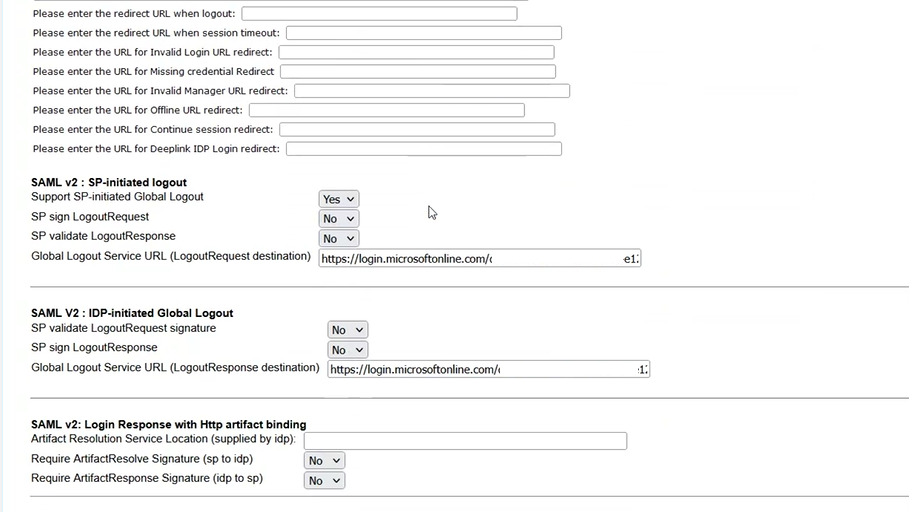
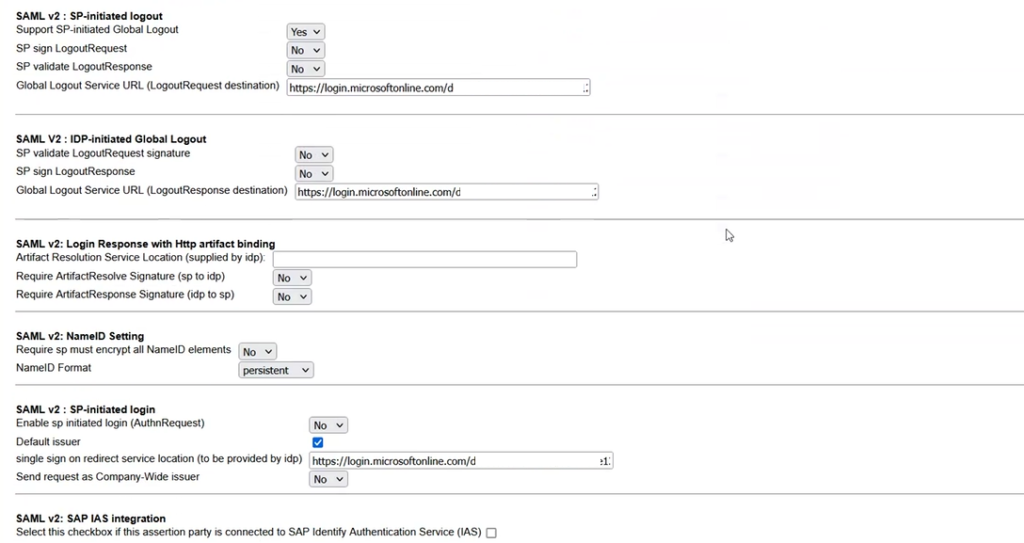
Configure SP-Initiated Logout
Configure IDP-Initiated Global Logout
Configure NameID Setting to Persistent
Configure SP-Initiated Login
Once users are assigned to Azure AD Success Factore App – Single Signon started working seamlessly between the systems.


